A few years ago, cybersecurity scryers predicted that the video gaming industry would be the next big target of cybercriminals. Whether this will come true in the future or not, the average gamer may have little to no idea of what awaits them, much less be prepared for it.
In fact, while generally more technically adept than the average Joe, most gamers lack familiarity with risks they could encounter while gaming or browsing the web for game-related content. For the majority of US households, this takes place on devices such as the personal computer, smartphone, and the dedicated gaming console.
Factoring in the gaming industry’s steady growth since 2011—the changes in consumer gaming perception, habits, and appetite for new content, tech, and accessories—and the expectation that, despite a foreseen nominal dip, the industry will still hit high marks on sales at end of year, it is more crucial than ever to educate gamers on cybersecurity best practices. This includes the various threats gamers may encounter online, their real-world consequences, and what they can do to protect themselves.
While a lot has changed in the gaming industry in the last five years, most of the tried-and-tested tactics of ensnaring the unfamiliar (and oftentimes, the experienced) are still around, causing panic and making headlines.
So, without further ado, here are the risks every gamer—on a PC, mobile, or gaming console—should keep an eye out for.
Malware and potentially unwanted programs (PUPs)
Malware and PUPs have been the top-of-mind threats to online gamers, and for a good reason. They come in many, many forms—key generators; game cracks; trainers; fake mobile game apps [1][2], game installers, clients/launchers, and audio protocol; game hacks; cheat files [1][2]; infected or risky mods; unofficial game patches; bogus emulators—you name it. At this point, it won’t be a surprise to consider that every conceivable software related to gaming might have a malicious equivalent in the wild.
Malware doesn’t only appear as applications, but can also be embedded in image files. In 2016, cybercriminals were found to have hidden a Trojan in image files in over 60 Android apps using stenography. Perhaps even more surprising, cryptomining code was included in Abstractism, a platform that was once peddled in Steam and was eventually pulled from the market after a flood of complaints.
Malicious binaries can also exploit software vulnerabilities, the way the TeslaCrypt ransomware did when, with the aid of several known exploit kits, it took advantage of unpatched Adobe Flash Player programs.
Lastly, malware can affect gamers when they connect to infected servers. In the report, Study of the Belonard Trojan, exploiting zero-day vulnerabilities in Counter-Strike 1.6, security experts at Russian antivirus firm Doctor Web investigated Belonard, a Trojan that takes advantage of weaknesses in both Steam and pirated versions of Counter-Strike 1.6 (CS 1.6).
Once infected with Belonard, gamers are then made part of a botnet, which can further propagate the promotion and marketing of other potentially malicious servers.
Survey scams
We sometimes wonder how a tactic this old can stick around for so long, and we find the answer in a longstanding phishing truism: It works.
Survey scammers immediately jumped on the Far Cry 5 craze by offering “free” copies of the game after it was released in Q2 2018. Unbeknownst to users who are led more by their desire to get a free Triple-A title game than to protect their data, they sign up to a service that purports to offer “unlimited movies,” but end up giving away their email addresses, receive even more offers they don’t want, and realize in the end that they didn’t get any of what was offered to them.
A similar flocking happened when Grand Theft Auto 5 (GTA V) came out in Q3 2017. Many scammers used YouTube to market their so-called money generators, which are survey scams, to nudge gamers to give away their personally identifiable information (PII) or download a potentially malicious file.
Let’s also not forget the amount of scammery that went down when Pokemon Go reached peak hype.
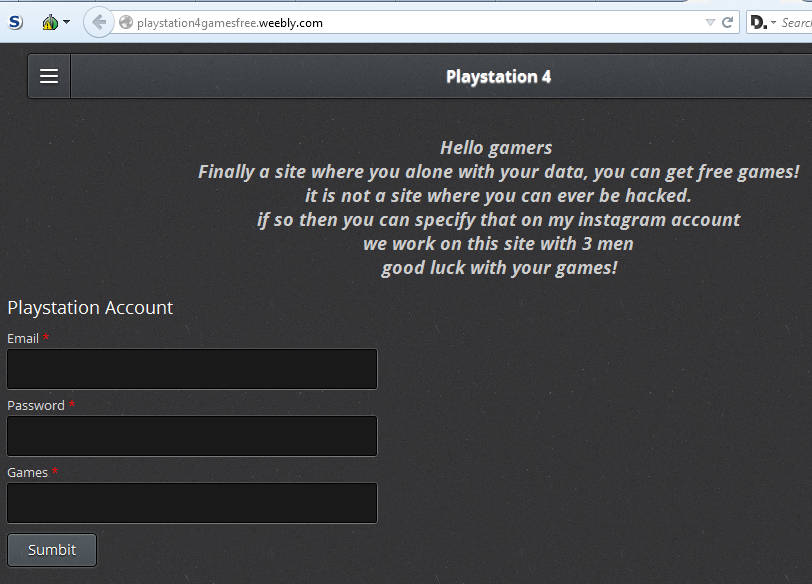
Phishing scams
Steam users are probably more than familiar with the times when phishers used squatted domains to lure them into giving out their credentials to Steam or their favorite third-party trading site, like CS:GO Lounge.
sleamcummunity.com and
steamcornmunity.comSimilarly, a fake CS:GO Lounge domain was registered and mimicked the real trading and bidding site. Criminals behind it were also after Steam credentials. To rub salt to the wound, they even added a Trojan that pretended to be a Steam activation file.
