A version of this article originally appeared in Forbes on February 12, 2020. Consumerization: The specific impact that consumer-originated technologies can…
Tag: enterprise
Securing the MSP: best practices for vetting cybersecurity vendors
Ironically, to keep costs low for their enterprise and mid-market clients, managed service providers (MSPs) are some of the most reliant…
Making the case: How to get the board to invest in higher education cybersecurity
Security leaders in institutions of higher education face unique challenges, as they are charged with keeping data and the network secure,…
Enterprise incident response: getting ahead of the wave
Enterprise defenders have a tough job. In contrast to small businesses, large enterprise can have thousands of endpoints, legacy hardware from…
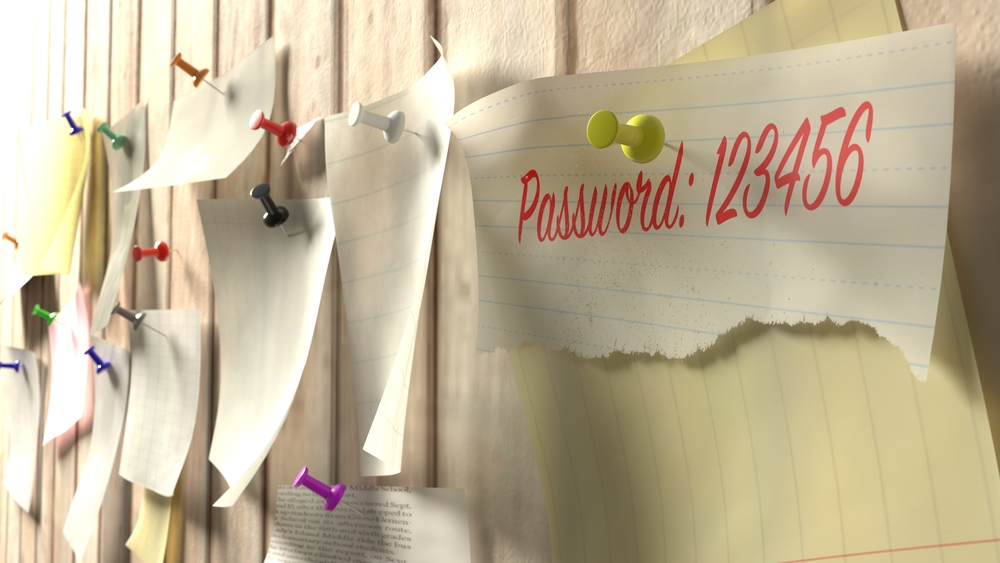
Are hackers gonna hack anymore? Not if we keep reusing passwords
Enterprises have a password problem, and it’s one that is making the work of hackers a lot easier. From credential stuffing…
Phishes, pseudophishes, and bad email
Everyone knows about phishing. We’ve all heard that the solution to phishing is to educate the user as, after all, it…
OWASP top ten – Boring security that pays off
There’s a lot of very unique, creative, and devastating cyber threats out there. The first inclination of a defender is to…
New Mac OS X remediation offering and forensics capabilities for enterprise
At Malwarebytes, our mission is to protect consumers and businesses from the most dangerous cyber threats. Today, we announced a new…