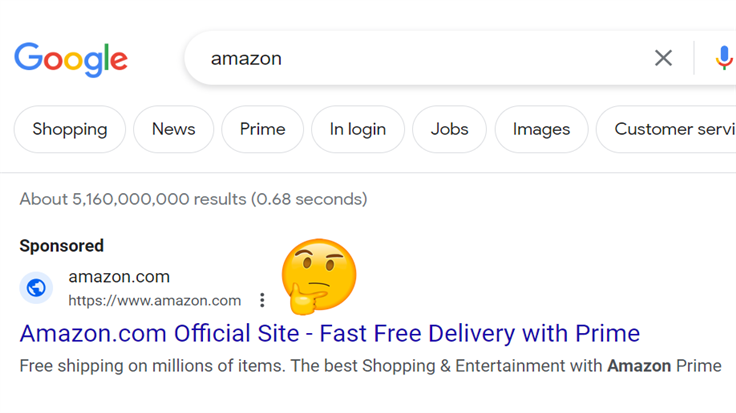
Malvertising made a resurgence in 2023, with cybercriminals creating malicious ads and websites imitating Amazon, TradingView, and Rufus.
Tag: amazon
“Amazon got hacked” messages are a false alarm
A message about extra delivery addresses getting added to Amazon accounts has gone wild on social media. Luckily, it’s nothing to worry about.
Amazon in-van delivery driver footage makes its way online
Footage from technology used to monitor Amazon delivery drivers is leaking onto the internet. AI-enabled equipment which keeps an eye on…
Malvertising via brand impersonation is back again
Web search is about to embark on a new journey thanks to artificial intelligence technology that online giants such as Microsoft and Google…
Fake Amazon Prime email abuses LinkedIn’s URL shortener
Over the last few days, scammers have been sending out phishing mails that disguise bogus URLs with something called Slinks—shortened Linkedin…
New streaming ad technology plays hide-and-seek with gamers
A new form of digital advertising is looking to make its way to you courtesy of video gaming. However, there’s a…
Ring shares data with police without consent (but it’s in good faith), says Amazon
Ring, the Amazon-owned company behind the popular smart doorbells, has admitted to giving doorbell data to law enforcement willy-nilly. All they…
Amazon Photos vulnerability could have given attackers access to user files and data
Amazon has patched a flaw in the Amazon Photos app which could have allowed an attacker to steal and use a…
De-Googling Carey Parker’s (and your) life: Lock and Code S03E06
Three years ago, a journalist for Gizmodo named Kashmir Hill wanted to understand what life was like without “Big Tech.” Far…
Securitas breached, 3TB of airport employee records exposed
An unsecured AWS server, found open to the public Internet, is the root cause of a huge compromise of data of…