Account takeover (ATO)
An account takeover is the result of credential fraud caused by phishing, hacking, or a data breach. Anyone maintaining an account online is at risk.
Ubisoft, the company behind Assassin’s Creed and the Tom Clancy brand, was compromised in 2013. While the company was mum about how it happened, one of our experts hinted that an employee may have been spear-phished, allowing the criminals to gain access to their internal network. Ubisoft prompted its users to quickly change their passwords.
Employees aren’t the only likely targets of those with nefarious intentions. Game developer’s forums are also at risk. Bohemia Interactive’s DayZ had theirs compromised, with hackers accessing and downloading usernames, passwords, and email addresses.
Ad flooding and malvertising
Ads, whether showcased on websites or apps, are perceived as more of an annoyance than a threat by normal users. But when they become too aggressive, Malwarebytes characterizes them as adware.
Mobile users who enjoy playing free games can probably attest that they can tolerate ads—they’re usually not in the way of the game they’re playing anyway. But if ads are more prevalent than the actual game, then expect to hear users complain. A lot.
Of course, some ads also contain malvertising, which opens up the angle that ads can be used as infection vectors to reach users who aren’t usually bothered by them.
Cyberbullying
Not all threats video gamers encounter online are after their information or their money. Some are after them, their reputation, their peace of mind. We implore every gamer to be wary of the items below as much as the items above because they can cause mental and emotional damage, rather than financial.
According to the US Department of Health and Human Services, the division that maintains the stopbullying.gov website, online bullying includes flaming, harassment, exclusion, denigration, outing/shaming caused by deception or pretension, and doxing. Nude photo sharing or revenge porn can also be considered a form of cyberbullying.
Cyberbullying can happen to gamers while interacting online, whether that’s using voice features of multiplayer games, or in forums or other chat functions of gaming platforms.
We’ve covered the topic of cyberbullying on several occasions, especially during events like the National Cybersecurity Awareness Month (NCSAM). We shared tech that could help curb cyberbullying, statistics on online bullying trends, and demystified the myths surrounding this act. It pays to go back and read these posts.
Trolling/griefing
Trolling could be both fun and funny. At least at first. But after the raucous laughter dies down to a chuckle, gamers eventually decide to get serious and carry.
Except they can’t.
Because sometimes that troll continues to stand in the open doorway doing jumping jacks, preventing gamers from going to the next room and advancing in gameplay.
This was what happened after Ubisoft officially released Tom Clancy’s The Division.
On the other hand, griefing—the term used to bring grief onto players by ruining their overall experience—is not lost in Elite Dangerous, a space exploration simulation. For one of its players, Commander DoveEnigma13, the end game is to reach a distant star system called Colonia. It may be his last chance to make the trip, as he had been battling a terminal illness for at least three years. So, with other Elite players, his daughter, and Frontier (the game developers) helping make this voyage a success, the Enigma Expedition was born.
However, reports of other Elite Dangerous griefers were sabotaging the expedition by attacking the final waypoint, a mega-ship called Dove Enigma, which Frontier also created as homage for the Commander. Without this, it would be difficult for the Enigma fleet of 560+ players strong to reach Colonia due to fuel shortage. However, in an interview with the Polygon, one of the players who was part of the fleet said that “the threat is minor at best.”
Read: When trolls come in a three-piece suit
Stalking
Thanks to Pokemon Go, augmented reality (AR) has become part of the modern gamer’s vocabulary. It’s the future of interactive and immersive gaming, bringing the experience to new heights. Unfortunately for some, AR games like Ingress have also made a way for gamers with questionable intent to use unofficial tools to stalk other gamers, visit their real-life homes, and leave creepy messages on doorsteps for the homeowners to see.
Intoku, an Ingress gamer, admitted to Kotaku in an interview: “Players on both sides have stalked and been stalked.” With a game that is based around real-world locations, players shouldn’t be surprised, nor should they expect little or no risk when playing such games.
