GuLoader, a perennial favourite of email-based malware campaigns since 2019, has been seen in the wild once again. GuLoader is a downloader…
Tag: malspam
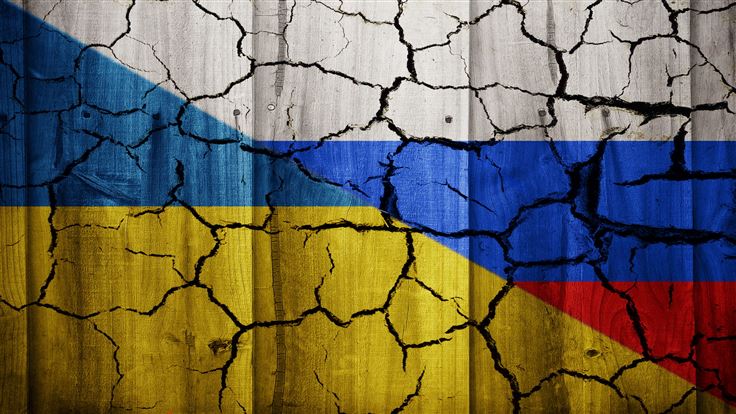
FormBook spam campaign targets citizens of Ukraine️
Our Threat Intelligence team has been closely monitoring cyber threats related to the war in Ukraine. Today, we discovereda malicious spam…
Dridex affiliate dresses up as Scrooge
Threat actors are hoping to catch a few more victims before they leave work for the Christmas holidays. The recent malicious…
TrickBot helps Emotet come back from the dead
Probably one of the best known threats for the past several years, Emotet has always been under intense scrutiny from the…
LemonDuck no longer settles for breadcrumbs
LemonDuck has evolved from a Monero cryptominer into LemonCat, a Trojan that specializes in backdoor installation, credential and data theft, and…
A week in security (July 5 – July 11)
Last week on Malwarebytes Labs: Other cybersecurity news: Stay safe, everyone!
Malspam banks on Kaseya ransomware attack
The Malwarebytes Threat Intelligence Team recently found a malicious spam campaign making the rounds and banking on the ransomware attack that…
The most enticing cyberattacks of 2020
This is part one of a two-part series. To read about the strangest cybersecurity events of 2020, read our second story…
QBot Trojan delivered via malspam campaign exploiting US election uncertainties
This blog post was authored by Jérôme Segura and Hossein Jazi. The 2020 US elections have been the subject of intense…
Malspam campaign caught using GuLoader after service relaunch
They say any publicity is good publicity. But perhaps this isn’t true for CloudEye, an Italian firm that claims to provide…