Sometimes the narrative direction your blog post is going to take does a 180, and then spins around a few more times for good measure.
When we saw what appeared to be a fake OWA portal asking for username and password info, we were interested.
When we saw the same site offering up an executable file after handing over credentials, we were even more interested.
But then Steve the Employee happened.
At this point, the narrative direction is quite clearly “Fake OWA site harvests credentials”. However, that isn’t what is going on here.
We’re big fans of training up staff to be more security aware, and it is most definitely a pressing concern for businesses wanting to avoid data theft and malware attacks.
Businesses will often hire independent security firms to conduct tests on their network – and occasionally, their employees. They may set up a fake phishing page and track clicks on links, or email files around the office from a “trusted source” and see if anybody opens it up.
By doing this, an organisation can see where potential weak spots lie and address it appropriately.
It seems one such company was performing a security test, and one of the employees of this business entity – did we call him Steve yet? – was so sufficiently versed in the art of “Not clicking on things” that he went the extra mile, submitting this fake email portal to a public clearinghouse of potentially rogue URLs.
At this point, the submission would be seen by researchers such as myself who would then set about analysing the content, files and anything else particularly eye-catching.
We would then go off and write a blog warning readers about the dangers of malware-laden websites, phishing emails and the occasional pair of binoculars. Let’s take a look and see what may have confronted Steve on his dark night of the soul.
The site certainly looks suspicious to the trained eye – there’s no HTTPs in the URL bar for starters, but is asking for login credentials? Uh oh. Steve! Save yourself!
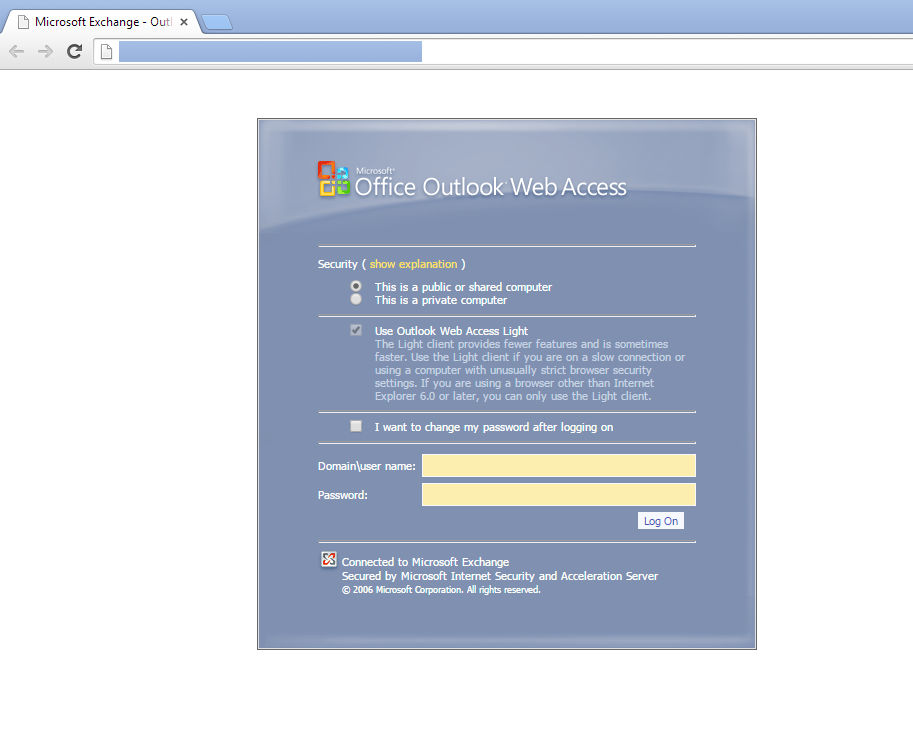
The site is registered via an anonymity service located in Panama. As Steve can attest, your organisation probably doesn’t roll like that.
After logging in, the site offers up an executable file because an “update is required” to access the application.
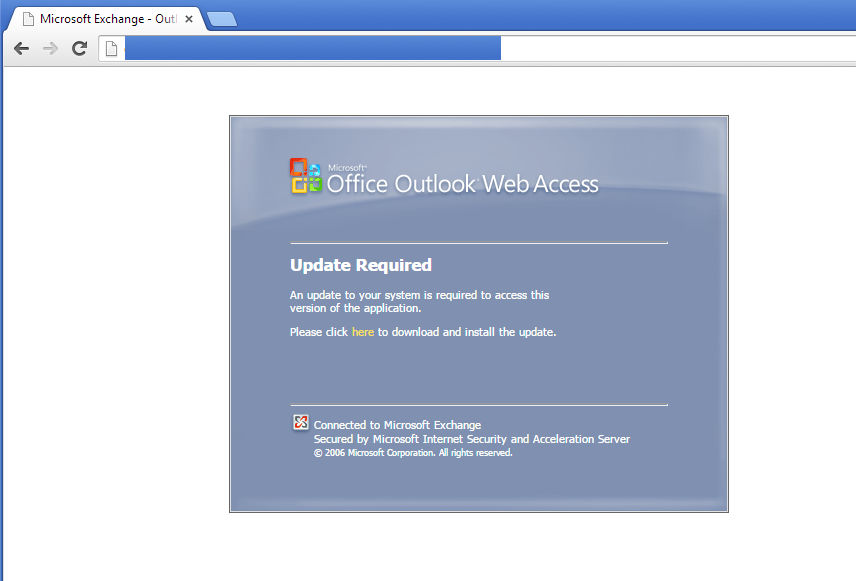
What could possibly go wrong! We cannot confirm or deny that Steve hurled himself in slow motion across a nearby table to prevent a colleague taking the bait.
Network analysis reveals that the executable makes callbacks to a domain used by a company dealing in penetration / security / social engineering tests. Looking at the code deepens the connection to said firm.
When tests such as these are set up, the best expectation you can probably hope for is that an employee chooses not to click a link or run a file.
To go above and beyond the call of duty and start submitting sites and files to phishing link clearing houses probably deserves a bonus, or at least half a day off.
It probably wasn’t something anybody involved in the testing was expecting, but unexpected happenings are what security is all about.
So hey, move along and nothing to see here. All hail Steve – pretty sure we called him Steve – Employee of the Month, and most definitely not clicking on any of your weird email links.
Christopher Boyd










