We are not sure if this is going to be a new trend among browser hijackers, but it seems more than a coincidence that we found two browser hijackers using a very similar approach to reach their goal of taking victims to the sites of their choice. Both are using one of their own files to act as a file-in-the-middle between the user and the browser. Let’s compare them.
Dotdo Audio
Dotdo is a strain of hijackers that we have discussed before for using different and more “out of bounds” methods to get the job done. I named this variant “audio” because it uses audio advertisements. But that is not our focus here. It’s the replacement of browser executables with their own that raised our interest. The installer renames the files firefox.exe and chrome.exe, if present, and adds a number to the filename. It then hides these renamed files and replaces them with its own files.
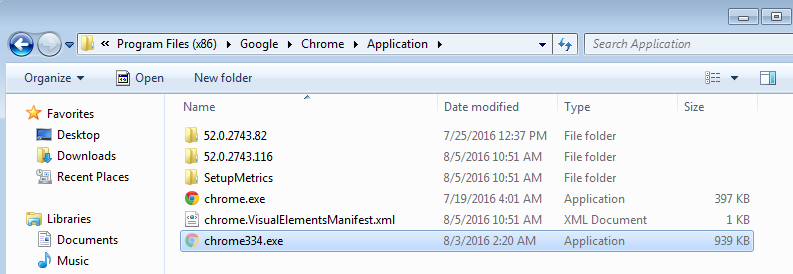
The screenshot above shows you the hidden and renamed Chrome file, in the same folder as the replacement. I changed the settings for hidden files so that we can see them.
In a similar screenshot below we can see that the same was done for Firefox.
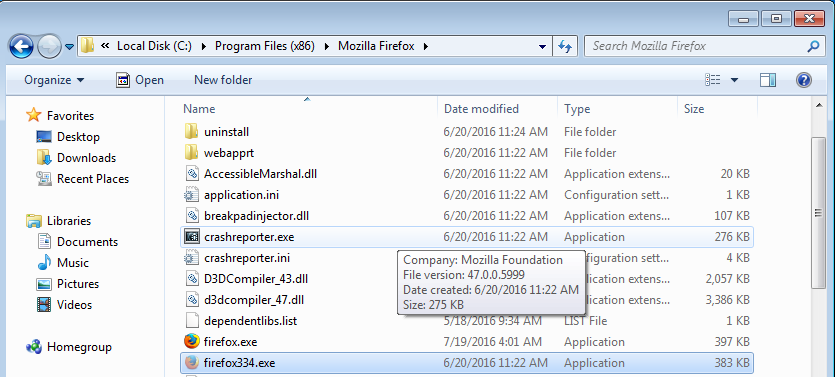
Note that all the changes are misdated, they were all made 8/10/2016.
For the hijacker using the method of replacing files this has the advantage that they don’t have to follow the more common method of altering shortcuts. All the shortcuts the user has on his desktop, startmenu, taskbar, and anywhere else, can stay the same as the folder and filename they are pointing to are still valid and now under control of the hijacker. Then, when the false browser is started the hijacker will trigger the renamed chrome.exe and add some extra instructions.
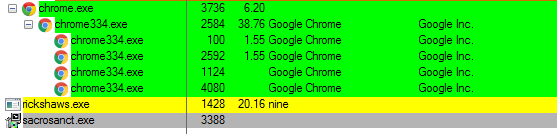
As a result the victim will be able to surf as he expected and probably ask himself where the audio advertisements are coming from. HPRewriter2
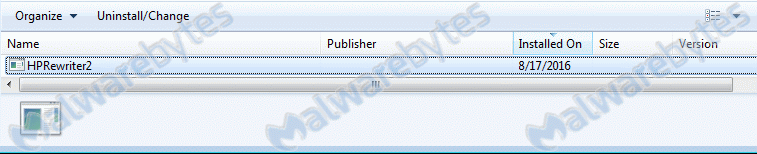
This one was named after the entry it makes in the list of installed Programs and Features.
The browsers are hijacked to open with traffic-media[dot]co by altering the browser shortcuts for:
- Chrome
- Firefox
- Internet Explorer
- Opera
- Yandex
The target of the shortcuts is altered to C:Users{username}AppDataRoamingHPRewriter2RewRun3.exe {version number} as shown in the example below.
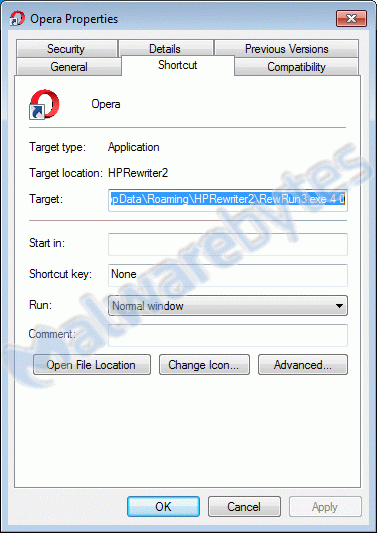
Triggering Rewrun3.exe without a version number accomplishes nothing (it will not run), but with the version number forwarded by the shortcuts, Rewrun3 opens the targeted browser with the traffic-media[dot]co site or one of their redirects.
Summary
We discussed two hijackers from very different families and using different methods, but they also had a few things in common. They want the victims to hear/see their advertisements and they used a file-in-the-middle between the browser shortcuts and the actual browser in order to alter the browsers behavior to meet their goals.
Additional information
File properties:
Dotdo hijack installer SHA1: 0d16eae1f5748410fa047daa533d0ebbd994ea1c
Firefox.exe (fake) SHA1: 53a77f64595b1fb65a88247a324458f569e3d12a
Chrome.exe (fake) SHA1: 501c9a6b224f58773b603675a71624d7e7353d1f
HPRewriter2 installer SHA1: f96399f3b91218f30a9e58fce8009eaab5521398
Rewrun3.exe SHA1: 117db3909a2507e162a6361be1f4e5950f017e7d
Removal guides:
Protection and detection
Because of the intrusive changes the Dotdo installer makes it was classified as a Trojan. The resulting changes to the system are detected and removed as PUP.Optional.DotDo and PUP.Optional.MultiPlug.
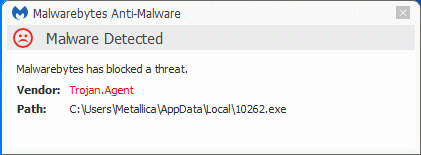
Likewise some of the main files involved in the HPRewriter2 hijack are detected as Trojans. The resulting changes to the system are detected and removed as PUP.Optional.HPDefender.
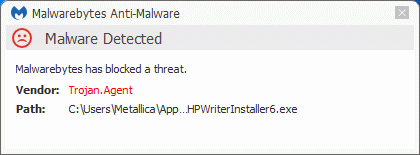
As a result of the Trojan detections Malwarebytes Anti-Malware Premium users are protected against these threats even if they don’t have the Non-Malware Protection enabled.
Save yourself the hassle and get protected too.
Pieter Arntz











