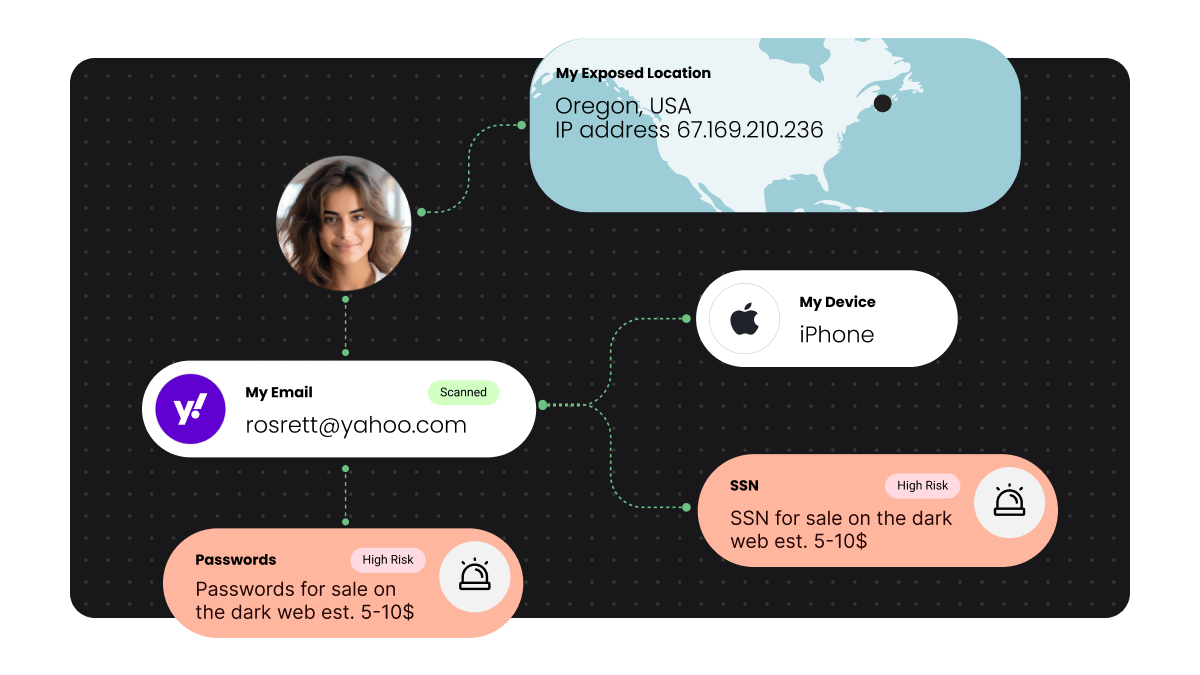
Find out what sensitive data of yours is exposed online today with our new, free Digital Footprint Portal.
Tag: hackers
Call of Duty cheats can expect embarrassment with new anti-cheat feature
In-game cheats are about to have an even harder time of things in triple AAA titles such as Call of Duty….
Looking over your shoulder: when small mistakes have big consequences
People up to no good get themselves caught in an endless number of ways. This has always been the case in…
A week in security (Oct 25 – Oct 31)
Last week on Malwarebytes Labs Other cybersecurity news Stay safe, everyone!
The 3 biggest threats reaching for your antivirus software’s off switch
Having antivirus (AV) software on your computer is a staple. Modern antivirus offers layered protection—a cybersecurity approach that uses multiple techniques…
The Olympics: a timeline of scams, hacks, and malware
The 2020 Olympics are, after a bit of a delayed start, officially in full swing. So too is the possibility for…
A week in security (June 28 – July 4)
Last week on Malwarebytes Labs: Other cybersecurity news Stay safe, everyone!
A week in security (June 7 – June 13)
Last week on Malwarebytes Labs: Other cybersecurity news Stay safe, everyone!
A week in security (February 1 – February 7)
Last week on Malwarebytes Labs, we dug into a load of security events. We first peered into how Fonix ransomware was…
Lock and Code S1Ep21: Lesson planning your school’s cybersecurity with Doug Levin
This week on Lock and Code, we discuss the top security headlines generated right here on Labs and around the Internet….