At hpHosts, Malwarebytes’s trusted blacklist of malicious sites, we also receive tip-offs or reports from users about one or two dodgy URLs they may have encountered while surfing the Web on top of those our engineers gather themselves.
The latest tip we received recently was on a fake The North Face website. As per Hosts‘s classification, it’s filed under FSA, meaning it’s a site “engaged in the selling or distribution of bogus or fraudulent applications and/or provision of fraudulent services.” It’s located at thenorthfaceoutlet(dot)in(dot)net, with the following screenshot of the default page below:
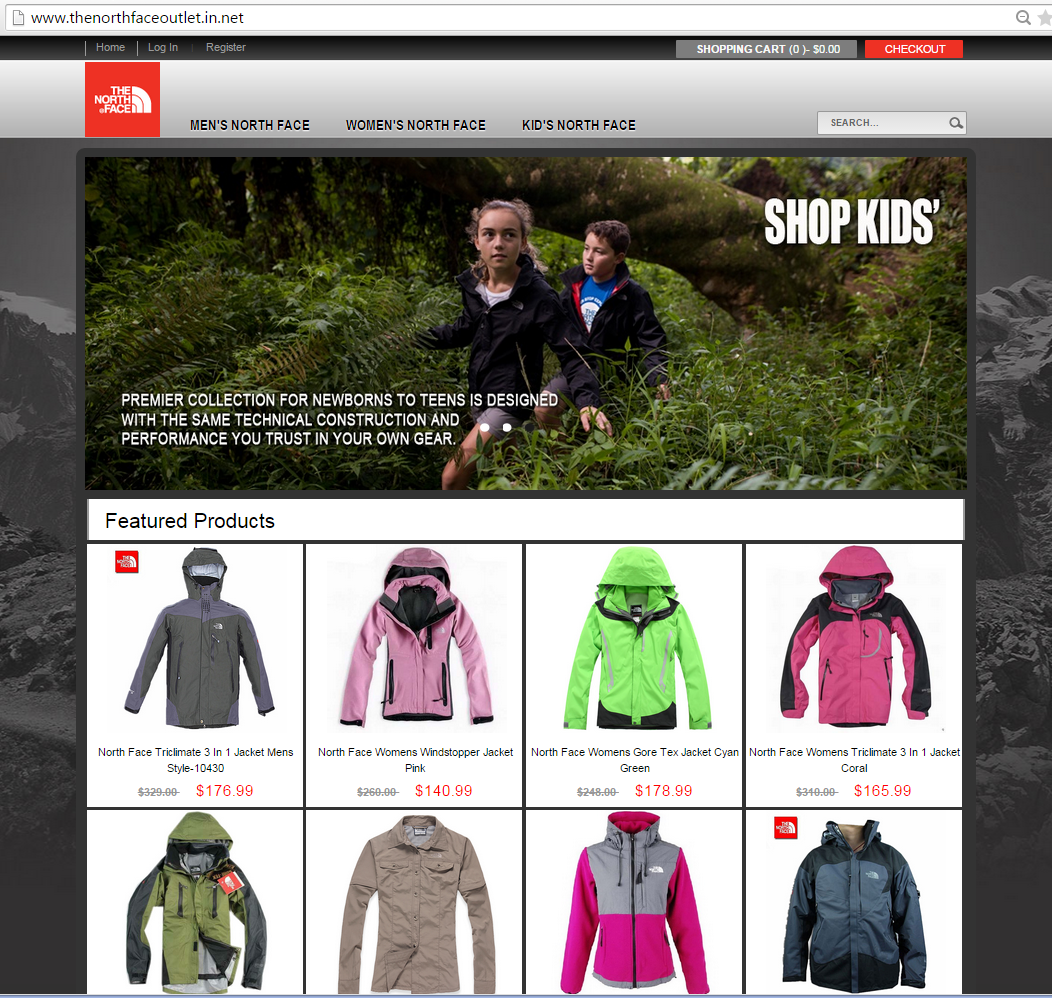
(click to enlarge)
Majority of sites, such as the above, offer counterfeit products which are shipped from China. Some just charge the unwary visitor but have no intention of shipping the product. Some still include JavaScript code onto their domains that security sites deem malicious.
Regular users, on the other hand, may class thenorthfaceoutlet(dot)in(dot)net, and others like it, as simply scam or even phishing campaigns. The former, we can readily prove here in this post; the latter, I’m afraid, takes more than just conjecture.
The Skinny
We dug deeper into the case of this particular fake The North Face site. Below are our observations based on its whois data and generally what’s on the site:
- The email address used to register the domain is from @163.com, a popular Chinese Web portal operated by NetEase, Inc. It was also used to register multiple domains
- The domain is hardly four months old.
- Although the domain’s IP is said to be hosted in Singapore, the personally identifiable information (PII) used to register thenorthfaceoutlet(dot)in(dot)net are someone from the US. We reckon that whoever was really behind the site scraped information they needed from publicly-available sources online, such as free people search engines.
- We have observed that its purported support email, onlineservice_001@live.com, has been associated with other equally dodgy domains that are selling products of big names such as Michael Kors, Louis Vitton, Ralph Polo Lauren and others.
- The site listed a US Head Office address that actually belonged to Barbour, another clothing brand.
- In order for would-be buyers to make a purchase on the site, it requires them to register. They ask for login, payment, address, and contact details.
- This counterfeit site’s URL, along with others like it that we’ve seen, shows no signs of typo-squatting.
- This site also uses decent resolution of photos, further removing the hint of phoniness about it.
During our research, it’s no surprise to see that there are more URLs similar to the fake The North Face site we’re discussing here—more than 50 in our count, at least.
There were probably more campaigns that have gone down these past few months and being created as we speak.
