Recently, we have seen an increasing number of reports from iPhone users about their calendars filling up with junk events. These events are most often either pornographic in nature, or claim that the device has been infected or hacked, and in all cases they contain malicious links. This phenomenon is known as “calendar spam.”
Calendar spam became a big problem for Apple’s iCloud calendars back in 2016. At that time, Apple put some protections in place on iCloud to prevent these issues. Whatever they did was working, up until recently. Let’s take a look at how the scammers have changed their tactics.
Fake captcha page example
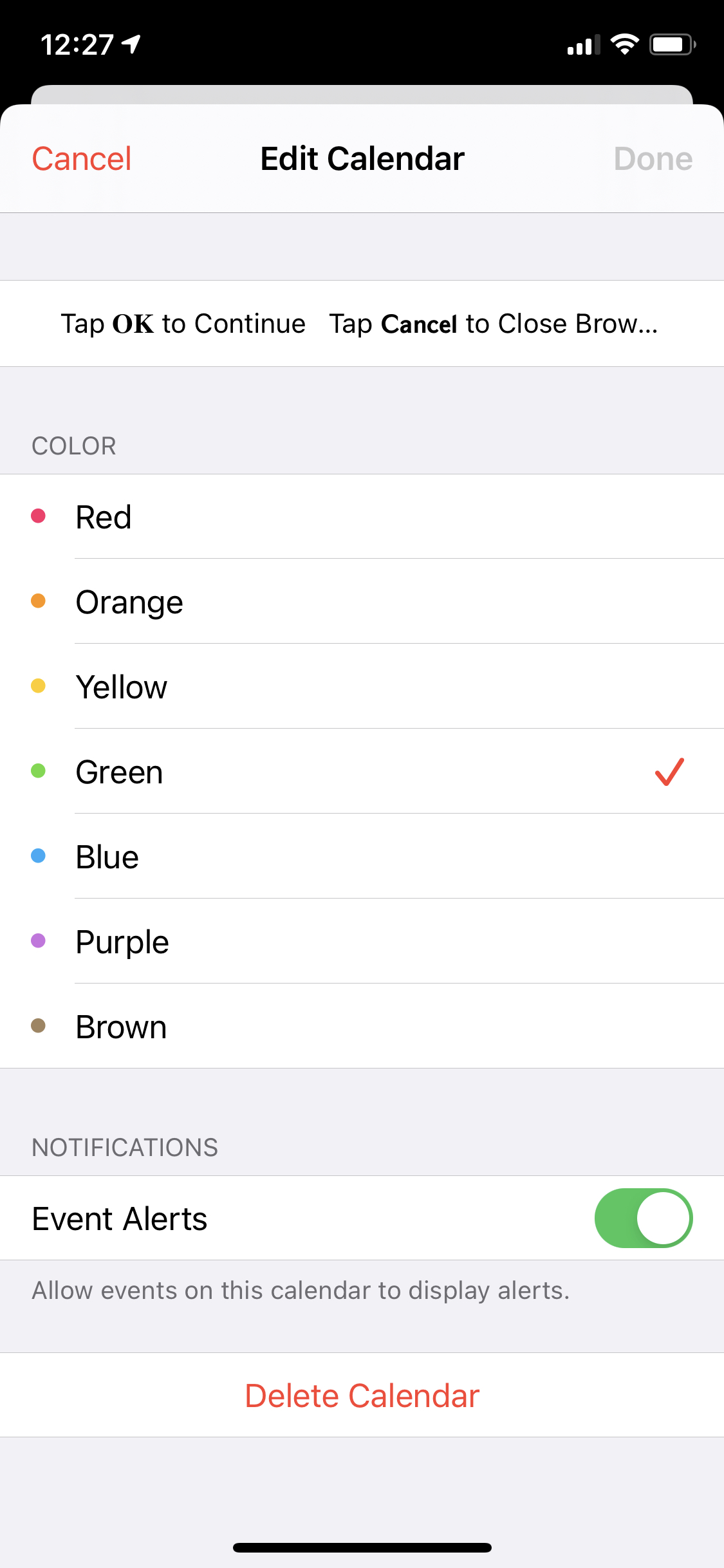
Users will encounter a scam web page like the following one (though this is just an example). These pages are reached via a number of techniques, including malvertising, compromised WordPress sites, and Search Engine Optimization (SEO) tricks. In this case, the page displays a fake captcha that users are expected to tap in order to prove they’re not a bot.
