Threat actors often compete for the same resources, and this couldn’t be further from the truth when it comes to website…
Tag: magento
A look at a Magecart skimmer using the Hunter obfuscator
Threat actors are notorious for trying to hide their code in various ways, from binary packers to obfuscators. On their own,…
A week in security (February 14 – February 20)
Last week on Malwarebytes Labs: And don’t forget to listen to our recent podcast about the world’s most coveted spyware, Pegasus….
Adobe patches actively exploited Magento/Adobe Commerce zero-day
Adobe has released an emergency advisoryfor users of its Commerce and Magento platforms. It explains that a critical zero-day vulnerability is…
A new Magecart campaign is making waves
Malwarebytes’ researchers are closely monitoring web skimmers and have noticed that one of the infamous Magecart groups is causing a rise…
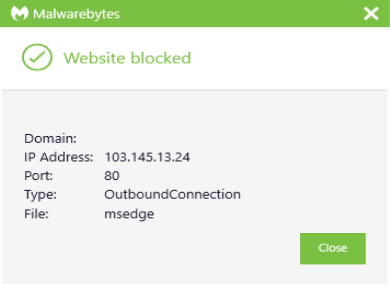
Credit card skimmer evades Virtual Machines
This blog post was authored by Jérôme Segura There are many techniques threat actors use to slow down analysis or, even…
Credit card skimmer piggybacks on Magento 1 hacking spree
Back in the fall of 2020 threat actors started to massively exploit a vulnerability in the no-longer maintained Magento 1 software…
Credit card skimmer masquerades as favicon
Malware authors are notorious for their deceptive attempts at staying one step ahead of defenders. As their schemes get exposed, they…
Fraudsters cloak credit card skimmer with fake content delivery network, ngrok server
Threat actors love to abuse legitimate brands and infrastructure—this, we know. Last year we exposed how web skimmers had found their…
Magecart criminals caught stealing with their poker face on
Earlier in June, we documented how Magecart credit card skimmers were found on Amazon S3. This was an interesting development, since…