For the third time in a month Google has issued an update to patch for several security issues. This time the update patches 19 vulnerabilities, of which 5 are classified as “high” risk vulnerabilities.
In an update announcement for Chrome 95.0.4638.54, Google specifies the 16 vulnerabilities that were found by external researchers.
The CVEs
Publicly disclosed computer security flaws are listed in the Common Vulnerabilities and Exposures (CVE) database. Its goal is to make it easier to share data across separate vulnerability capabilities (tools, databases, and services).
Below are the CVEs attributed to external researchers that got rated as high risk:
- CVE-2021-37981 (High CVSS 7.7) : Heap buffer overflow in Skia. The vulnerability exists due to a boundary error when processing untrusted HTML content in Skia. A remote attacker can create a specially crafted web page, trick the victim into opening it, trigger a heap-based buffer overflow and execute arbitrary code on the target system.
- CVE-2021-37982 (High CVSS 7.7): Use after free in Incognito. The vulnerability exists due to a use-after-free error within the Incognito component in Google Chrome. A remote attacker can create a specially crafted web page, trick the victim into visiting it, trigger a use-after-free error and execute arbitrary code on the target system.
- CVE-2021-37983 (High CVSS 7.7): Use after free in Dev Tools. The vulnerability exists due to a use-after-free error within the Dev Tools component in Google Chrome. A remote attacker can create a specially crafted web page, trick the victim into visiting it, trigger a use-after-free error and execute arbitrary code on the target system.
- CVE-2021-37984 (High CVSS 7.7): Heap buffer overflow in PDFium. The vulnerability exists due to a boundary error when processing untrusted HTML content in PDFium. A remote attacker can create a specially crafted web page, trick the victim into opening it, trigger a heap-based buffer overflow and execute arbitrary code on the target system.
- CVE-2021-37985 (High CVSS 7.7) : Use after free in V8. The vulnerability exists due to a use-after-free error within the V8 component in Google Chrome. A remote attacker can create a specially crafted web page, trick the victim into visiting it, trigger a use-after-free error and execute arbitrary code on the target system.
Heap buffer overflow
A buffer overflow is a type of software vulnerability that exists when an area of memory within a software application reaches its address boundary and writes into an adjacent memory region. In software exploit code, two common areas that are targeted for overflows are the stack and the heap. So, by creating a specially crafted input, attackers could use this vulnerability to write code into a memory location where they normally wouldn’t have access.
Use after free
Use after free (UAF) is a vulnerability caused by the incorrect use of dynamic memory during a program’s operation. If, after freeing a memory location, a program does not clear the pointer to that memory, an attacker can use the error to manipulate the program.
Skia
Skia was developed as an open-source graphics library, written in C++ which abstracts away platform-specific graphics API. After Google acquired it in 2005, Chrome uses Skia for nearly all graphics operations, including text rendering.
Incognito
Incognito mode in Google Chrome – and other browsers—is essentially a setting on your web browser to disallow the storing of local data relating to the websites you surf. When surfing the web in this mode, your browsing history will not be recorded.
Dev Tools
Chrome DevTools is a set of web developer tools built directly into the Google Chrome browser. The Chrome DevTools are a set of web authoring and debugging tools that web developers can use to iterate, debug and profile their site.
V8
V8 is Google’s open source JavaScript and WebAssembly engine. Basically, it’s the engine that reads JavaScript V8 and translates the JavaScript code directly into machine code so that computers can actually understand it. This way the code can be run while browsing. WebAssembly is a binary format that allows you to run code from programming languages other than JavaScript on the web efficiently and securely. This format is handled by V8 as well.
PDFium
Pdfium.Net SDK is the leading .Net library for generating, manipulating and viewing files in the portable document format. It is used in Chrome for displaying PDFs and print preview. It’s also used in Android for PDF rendering.
How to protect yourself
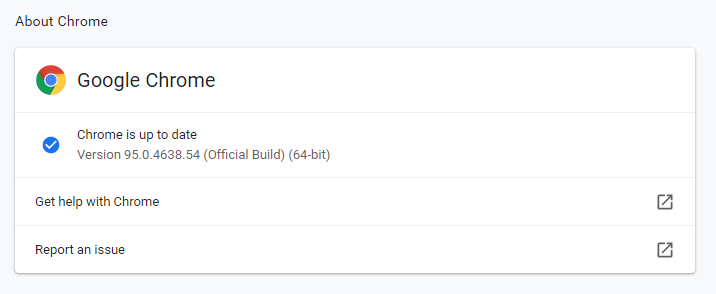
If you’re a Chrome user, you should update to version 95.0.4638.54 as soon as possible. Users of other Chromium browsers should be on the lookout for updates that fix the vulnerabilities they will have in common.
The easiest way to update Chrome is to allow Chrome to update automatically, which basically uses the same method as outlined below but does not require your attention. But you can end up lagging behind if you never close the browser or if something goes wrong, such as an extension stopping you from updating the browser.
So, it doesn’t hurt to check now and then. And now would be a good time, given the working exploits. My preferred method is to have Chrome open the page chrome://settings/help which you can also find by clicking Settings > About Chrome.
If there is an update available, Chrome will notify you and start downloading it. Then all you have to do is relaunch the browser in order for the update to complete.
Stay safe, everyone!