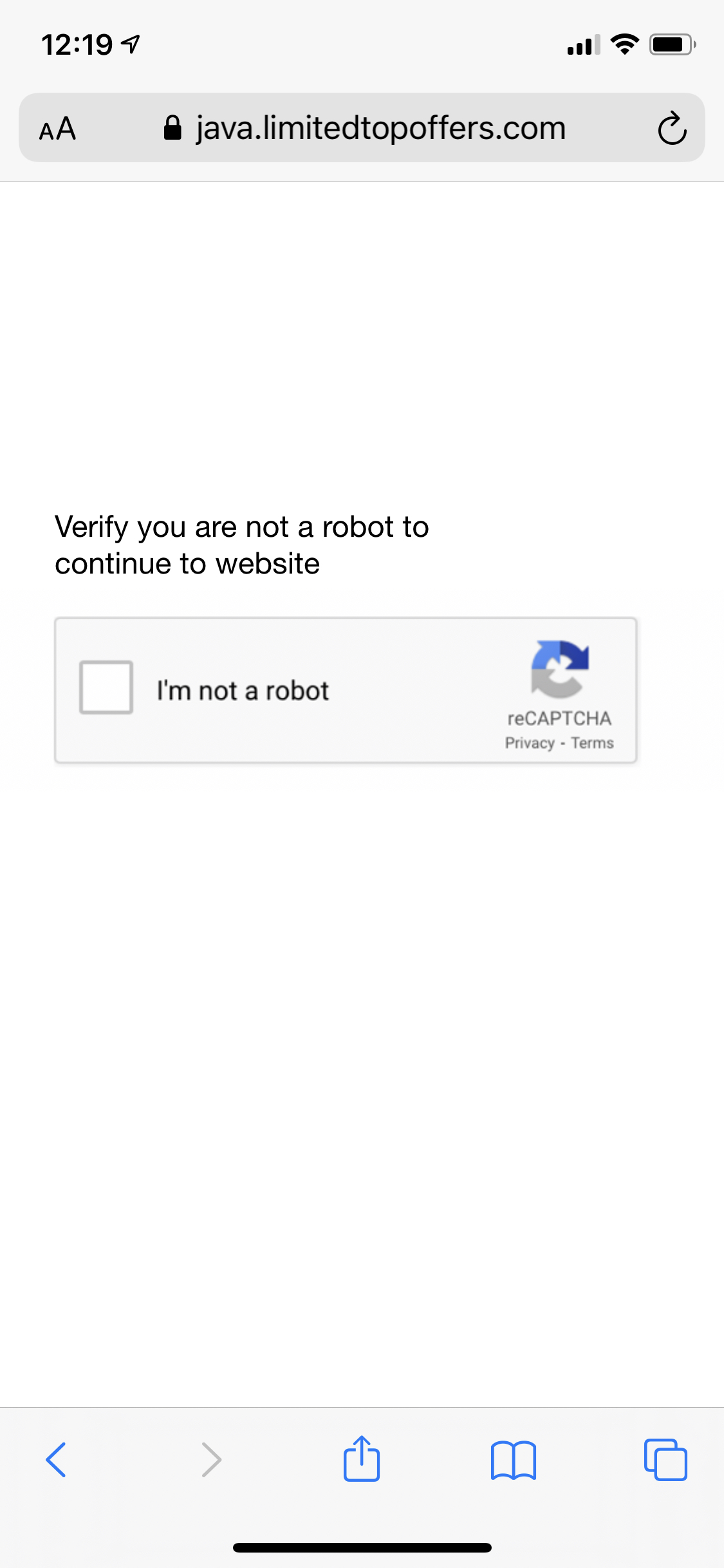
For this particular page, tapping the “I’m not a robot” box (or, really, anywhere else on the page) results in a prompt attempting to trick the user into subscribing to a calendar.
