Twitter verification is a two-edged sword. According to Twitter, it’s supposed to let people know “that an account of public interest is authentic.” That’s great, so long as the account is authentic, but what if, one day, it suddenly isn’t?
An attacker that can wrestle a verified account from its owner can cloak themselves in the real owner’s authenticity. And they can use that authenticity to pull off what NBC News reporter Kevin Collier described as “the best DM phishing attempt I think I’ve ever seen.” The attack, seen by Collier and attempted against author Miles Klee, used a compromised blue tick account to try to scam Klee out of his own verified account.
According to the compromised account’s bio, he is…
Support Team Officer Patrick Lyons. You will be informed of an important development regarding your account via this channel.
The account sends the intended victim a Direct Message that reads:
Hello, dear Twitter user!Your blue badge Twitter account has been reviewed as spam by our Twitter team.We understand how valuable the blue badge is to you.Please appeal using the form below, otherwise your blue badge may be deleted.{redacted URL}ThanksTwitter Team
The phishing site
The URL uses a realistic-looking domain (registered in November 2021), that displays a realistic login screen that uses the appropriate Twitter fonts and styling.
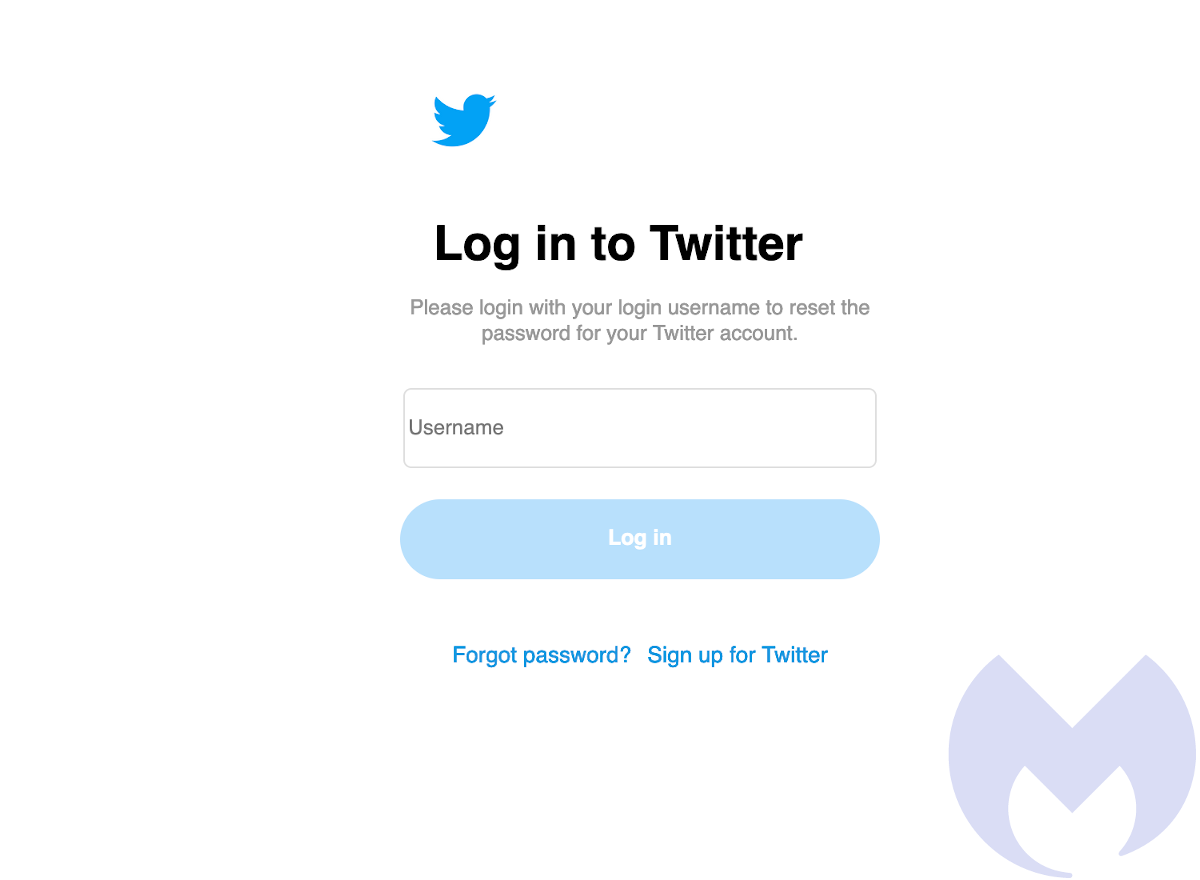
Entering a user name and clicking the “Log in” button takes the user to a realistic-looking fake password reset page.
