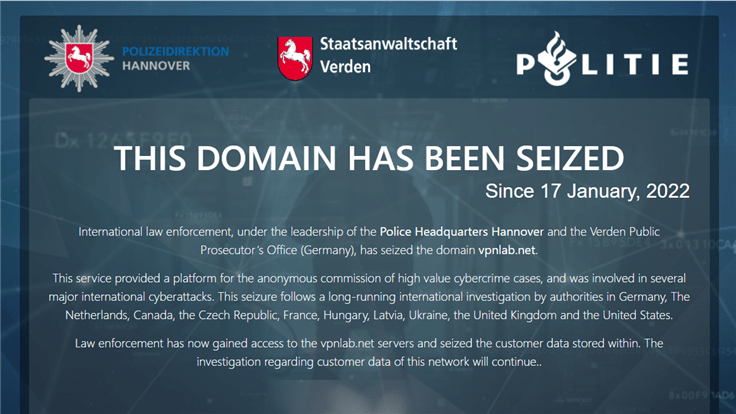
Europol has announced that law enforcement has seized or disrupted the 15 servers that hosted VPNLab.net’s service, rendering it no longer available.
Led by the Central Criminal Office of the Hannover Police Department in Germany, the coordinated operation took place in Germany itself, the Netherlands, Canada, the Czech Republic, France, Hungary, Latvia, Ukraine, the United States and the United Kingdom.
What was VPNLab.net?
VPNLab.net was a virtual private network provider that mostly advertised its services on the criminal side of the Dark Web, and provided services for various cybercriminals, including ransomware gangs. VPNLab had been around since 2008 and had built its service around the OpenVPN technology, used strong encryption, and provided double VPN, with servers located in many different countries.
According to its own website before it was taken down, VPNLab said it was a service providing your security on the Internet by using encryption of original traffic.
“Our service is designed for a broad spectrum of clients who care about their personal security. We set a special encrypted channel between your computer and our foreign servers. The channel is installed based on OpenVPN technology and encrypted using 2048 bit key and thanks to sophisticated algorithms all the information is unreadable for your provider. Average users don’t see the necessity of the described procedure and may even find it useless.”
At a cost of $60 per year and the multitude of accepted payment methods that included WebMoney, Perfect Money, and a host of cryptocurrencies, this would not indicate to visitors that they were looking at a predominantly illicitly used service but at one that certainly took privacy seriously.
What is double VPN?
Double VPN is basically what the name suggests. Your online activities are not hidden behind one, but two servers. The basic technology is called VPN server chaining and the idea behind it is pretty simple, but that doesn’t mean the technology is.
- Your traffic is encrypted on your device and sent to an external VPN server.
- Upon reaching the server it is encrypted again.
- The double encrypted data goes to a second server where it is decrypted.
- And then the information is sent to its destination, secure and private.
Double VPN is not a common feature, because it is very slow. When your traffic runs through two VPN servers located in different countries thousands of miles apart, the slow down becomes inevitable. Also, using double encryption is especially resource-demanding.
The will to keep your traffic private will really have to be worth the time and resources, before you use double VPN. This narrows down the interested users, but certainly includes many criminals.
DoubleVPN was also the name of a similar service used by cybercrime groups that got taken down in a coordinated effort between global law enforcement agencies, led by the Dutch National Police in June of 2021.
The impact
During this week’s operation, 15 servers were taken offline and the domain name was seized. No arrests were mentioned which probably means that none were made.
According to the Head of Europol’s European Cybercrime Centre, Edvardas Šileris:
“The actions carried out under this investigation make clear that criminals are running out of ways to hide their tracks online. Each investigation we undertake informs the next, and the information gained on potential victims means we may have pre-empted several serious cyberattacks and data breaches.”
The intent of the actions is not directed at the services per se, but if service providers support illegal action and are unwilling to provide any information on legal requests from law enforcement authorities, then cooperation of international law enforcement agencies will be initiated in order to shut down a global network and destroy such brands that are clearly servicing criminals.
The bulletproof nature of the service made VPNLab.net a popular choice for cybercriminals, who could use its services to carry on committing their crimes without fear of being detected by authorities. Law enforcement took interest in the provider after multiple investigations uncovered criminals using the VPNLab.net service to facilitate illicit activities such as malware distribution.
Other cases showed the service’s use in the setting up of infrastructure and communications behind ransomware campaigns, as well as the actual deployment of ransomware. It was even advertised as such a service on the Dark Web.
All in all, it is another dent in the infrastructure provided to cybercriminals, which may have prevented or postponed a few crimes.