Today we took a look at a phishing mail pinning its hopes on a QR code linking to a bogus website. Scammers claim that your mail address has “not been registered for the 3D Secure Security Update”.
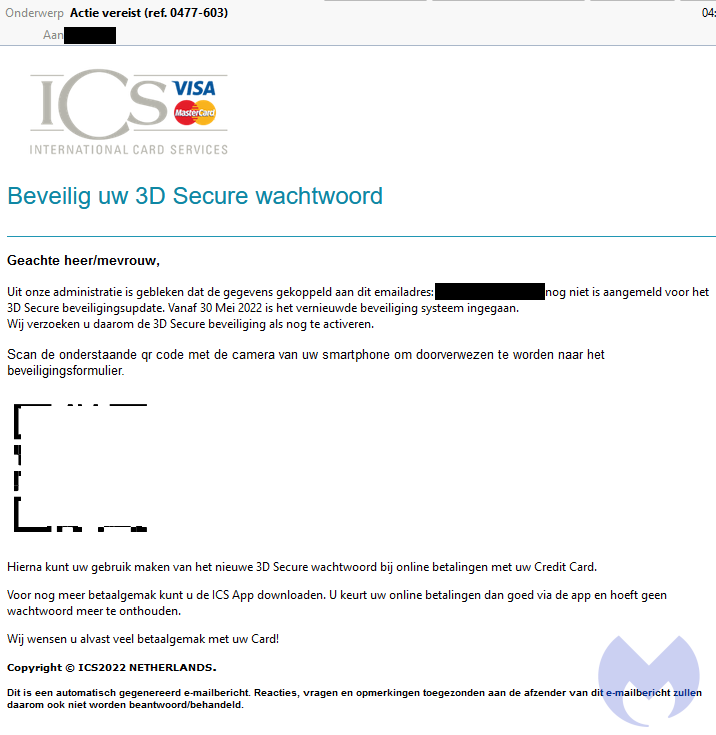
The mail reads as follows:
Dear Sir / Madam,Our administration has shown that the data linked to this email address:{redacted} has not yet been registered for the 3D Secure security update. From May 30, 2022, the new security system has come into effect.We therefore request that you activate the 3D Secure security.Scan the QR code below with the camera of your smartphone to be redirected to the security form.You can then use the new 3D Secure password for online payments with your credit card.For even more payment convenience, you can download the ICS App. You can then approve your online payments via the app and no longer have to remember a password.We wish you a lot of ease of payment with your Card! What is 3D Secure?
3D Secure is an additional layer of security for online payments. The name “3D Secure” refers to the 3 domains which interact whenever you make use of the protocol: Merchant, issuer, interoperability domain. 3DS2 is due to replace 3DS sometime in 2022 as the original is slowly phased out.
Encouraging potential victims to strengthen their security by inadvertently walking into a trap is a common tactic. Tying it in with 3D Secure is arguably more original than most, especially as it’s perhaps a bit of a niche aspect of secure payments. Perhaps confusing victims with some very specific technobabble is the point.
The rogue website
Victims arrive on the site via a redirect URL.
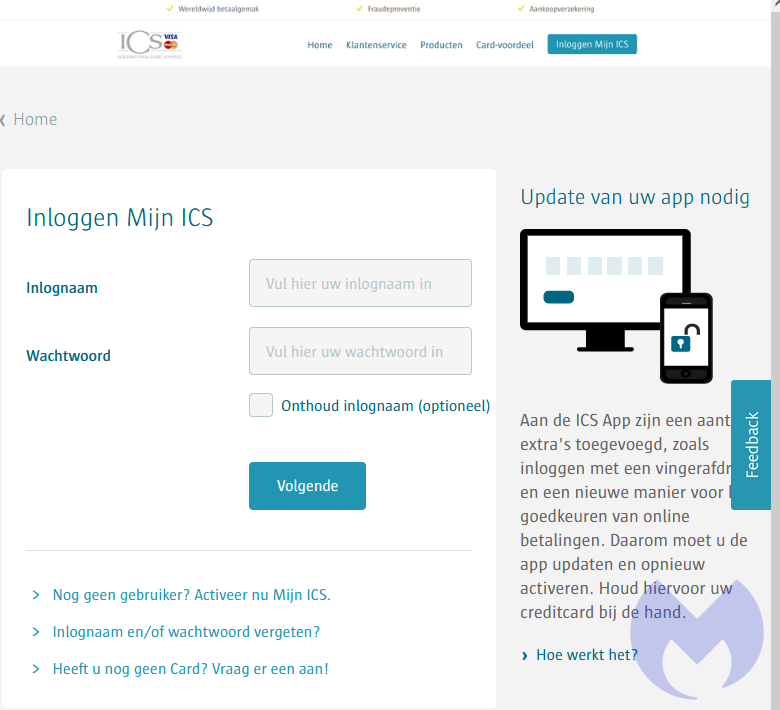
The site emulates a well known organisation which issues credit cards in the Netherlands. It asks for name, date of birth, postcode and house number, mobile, and email.

After this, victims arrive on a “please wait while we check your details” notification. The details entered have already been sent, and they’ll be waiting on that page for a very long time. Curiously, no request for card details is made. We suspect whoever runs the site will follow up by mail or phone and finish the scam off by asking for payment information.
The QR Code factor
Quick Response (QR) code scams come around every so often. Sometimes rogue codes are pasted over, or close to, genuine codes. Other times, codes are tampered with. They’re also a feature of Bitcoin ATM scams.
Where phishing is concerned, it’s important to not misunderstand how these attacks work and cause unnecessary panic. Most QR code scanners on mobile devices will show you a preview of the URL you’re about to visit, so it boils down to being able to recognise the signs of a dubious URL, just as it would if the attackers had incldued a link. (This is probably why the attack used a redirect.)
As a result, best practicesfor regular phishing attacks still apply.