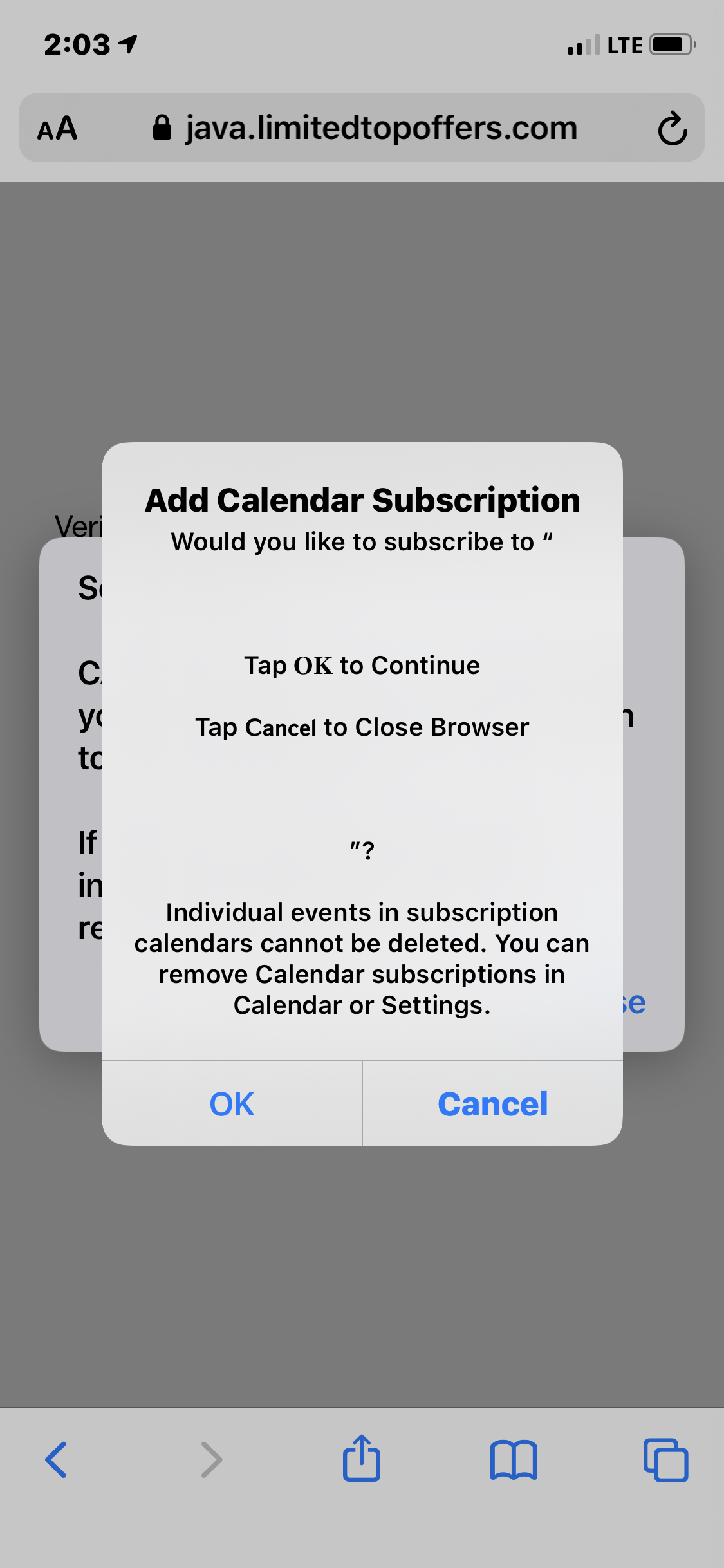
Normally, this prompt would ask the user if they want to subscribe to a particular calendar by name. In this case, the scammers have given the calendar a name containing whitespace and the “Tap OK to Continue” / “Tap Cancel to Close Browser” message. Clicking Cancel will return you to the page, and if you do this a couple times, you’ll trigger a redirect. (More on that shortly.)
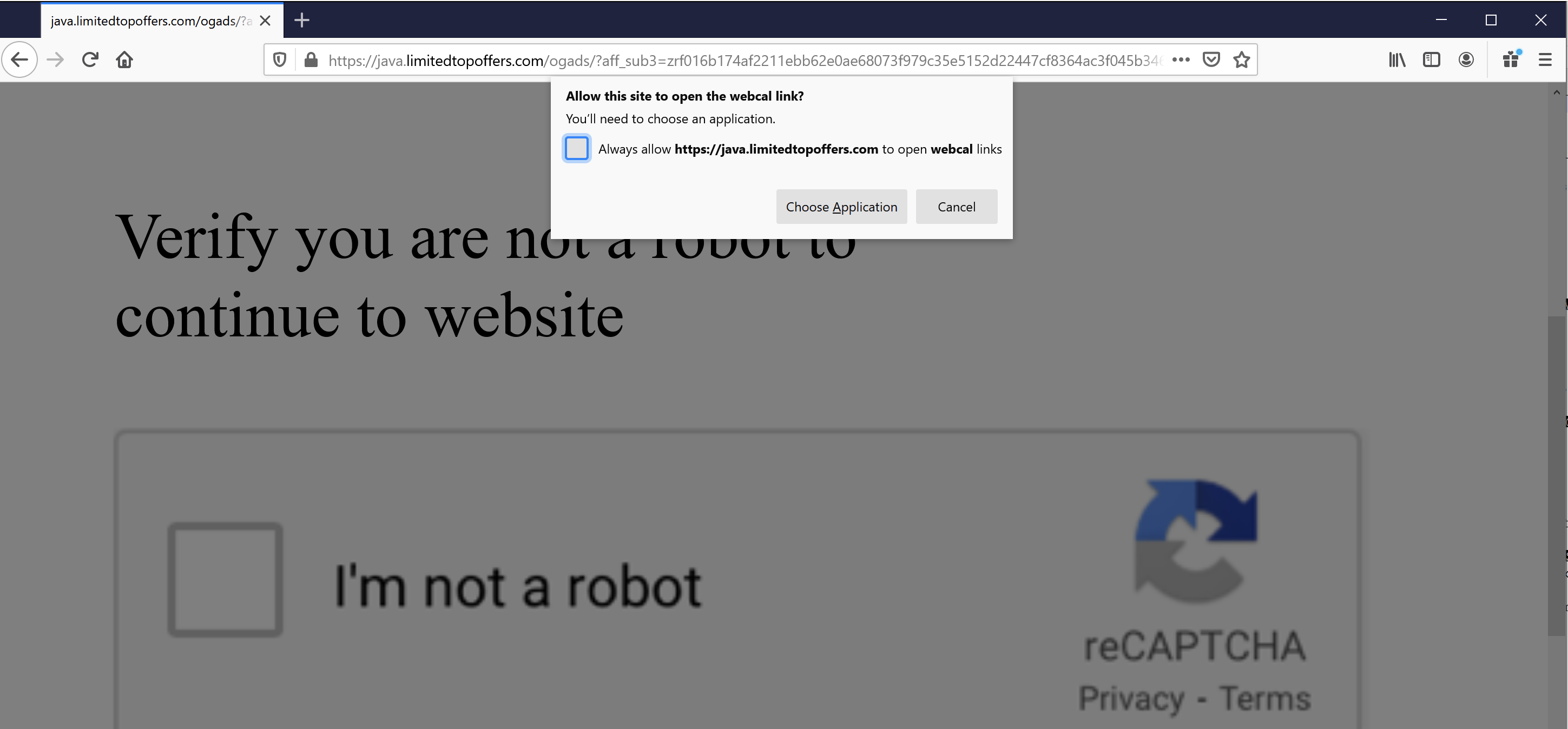
Clicking OK results in the spam calendar, and all its events, being added to the user’s Calendar app. These events all have alerts that cause notifications to appear in the Notification