A recent APWG global phishing survey (PDF) published revealed more phishers in China are registering domains due to dropping prices.
APWG believed this will attract more bad actors into setting up their own sites, regardless of their malicious purpose: phishing, distribution of malware, and, yes, even establishment of domains selling counterfeit products. Below are screenshots of the eight out of the 50+ sites on our list that are still online, as of this writing:
The Means
At some point, these campaigns have to be “marketed” somewhere. Unfortunately for us, most if not all of these sites have excellent SEO scores that may rival their legitimate counterparts. That alone may up the chances of users unfamiliar of a brand’s official URL to go to search engines for help.
Another tactic the bad guys rely on is, of course, spam:

(click to enlarge)
What you see above is a carpet bomb of links posted on a legitimate website about London. We’ve see more posted on comments sections and guest book entries of actual donation pages, travel sites, eSports sites, and tribute pages.
Probably unrelated to the dubious site above, but we’ve also came across complaints about certain Facebook users having an online yard sale, enticing people to buy their affordable, slightly used knock-offs.
The Counter
We’re pleased to see that The North Face redirects URLs selling counterfeit products to the IP 167.64.243.157, which actually shows a Notice to Consumers graphic, informing them that the site they’re attempting to visit is actually is wrong and points them to the correct destinations instead. Screenshot below:
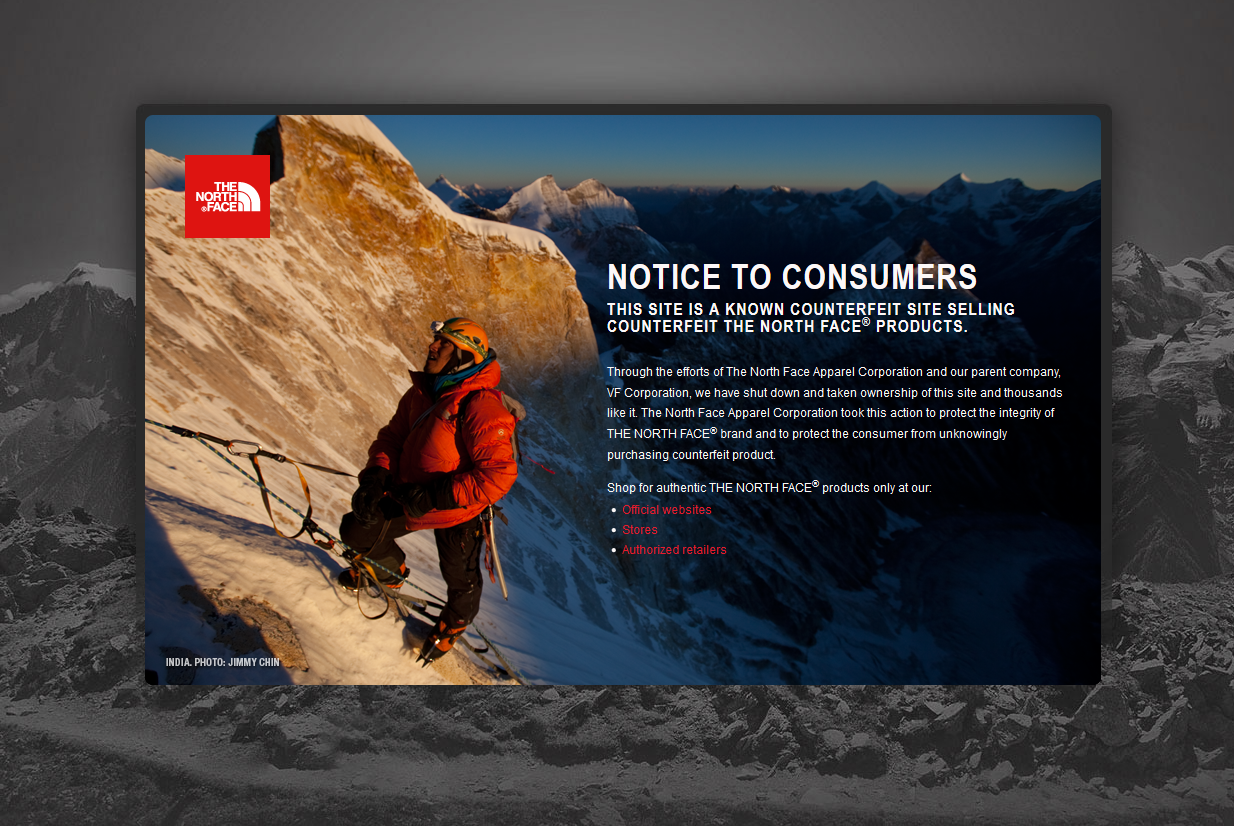
(click to enlarge)
Although not all of the bad sites redirect this way, which is no vendor’s fault, we still think it’s a decent way to educate users and to curb the number of potential victims of these fake sites.
The best way to combat counterfeiters is to report them, either to the official channels of the brand being mimicked, to a blacklist site like hpHosts, which also reports to proper authorities, or to your favorite AV vendor.
Most (if not all) AV software now have built-in Web protection solutions that block malicious sites and unwanted redirects as long as they’re in their blacklist. Keep that in mind.
Other steps users may take to protect themselves are as follows:
- Bookmark online stores you frequent, removing the need of memorizing their URLs.
- When buying online, it’s more advantageous to use your credit card instead of your debit card. Most credit card companies already have insurance or a chargeback scheme in place while banks that issue debit cards have yet to emulate this.
- Keep your AV software updated.
- When you enter information to a site, make sure that it is secure first. How to tell if a site is secure? The URL should start with “https://”, with the operative letter being the “s”. If it’s not there, avoid entering your information.
Other related post(s):











