As we reporteda few days ago, a F5 BIG-IP vulnerability listed as CVE-2022-1388is actively being exploited. But now researchers have noticed that attackers aren’t just taking control of the vulnerable servers but also making them unusable by destroying the device’s file system.
F5 BIG-IP
The BIG-IP platform by F5 is a family of products covering software and hardware designed around application availability, access control, and security solutions. It is used for various applications like load balancing and application delivery.
On May 4, 2022 F5 notifiedusers of the existence of a vulnerability in BIG-IP iControl REST where undisclosed requests could bypass iControl REST authentication. F5 said the vulnerability could allow an unauthenticated attacker with network access to the BIG-IP system through the management port and/or self IP addresses to execute arbitrary system commands, create or delete files, or disable services. The attacker, in other words, could gain complete control over the affected device.
Soon after the patch, two separate groups of researchers announced on Twitter that they had developed exploits and would publish them soon. Other researchers noticed online scanning was ongoing for BIG-IP.
Due to the critical nature of the bug, F5 urged admins to apply updates as soon as possible.
New type of attack
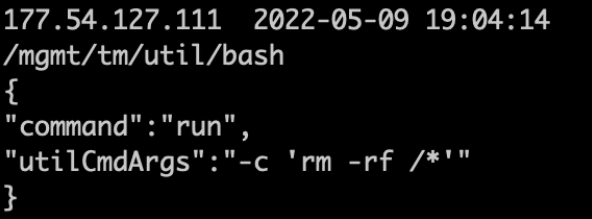
While most of the attacks so far were aimed at creating a foothold or gathering information for further attacks, we are now seeing a very different and destructive type of attacks.
At least one group of attackers is sending commands to vulnerable devices that delete the whole F5 file system, which is breaking load balancing and websites.
While destroying the file system of the device may seem worse than data exfiltration or planting a backdoor at first glance, some researchers are saying it may be a blessing in disguise. The group is making the vulnerable devices unavailable for threat actors that are trying to utilize the more monetizable attack vectors. Most of the original attacks were dropping web shells, which are malicious scripts used by an attacker that allows them to escalate and maintain persistent access on an already compromised web application. (Not every web shell is malicious, but the non-malicious ones are not interesting to us in this context.)
The motives of this threat actor are hard to guess. Maybe it’s simply a case of showing off, or an act out of sheer frustration.
But for those running a vulnerable device this makes the “can’t patch now, for it will make the device unavailable” argument moot. If this attackers gets to you the device will be unavailable for much longer than it takes to patch.
Stay safe, everyone!