Center. Tapping a notification will take you into Calendar, which will display the content of the event. In all cases, the content is a scam message trying to get you to open a link.
At this time, the links go to a 404 page, but we believe they would have linked out to apps in Apple’s App Store.
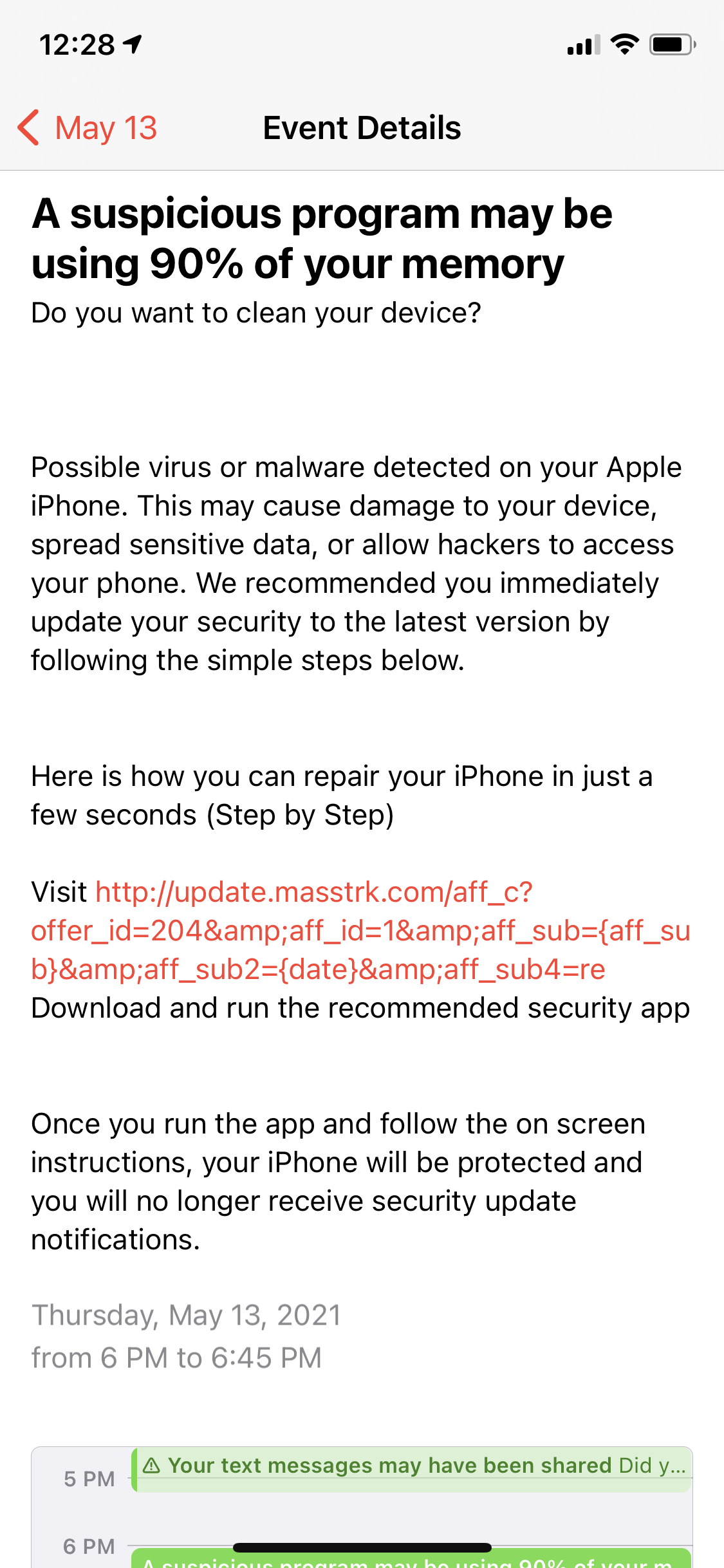
Redirects to “security” apps
Whether you do or don’t subscribe to the calendar, the page will go back to the fake captcha. Tapping the captcha a second time, and clicking either OK or Cancel, will result in your browser being redirected to a scam page claiming your iPhone is infected or that hackers are watching you.
