The king of tricks is dead. Long live the new king. Or will it make a comeback? While we already assumed…
Tag: dyreza
Threat spotlight: Conti, the ransomware used in the HSE healthcare attack
On the 14th of May, the Health Service Executive (HSE), Ireland’s publicly funded healthcare system, fell victim to a Conti ransomware…
TrickBot adds new trick to its arsenal: tampering with trusted texts
Researchers from Dell Secureworks saw a new feature in TrickBot that allows it to tamper with the web sessions of users…
TrickBot comes up with new tricks: attacking Outlook and browsing data
Last year, we reported on a new modular malware called TrickBot that uses a network protocol similar to Dyreza. The malware was…
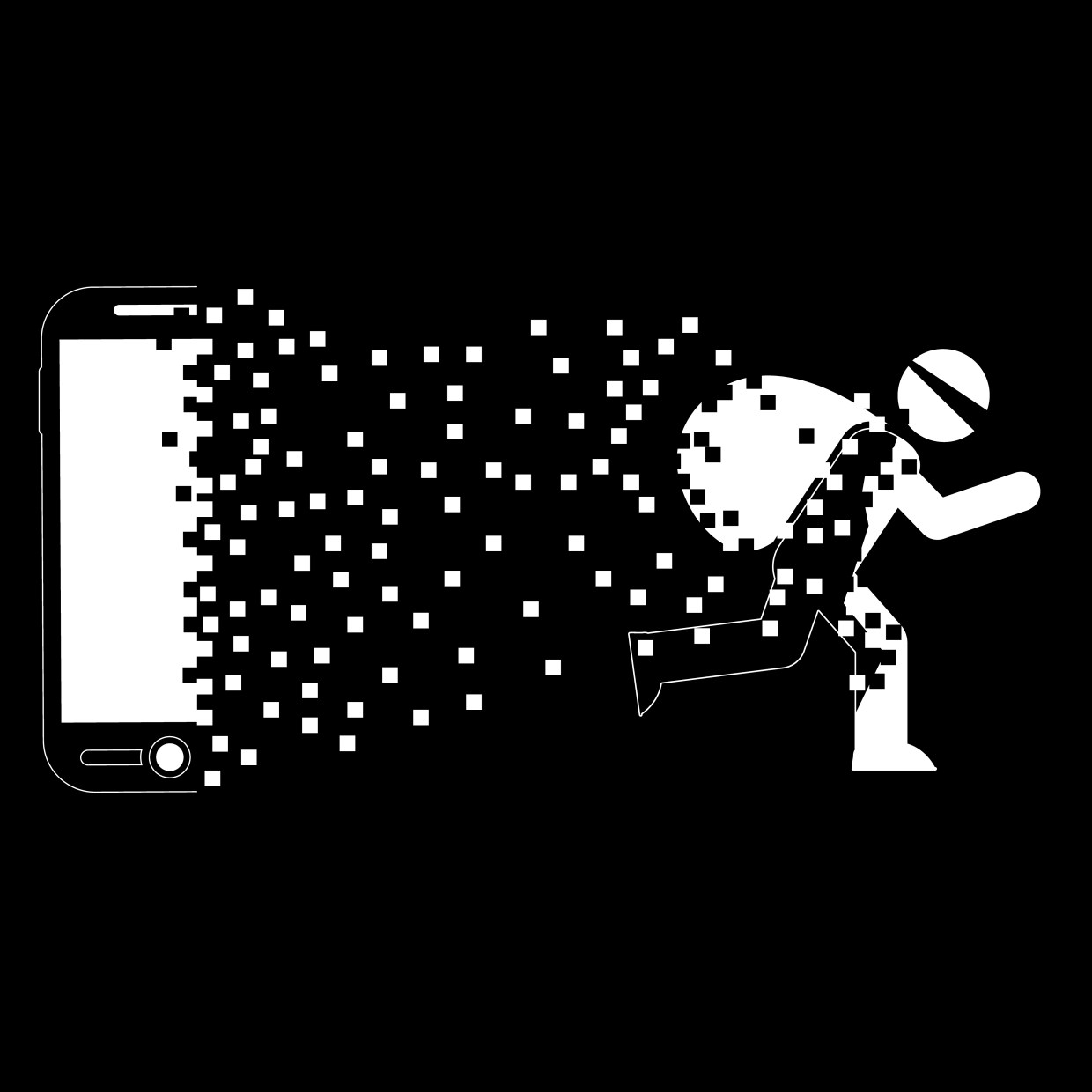
Introducing TrickBot, Dyreza’s successor
Recently, our analyst Jérôme Segura captured an interesting payload in the wild. It turned out to be a new bot that,…
A Technical Look At Dyreza
In a previous post we presented unpacking 2 payloads delivered in a spam campaign. A malicious duet – Upatre (malware downloader)…
Unpacking Fraudulent “Fax”: Dyreza Malware from Spam
This post describes the process of unpacking a malware delivered in a spam campaign. The described sample has been delivered on…