A group of security researchers and computer scientists have recently uncovered a vulnerability in how a Diffie-Hellman key exchange is deployed on the web.
Dubbed as Logjam, the vulnerability affects home users and corporations alike, and over 80,000 of the top one million domains worldwide were found to be vulnerable. The original report on Logjam can be found here.
What is Diffie Hellman? Diffie-Hellman is used to establish session keys that are a shared secret between two communicating parties. Protocols like SSH (used for secure shell access) or TLS (a common protocol used to secure data on the web) can implement Diffie-Hellman session keys in order to transport data securely.
Common examples of where Diffie-Hellman may be used include securing bank transactions, e-mail communication, and VPN connections, just to name a few.
What did the researchers discover? Unfortunately, many implementations of Diffie-Hellman on web servers use weaker parameters.
The researchers behind the Logjam attack found these web servers to be vulnerable, allowing an attacker to read or alter data on a secure connection. According to their report:
We identify a new attack on TLS, in which a man-in-the-middle attacker can downgrade a connection to export-grade cryptography. This attack is reminiscent of the FREAK attack [6], but applies to the ephemeral Diffie-Hellman ciphersuites and is a TLS protocol flaw rather than an implementation vulnerability
While much of the research is performed against a Diffie-Hellman 512-bit key group, the researchers behind the Logjam discovery also speculate that 1024-bit groups could be vulnerable to those with “nation-state” resources, making a suggestion that groups like the NSA might have already accomplished this. A comprehensive look at all of their research can be found here.
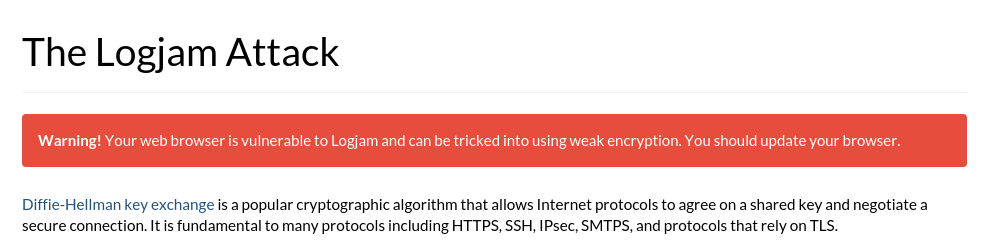
This all sounds great. What do I need to do? You can use the link above to discover if your browser is vulnerable. If it is, you should see an image like the one below:
At the time of this writing, patches are still in works for all the major web browsers, including Chrome, Firefox, Safari, and Internet Explorer. They should be released in the next day or two, so ensure your browser updates correctly once its released. These updates should reject Diffie-Hellman key lengths that are less that 1024-bits.
In the meantime, you may want to use a Virtual Machine and avoid entering sensitive information into website forms.
For those running web servers that implement Diffie-Hellman, make sure the key group is 1024-bit or larger. There is also a help page that can be found here.