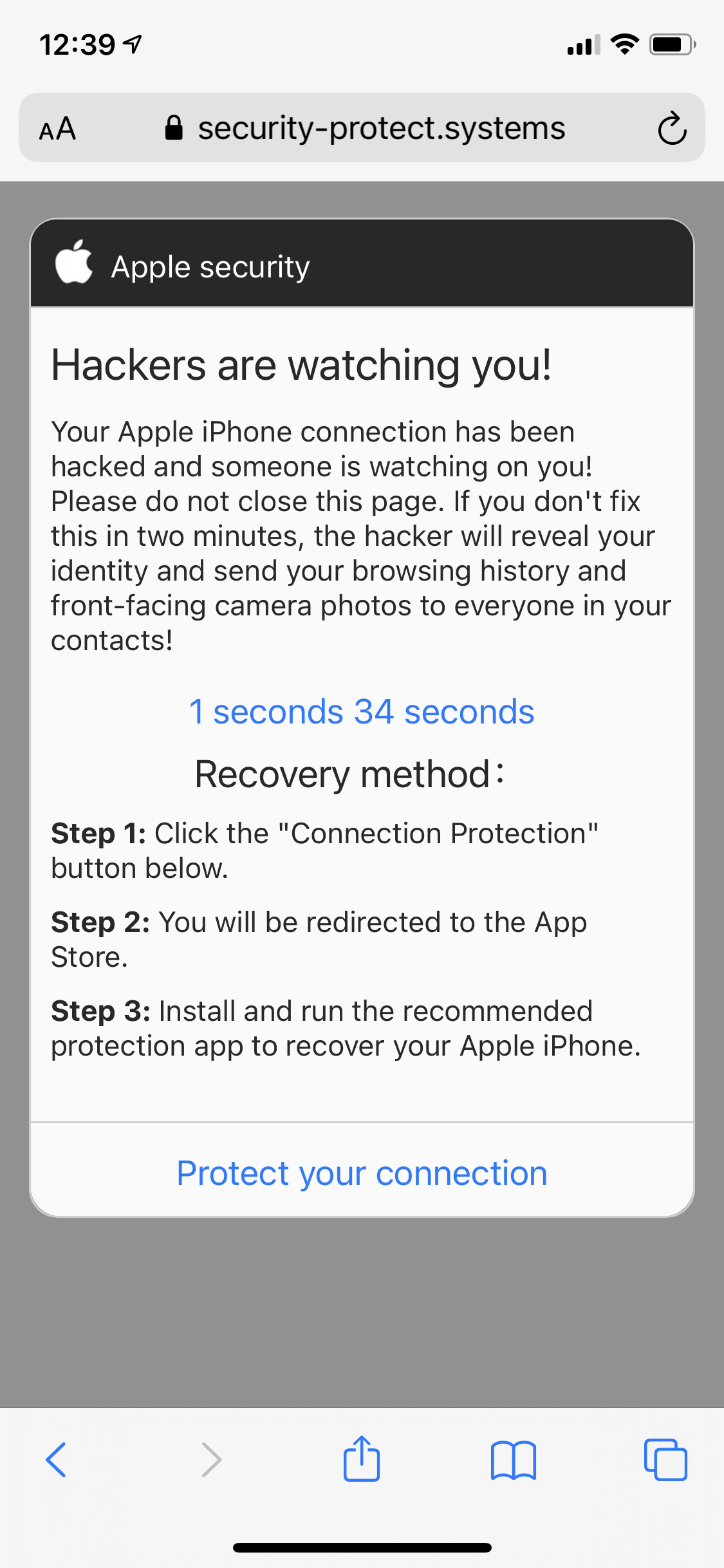
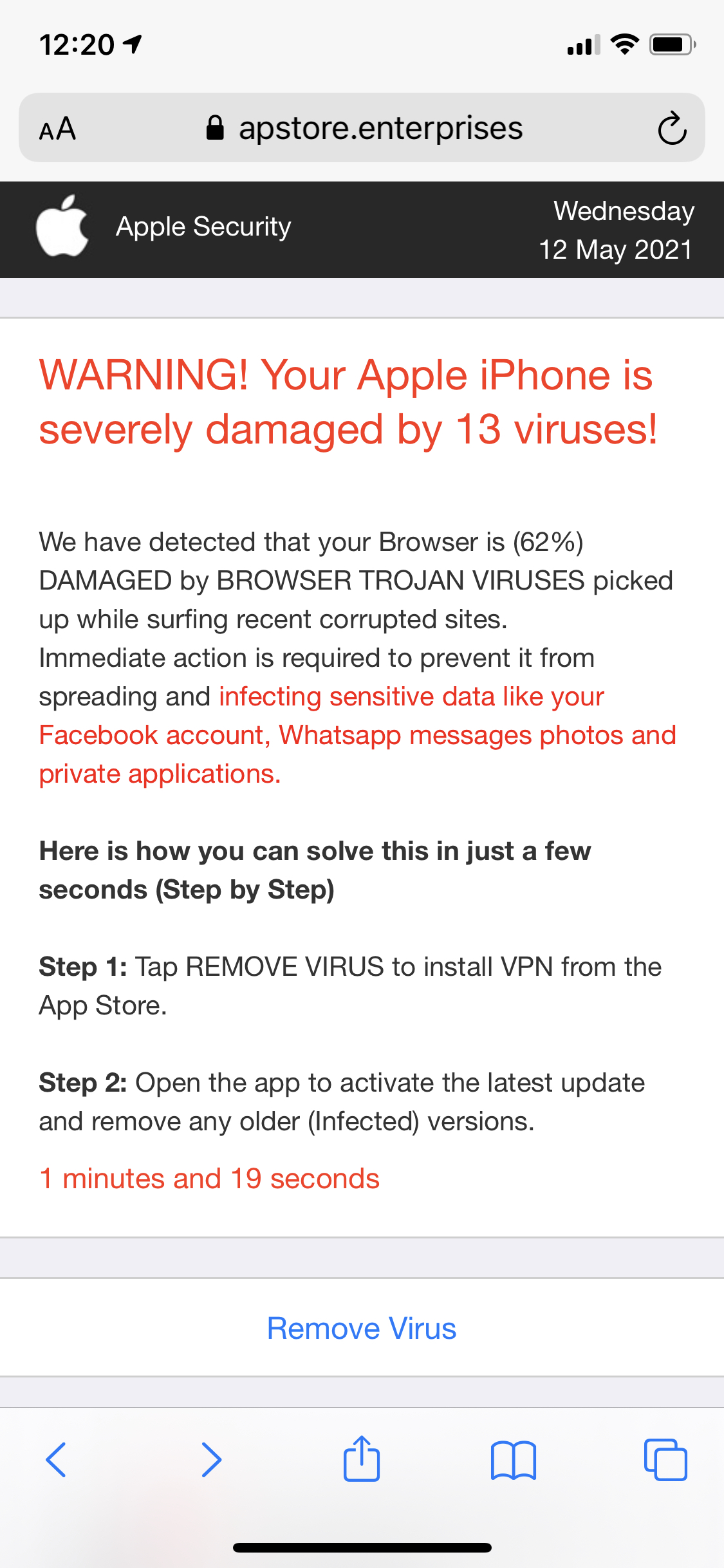
These pages will redirect to a variety of App Store apps. Mostly, these are junk VPNs or supposed security apps. They mostly have high ratings, and have been around for 4+ years, but the total number of ratings given is low. This could be an indication that the ratings have been reset periodically.
Worse, many of these apps have high price, short duration subscriptions. In most cases, prices are around $8.99 or $9.99 per week.

Removing the subscribed calendar(s)
If you have been impacted, your iPhone has fortunately not actually been hacked or infected (regardless of what the messages claim), and there is a simple solution. You can just delete the subscribed calendars.
First, open your Calendar app, and then tap the Calendars button at the bottom center of the screen, shown below.
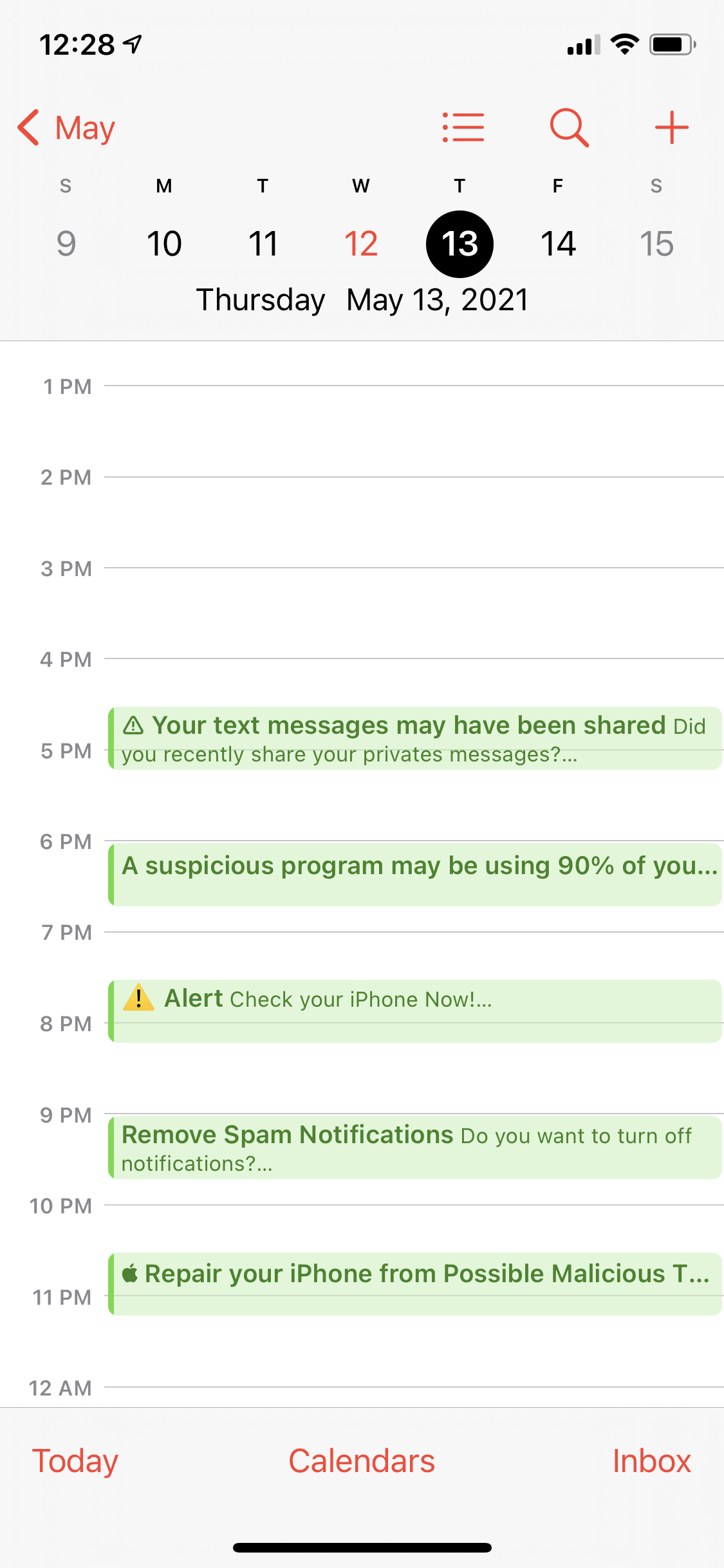
This will result in seeing a view like the following, showing all the calendars loaded on your iPhone. Note the odd item with a green tick and no title, under the heading “SUBSCRIBED”.
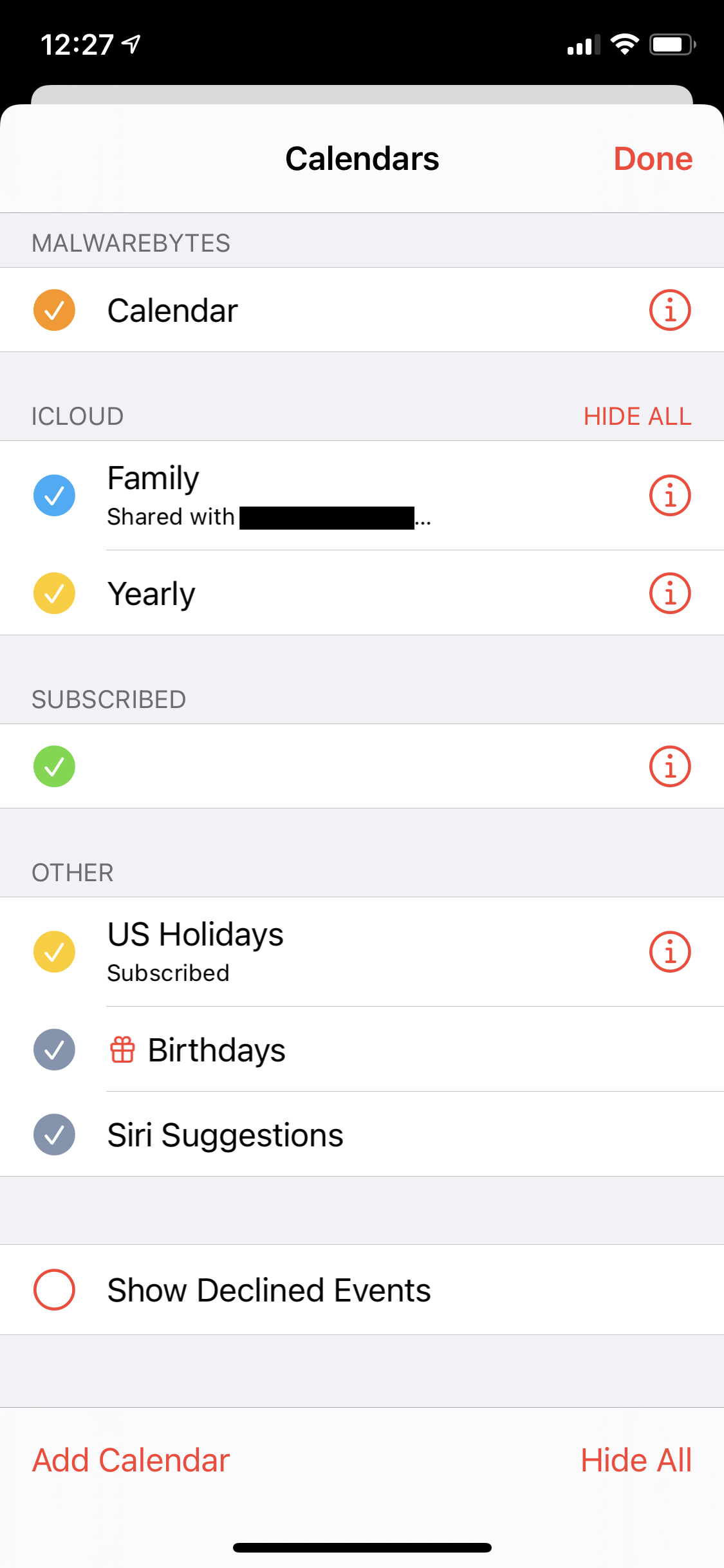
The calendar name appears blank here, but that may not be true in every case. You’ll want to remove all subscribed calendars, except those that you are certain are legitimate. To do this, tap the button showing the letter i in a circle next to the subscribed calendar. (If you have more than one, you’ll have to repeat for each one.)
On the next screen, tap the Delete Calendar button at the bottom of the screen. (On some devices, you may have to scroll down to see it.)
How to prevent the issue
First and foremost, if you find yourself seeing a strange message in Safari on your iPhone, don’t believe it, and don’t do what it tells you to do. Don’t click any buttons consenting to whatever the site is asking, such as OK, Allow, Install, etc. If you can close the tab or navigate to another page in the browser, do so. If an alert is preventing that, click Cancel if that’s an option.
If there is an alert preventing you from taking action until you tap a button, and you don’t know what to do, just restart your iPhone.
