The FBI has issued a Private Industry Notification (PIN) about cybercriminal actors targeting the food and agriculture sector with ransomware attacks.
Farms are literally the first step in one of the most important, if not the most important, supply chain in our economy: The food supply chain. As always, cybercriminals love the extra leverage that is provided by how important a target is.
Ransomware attacks targeting the food and agriculture sector disrupt operations, cause financial loss, and negatively impact the food supply chain. Food and agriculture businesses victimized by ransomware suffer significant financial loss from ransom payments, loss of productivity, and the (often neglected) cost of remediation. And, as the FBI points out, no operation is too big, or too small, to be a target:
Larger businesses are targeted based on their perceived ability to pay higher ransom demands, while smaller entities may be seen as soft targets, particularly those in the earlier stages of digitizing their processes…
The FBI also warns that ransomware can carry a cost in lost data: “Companies may also experience the loss of proprietary information and personally identifiable information (PII) and may suffer reputational damage resulting from a ransomware attack.”
Internet of Things
Agriculture may not be the first industry you associate with cybersecurity problems, but we all need to be aware of the risks created by connecting this ancient part of our food supply chain to the Internet. As farms have grown in scale they have increased their level of automation, making farms and farm equipment Internet-connected cogs in the of the Internet of Things “machine”. This comes at the cost of a significant increase of their attack surface.
The state of IoT is poor enough as it is, security wise. But manufacturers of agricultural equipment have spent the last few years locked in an automation arms race, and the side effects of this race are starting to show. In any industry that is developing and adopting new technology at pace you can expect growing pains and security is often the last thing on the developers’ minds. So it is with agriculture.
In our most recent Lock and Code podcast, Malwarebytes Labs’ David Ruiz spoke to hacker Sick Codes, whose research into cybersecurity in agriculture has been instrumental in raising its profile this year.
In it, he told us that the industry is starting to take security seriously, but it is still grappling with the basics, leaving it dangerously exposed. Speaking about his research into John Deere and another agricultural equipment manufacturers, he gave us an example of what he found, in plain terms:
A group of less than 10 people were able to pretty much get root [the highest level of access] on John Deere’s Operations Center, which connects to every other third party connectivity service that they have. You know, you can get every farms’ data, every farms’ water, I’m talking everything. We had like the keys to the kingdom. And that was just a few people in two days.
Rise in malware
Sick Codes and the FBI aren’t the only ones to notice that something is up in agriculture. As we pointed out in our State of Malware report, published earlier this year, Malwarebytes recorded an eye-watering 607% increase in malware detections in the agriculture sector in 2020.
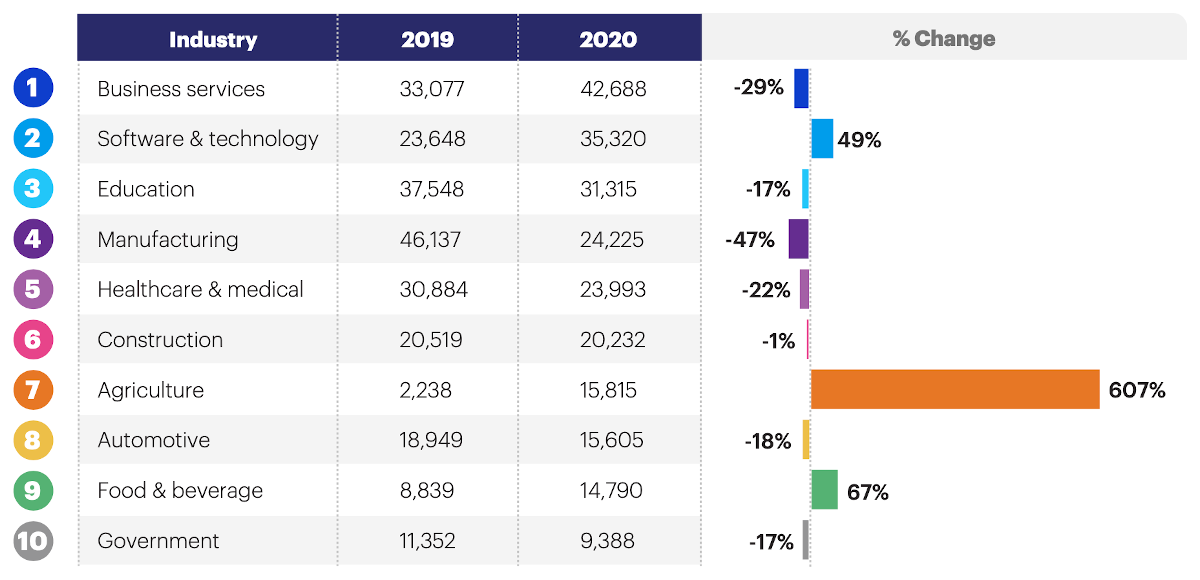
As the manufacturing and automotive sectors contracted in 2020, under the weight of pandemic shutdowns, attackers simply turned their faces to other industries, with agriculture by far the biggest loser.
Critical infrastructure
While the FBI’s warning focusses on the threat to individual operators, the rapid computerization of agriculture also carries potential risks for the system of food production itself.
Connectivity and centralization could create opportunities for threat actors—state sponsored or otherwise—to throw a wrench in the workings of our critical infrastructure. Attackers could potentially provide false data to farming equipment, change the temperature in greenhouses, alter the composition of fertilizers, or bring businesses to a crashing halt by deploying ransomware. All of which could lead to shortages and increased food costs.
Recommended mitigations
The agriculture sector needs to be as prepared as any other sector to withstand attacks by cybercriminals. But the sector is only as secure as the technology it relies on, so our food supply requires secure IoT devices and Cloud services for food and agriculture too.
The FBI notice includes the following recommendations:
- Regularly back up data, air gap, and password protect backup copies offline. Ensure copies of critical data are not accessible for modification or deletion from the system where the data resides.
- Implement network segmentation.
- Implement a recovery plan to maintain and retain multiple copies of sensitive or proprietary data and servers in a physically separate, segmented, secure location (i.e., hard drive, storage device, the cloud).
- Install updates/patch operating systems, software, and firmware as soon as they are released.
- Use multi-factor authentication with strong pass phrases where possible.
- Use strong passwords and regularly change passwords to network systems and accounts, implementing the shortest acceptable timeframe for password changes. Avoid reusing passwords for multiple accounts.
- Disable unused remote access/RDP ports and monitor remote access/RDP logs.
- Require administrator credentials to install software.
- Audit user accounts with administrative privileges and configure access controls with least privilege in mind.
- Install and regularly update anti-virus and anti-malware software on all hosts.
- Only use secure networks and avoid using public Wi-Fi networks. Consider installing and using a VPN.
- Consider adding an email banner to messages coming from outside your organizations.
- Disable hyperlinks in received emails.
- Focus on cyber security awareness and training. Regularly provide users with training on information security principles and techniques as well as overall emerging cybersecurity risks and vulnerabilities.
To learn more about the current state of cybersecurity in the Internet-connected world of agriculture, you can listen to our Lock and Code podcast below:











