In an attempt to make Edge more secure, the Microsoft Vulnerability Research team has started to experiment with disabling Just-In-Time (JIT) compilation in the browser’s V8 JavaScript engine, to create what it’s calling Super Duper Secure Mode.
The reasoning behind this experiment sounds valid. A little under half of the CVEs issued for V8 are relate to the JIT compiler and more than half of all ‘in-the-wild’ Chrome exploits abuse JIT bugs. (Modern versions of Edge are based on the same Chromium code as Google’s Chrome browser, so Chrome exploits also affect Edge.) Microsoft is wondering out loud if the simplest way to deal with such a problematic sub-system is to just disable it and see where it takes them.
Disabling JIT compilation comes at a price though: speed. JIT compilation is a performance feature that speeds up the execution of JavaScript, the most popular programming language used on the web. Because it sits behind so many web applications, the speed that JavaScript runs has a direct effect on how fast and responsive web applications are.
We were curious just how big an effect it would have.
What is JIT compilation?
A good definition of JIT compilation is this one:
“Just-in-time (JIT) compilation … is a way of executing computer code that involves compilation during execution of a program (at run time) rather than before execution.”
The reason to use JIT compilation is simple: speed. JIT compilation combines the speed of compiled code with the flexibility of interpretation. It allows for more optimized code to be generated. And to limit the overhead, many JIT compilers only compile the code paths that are frequently used.
V8 is Google’s open source high-performance JavaScript and WebAssembly engine, written in C++. It is used in Chrome and in Node.js, among others. Since Edge is based on Chromium it uses V8 as well.
The speed impact of disabling Edge’s JIT compiler
We ran a few quick tests to see how big the impact of disabling JIT would be. To run these tests we compared the latest official release of Edge (Version 92.0.902.67) with the latest available Microsoft Edge Beta (Version 93.0.961.11) with Super Duper Secure Mode enabled and disabled. We found that the speed differences between the latest official release and the beta were marginal, so we we have left those out of the results.
The tests were done in a VM on a slow connection. As a benchmark we used Sunspider 1.0.2. We wanted to try the more elaborate JetStream2, but for some reason that never made it to the end. (If you get it to work with JetStream2, we’d love to hear from you.)
Sunspider says its benchmarking focusses “on the kinds of actual problems developers solve with JavaScript today”, is “balanced between different areas of the [JavaScript] language”, and runs each test multiple times to determine a 95% confidence interval and whether you have a statistically significant result.
Test SDSM Enabled SDSM disabled Speed up 3d 76.7ms +/- 3.4% 59.2ms +/- 3.6% 1.3x access 102.0ms +/- 0.8% 33.7ms +/- 4.1% 3.03x bitops 98.4ms +/- 1.0% 17.1ms +/- 3.7% 5.75x controlflow 9.1ms +/- 2.5% 5.6ms +/- 6.6% 1.63x crypto 46.0ms +/- 1.5% 37.9ms +/- 8.1% 1.21x date 23.6ms +/- 1.6% 26.9ms +/- 2.0% 1.14x math 61.4ms +/- 1.5% 28.6ms +/- 2.4% 2.15x regexp 36.0ms +/- 2.1% 5.6ms +/- 6.6% 6.43x string 70.1ms +/- 2.2% 63.2ms +/- 2.1% 1.109x Total 523.3ms +/- 0.6% 277.8ms +/- 1.9% 1.88x
Our results show that enabling the JIT speeds up JavaScript execution in Edge by a factor of 1.88. So disabling JIT compilation makes Edge’s JavaScript processing more secure, but almost twice as slow.
A few remarks I want to make before you do:
- The benchmark tests the core JavaScript language only and many more things affect the speed of the web than JavaScript execution. So this does not mean that normal surfing will be twice as slow!
- I repeated the tests several times and while there were some differences the general comparison was roughly the same every time. (Results varied between a 1.87x and 1.90x speed up when JIT compilation was enabled.)
Microsoft claims it found that users using Super Duper Secure Mode rarely notice a difference in their daily browsing. It will probably depend on the type of site(s) you’re visiting, what else you’re doing at the time etc, but it is worth noting that tools that measure web performance, including Google’s Core Web Vitals, attach great importance to JavaScript because slow JavaScript can have such a profound effect on user experience.
Not without a replacement
Regardless, history teaches us that simply disabling the V8 JIT compiler is not going to be a long-term solution. The first advice anyone would get on a computer forum if they complained about a slow browsing experience is going to sound like “enable JIT”. We think we can predict this with great confidence based on similar experience with anti-virus software.
The general public is not going to trade in speed for security. So Microsoft will eventually have to provide people with an alternative. What are the alternatives? It could decide to fix V8 and address whatever the root cause of the V8 bugs is. If it turns to another JavaScript engine entirely, it has a choice of perhaps four: Chakra or ChakraCore, free and open-source JavaScript engines developed by Microsoft for its Edge Legacy web browser; Duktape; or Moddable.
And there are a few more, but realistically speaking, for Microsoft to adapt or adopt one of these engines for Edge would mean to turn a way from Chromium, which it has only recently turned to. It seems unlikely that it will immediately create a “hard fork” so to speak. For now the goal of the Super Duper Secure Mode experiment is to raise the bar for attackers.
The security problems of JIT compilation
As we mentioned earlier, disabling JIT compilation in Edge reduces the number of options that an attacker has (known as reducing the attack surface). But another problem with JIT compilation is that it is incompatible with some mitigation technologies. The Microsoft Vulnerability Research team mentions a few security features that can’t be used when JIT is enabled:
- Control-flow Enforcement Technology (CET) a hardware-based exploit mitigation from Intel. Intel has been actively collaborating with Microsoft and other industry partners to address control-flow hijacking by using this technology to stop attackers from using existing code running from executable memory in a creative way to change program behavior.
- Arbitrary Code Guard (ACG) helps protect against a malicious attacker loading the code of their choice into memory through a memory safety vulnerability and being able to execute that code. Arbitrary code guard prevents allocating any memory as executable, which presents a compatibility issue with approaches such as Just-in-Time (JIT) compilers.
We are thrilled that Microsoft is looking at raising the security standard of its Edge Browser. After a unprecedented number of Chrome zero-days in 2021, and a number of high profile security incidents related to several Microsoft products this is a welcome change of pace.
Try it yourself
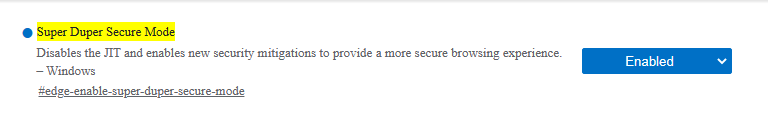
Users that want to try Super Duper Secure Mode for themselves will have to get hold of one of the Microsoft Edge preview releases (Beta, Dev, or Canary). If you have one of these running your can insert edge://flags/#edge-enable-super-duper-secure-mode into the address bar of the browser and set the new feature to “Enabled”.
Since this is an experiment we don’t have to take the name Super Duper Secure Mode very seriously. It’s probably not here to stay and may be an indication of how likely it is that disabling the JIT compiler without a replacement will become mainstream.
Stay safe, everyone!