You can also use the Web Protection feature in Malwarebytes Security for iOS. This should prevent you from visiting malicious pages in Safari. Of course, as with all things, nothing is infallible, so if you find that a malicious site has slipped past, please copy the address of the page from Safari’s address bar and submit it via a support ticket to Malwarebytes support. A screenshot would help as well.
Unfortunately, since users are essentially consenting to this scam via existing Apple-provided mechanisms for obtaining consent, there may not be much that Apple can do to stop this particular wave of calendar spam. However, we’ve notified Apple anyway, and hope it can at a minimum take action against the apps promoted by these scams.
What about other platforms?
Although we’re seeing a lot of this on iOS right now, the scam affects other platforms as well. On macOS, for example, it will attempt to add a calendar, though the process is far less convincing.
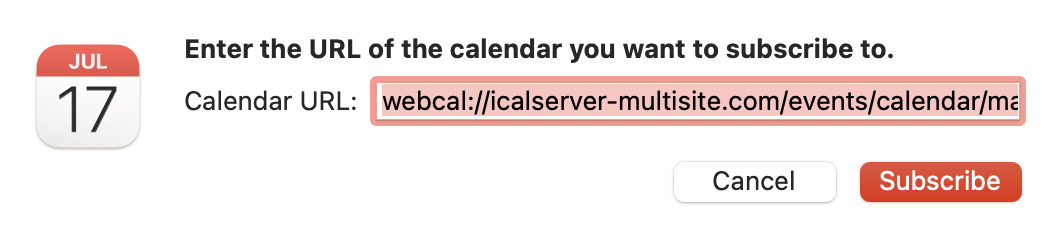
The same is also true on Windows.
You may also be offered a browser extension by some variants of this scam, depending on your browser. (Google Chrome is a common target.)
Regardless of the platform, if you see something odd like this in the browser, do not allow it, and close the page.