Microsoft offers to help you with patching Exchange servers, CISA offers an insider threat tool, and together with the NSA they offer advice on how to choose and harden your VPN.
These initiatives from major parties aim to help organizations assess and manage their security needs. But will they make an impact with their intended audience?
Microsoft Exchange Emergency Mitigation service
Microsoft will tomorrow roll out a new security feature for its Exchange email servers, which have been at the center of several hacking campaigns over the past two years.
In the September 2021 Cumulative Update (CU), Microsoft has added a new feature called the Microsoft Exchange Emergency Mitigation (EM) service. This service is not intended to be a replacement for installing Exchange Server Security Updates (SUs), but as a quick and effortless way to mitigate the latest threats against internet-connected, on-premises Exchange servers.
The basic idea is that once Microsoft detects a new attack being used in the wild, it will push out temporary mitigations to all Exchange servers around the world that are running the EM services. And that’ll happen even before they start working on a software patch to thwart the vulnerability. EM runs as a Windows service on Exchange Server, but if an organization doesn’t want to use EM, an admin can disable the service.
Microsoft introduced the EM service after it learned that many of its customers weren’t ready to install SUs because they were not running a supported CU.
CISA Insider Risk Mitigation Self-Assessment tool
The Cybersecurity and Infrastructure Security Agency (CISA) released an Insider Risk Mitigation Self-Assessment Tool, which assists public and private sector organizations in assessing their vulnerability to insider threats.
Insider threats are a serious risk to any organization because of the institutional knowledge and trust placed in the hands of the perpetrator. Insider threats can come from current or former employees, contractors, suppliers, or others with inside knowledge. The tool is designed to raise awareness and help measure the level of risk, and users receive feedback based on their answers to a series of questions.
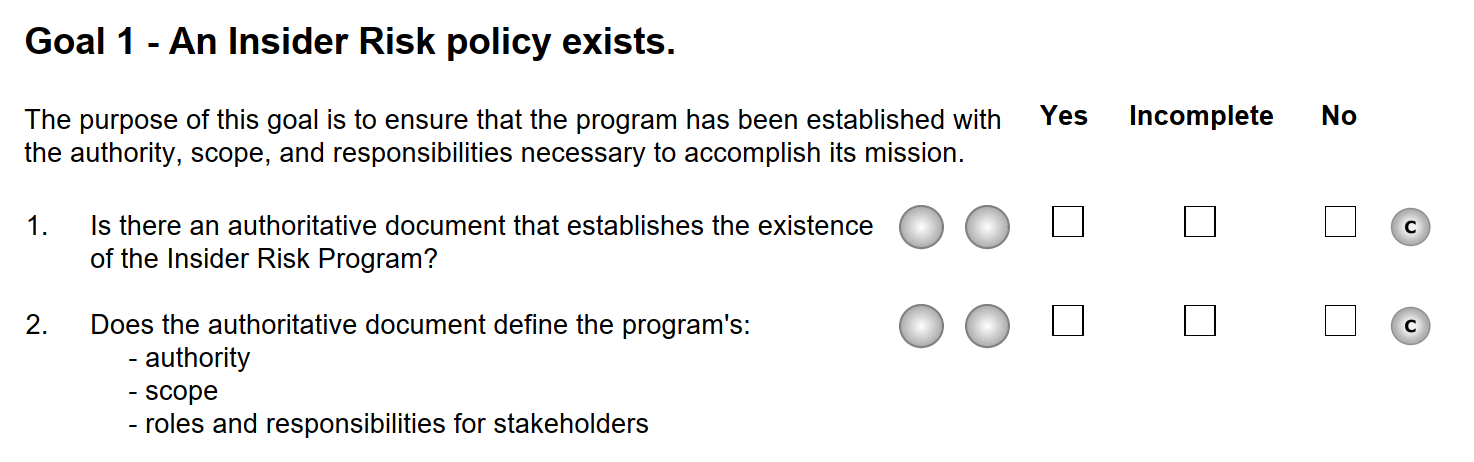
CISA urges all its partners, especially small and medium businesses who may have limited resources, to use this new tool to develop a plan to guard against insider threats. It states that making some small steps today can make a big difference in preventing or mitigating the consequences of an insider threat in the future.
NSA and CISA advise on VPNs
The National Security Agency (NSA) and the Cybersecurity and Infrastructure Security Agency (CISA) released a joint Cybersecurity Information Sheet today detailing factors to consider when choosing a virtual private network (VPN) and top configurations for deploying it securely. The Information Sheet details considerations for selecting a remote access VPN, as well as actions to harden the VPN from compromise.
Remote access VPNs are entryways into corporate networks and all the sensitive data and services they have. This direct access makes them prized targets for malicious actors. Multiple nation-state advanced persistent threat (APT) actors have weaponized common vulnerabilities and exposures (CVEs) to gain access to vulnerable VPN devices.
NSA is releasing the VPN guidance as part of its mission to help secure the Department of Defense, National Security Systems, and the Defense Industrial Base. Basically the advice comes down to selecting a secure, standards-based VPN and hardening its attack surface.
You may say “duh” but organizations running National Security Systems are required to use the algorithms in the NSA-Approved Commercial National Security Algorithm (CNSA) and government systems are required to use the algorithms as specified by the National Institute of Standards and Technology (NIST), which includes the algorithms approved to protect NSS.
What is the main problem?
At Malwarebytes Labs, we’ve reported about many vulnerable VPNs, and networking devices that have patchable vulnerabilities. The same is true for Microsoft Exchange vulnerabilities. We’ve also written about the importance of recognizing the danger of insider threats.
But one thing we have learned over the years is that education and raising awareness helps, but it is not picked up by everyone. Knowing that a problem exists and that a patch is available is an important step. But it is useless without the logical next step, patching. Unfortunately, patching cycles are troubled by a few main factors:
- People not knowing a patch was available or even that the problem existed
- Fear that something might stop working, so that needs to be tested first, and all that takes too much time
- No patch being available because the product has reached end-of-life (EOL)
- Not enough staff to keep up with the necessary patching
- Remote and hybrid workforces make patch management more complicated
As a result, critical patches are delayed, often leaving a windows of opportunity for attackers between reverse-engineering the patch and when the patch is widely applied. What that means for all the help provided is that those that need it the most will probably not use it, unless they are compelled to do so.
Microsoft Exchange users that did not have the necessary CUs are unlikely to install the EM service.
Small and medium businesses with limited resources will probably lack the time and staff to use the insider risk mitigation self-assessment tool.
Choosing and hardening an approved VPN may be useful for new customers, but those that already have a working system in place are often content to leave it as is, for all the reasons listed above.
Risks involved in remote mitigation
While some experts applaud the effort by Microsoft to offer a service that can be used as kind of a first aid kit for Exchange, since it can mitigate risks before a patch is available, others see some dark clouds on that horizon.
“Automatically installing temporary mitigations that block active exploitation of security flaws until Microsoft is ready to release official patches.” This will translate in many a system administrator’s mind to Microsoft making changes on my server that I know nothing about. Will we be able to find the source if these changes cause problems?
Having a first aid kit can give users a false sense of security. But you should still apply that patch as soon as it is made available and not rely on the band aid to hold.
Supply chain attacks have become a big thing and taking over the EM service sounds like an attacker’s dream come true. Imagine having the tool in hand to disable security on every Exchange server running that service. This has to be one of the most secure services in Microsoft’s history to avoid that scenario.
Stay safe, everyone!