Swatting
Swatting might start off as a prank call to emergency services, but the results—a dispatch of a large number of armed police officers to a particular address—can quickly become deadly, as we’ve seen in the Andrew Finch case. And yet, Peter “Rolly Ranchers” Varady, a then 12-year old YouTube streamer, was swatted less than a month after Finch’s death. This happened days after Cizzorz, a renowned YouTube streamer with millions of subscribers, helped him dramatically increase his subscriber count from 400 to almost 100,000.
In another story, a gamer with the pseudonym “Obnoxious” used swatting to get back at mostly young and female gamers who ignored or declined his friend requests on League of Legends (LoL).
In response to numerous swatting stories, some local US law enforcement agencies offer an anti-swatting service to video gamers and YouTubers.
Grooming
Probably the worst risk young gamers can encounter online is grooming, which is when a pedophile prepares a child for a meeting with the intention of committing a sexual offense. Not only is grooming a targeted act, but it’s also premeditated. Sometimes, it can be stopped if a parent happens to be in the same room as their child, or law enforcement is already tailing a suspect. Other times, it can lead to tragedy beyond words.
Breck Bednar was 14-years-old when he met Lewis Daynes online. Daynes was the ringmaster of the “virtual clubhouse” where Bednar and his friends at school would hang out. He claimed to be a computer engineer running a multimillion pound company. Daynes groomed Bednar into tricking his parents in order to arrange a meeting. He invited Bednar to his flat in Essex one Sunday in February 2014. Bednar texted his father that he’d be spending the night at a friend’s (who wasn’t Daynes). That was the last time they spoke.
There’s another side of grooming that is built around the highly popular game, Fortnite: the cybercrime kind. According to the BBC, teenagers as young as 14 admit to stealing private gaming accounts and reselling them online. Experts say that organized crime is linked to these activities, and that cybercrime grooming is taking place behind the scenes by dangerous persons or groups.
Play it safe. Always.
With a myriad of risks in online gaming, from financial to physical, it’s especially important to adhere to cybersecurity best practices. The gaming community is active, engaged, and passionate—and criminals will take advantage of that to the best of their ability. Head them off at the pass by following our advice:
- Explore your options. Regardless of your gaming platform, it always pays to know how it works. Since a lot of PC-based games use launchers, acquaint yourself with their settings and customize them with security and privacy in mind.
- Take advantage of additional security and privacy options when available. These launchers may have some form of two-factor authentication (2FA) to ensure that a user who asserts they own the account can verify this claim easily.
- Update all software installed on your gaming rig or, if you’re a console gamer, the firmware and the games installed in it.
- Always treat links sent your way—either by someone you’ve known for a long time or by someone you just met—as suspect. Because of the number of ways gaming accounts can be taken over by miscreants—and most of the time, victimized gamers are not aware of this—it’s wise to handle links with caution. It would be easier if you have other means to contact the link sender other than the gaming platform to verify that indeed it was them who messaged you. Ideally, if you and your friends and family members play games to bond, establish amongst yourselves a verification process, like a keyword/phrase you can mention or type up in chat. Not saying the keyword/phrase can denote that you’re not talking to the person they claim to be.
- Use a form of password management that works for you. We know it causes fatigue just to remember all those username and password combinations. Based on some comments we’ve received on the Malwarebytes Labs blog, we also know that not everyone is using password managers, but instead have created their own way of managing and storing passwords. Go with what works, as long as your passwords are kept safe and secure. Most of all, avoid reusing passwords.
- Manage your gaming profiles. These days, gaming profiles should be treated the way a regular social media profile and feed should be. Don’t reveal information about yourself that is deemed sensitive. You can pick and choose who sees your gaming activities and who doesn’t. Use your options wisely.
- Keep your shields up. If suspicious files claim they can help you in your gaming, but you must first disable your antivirus or turn off your firewall, that’s a major red flag. If a piece of software wants to have free rein in your system without your security protections on, you better find safer alternatives.
- Play games in the presence of or within earshot of your parents/carer. Grown-ups living with minors who are into gaming are always advised to get involved this way. They don’t have to breathe down their children’s necks, but they should at least pop in from time to time and make sure nothing nefarious is taking place—whether that’s the content of the game itself or the conversations happening amongst players.
Game over
We can say with confidence that many of the risks to online gamers a few years ago are still the risks they face today. Although nowadays, news of gamers behaving badly toward other gamers are at equal footing with news about malware and online criminals targeting gamers. Because of the real-world and life-changing impact they present to people behind the avatars—and to their families and loved ones—more is at stake now than just playing along in a computer-generated world. Gamers are not only called to take cybersecurity seriously, but they’re also called to be responsible digital citizens.
Playing video games is meant to be fun; a way for us to relax, blow off steam, and de-stress. However, let’s also recognize that gaming is already part of the overall threat landscape. Make sure that your information—and your person—are safe from harm in the digital world and beyond.
Game on!