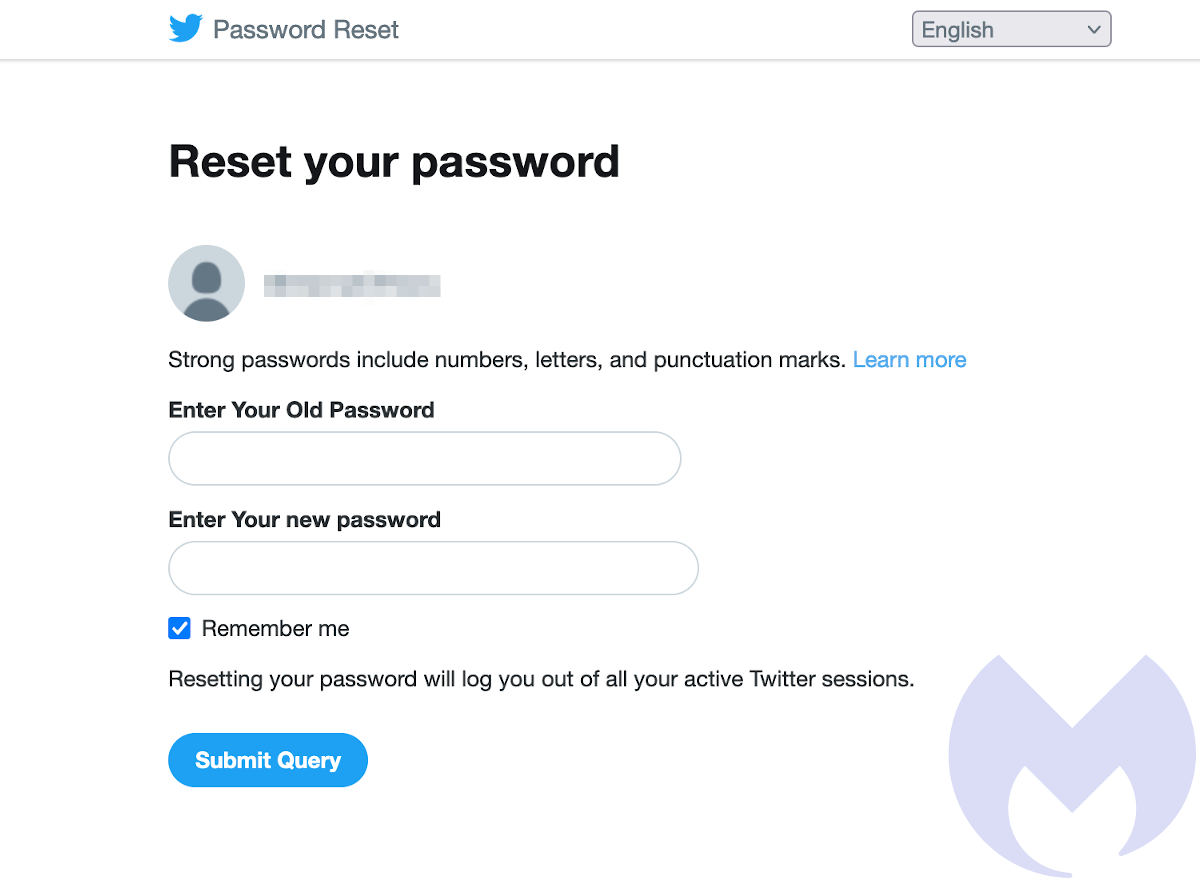
This page asks users to reset their passwords, by entering both old and new. Entering your old password gives your password straight to the scammers, who already have your username. And whether you enter a valid password or not, you see the same message:
You entered your old password incorrectly, please check and try again. If you do not know your password, you can renew your password from your Twitter account.
At this point, your password is in the hands of the scammers, but the site does not ask for a second authentication factor. The “burner” account we tested the site with had two-factor authentication (2FA)enabled and it looks as if that is enough to blunt this attack.
Don’t risk giving scammers your authority
Messages sent from verified accounts appear more authentic, which is why they are such a prize for scammers. Right now, hijacked verified profiles are enormously popular for hawking NFT scams, for example. Verified account owners can give their security a huge boost, just by enabling 2FA.
Better yet, Twitter could give every verified account a huge security boost by making 2FA mandatory.
Remain vigilant, and stay safe!










