Google has announced the strengthening of safeguard measures for its Workspace customers. You may well be using Workspace without realising it. If…
Tag: protection
How to protect your child’s identity
We all know identity theft in adults is a serious problem, but how much do you consider your child’s identity? Identity…
TikTok faces $28m fine for failing to protect children’s privacy
TikTok is no stranger to controversy where data usage is concerned. Back in 2021, the social media dance extravaganza platform agreed to pay…
Why MITRE matters to SMBs
Running a small- to medium-sized business (SMB) requires expertise in everything, from marketing and sales to management and hiring, but in…
MITRE ATT&CK® Evaluation results: Malwarebytes’ efficiency, delivered simply, earns high marks
Cybersecurity can be complex work, as security teams need to regularly decipher and prioritize alerts, protect against daily threats, and possibly…
Ryuk ransomware attacks businesses over the holidays
While families gathered for food and merriment on Christmas Eve, most businesses slumbered. Nothing was stirring, not even a mouse—or so…
Compromising vital infrastructure: transport and logistics
Back when I was a dispatcher for a courier and trucking company, we used to joke that it only took a…
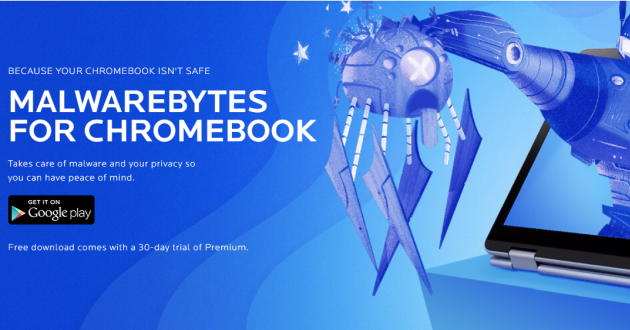
Introducing Malwarebytes for Chromebook
Have you been thinking about switching over to Chromebook because you don’t need all the built-in software programs of a PC…
Block all or nothing to prevent ICO fraud?
At Malwarebytes, we feel we have reached a point where we need to ask our customers how to proceed on the…