Sites and apps frequently gamify their products and experiences to grow their user base. It’s a relatively easy way to have…
Tag: scam
Steer clear of cryptocurrency recovery phrase scams
The dangers of cryptocurrency phishing are back in the news, after tech investor Mark Cuban was reported to have lost around $870k via…
YouTube makes sweeping changes to tackle spam on Shorts videos
YouTube is rolling out unclickable links. Video portals like YouTube have had to deal with spam comments and bogus links for…
Plane sailing for ticket scammers: How to keep your flight plans safe
You may be getting ready to jump on a plane and head off for a few days or weeks of rest…
“Free” Evil Dead Rise movie scam lurks in Amazon listings
Scammers are using a novel technique with Amazon listings to trick fans of Evil Dead into downloads they may not want,…
UPS warns customers of phishing attempts after data accessed
UPS Canada is warning customers in Canada of potential data exposure and the risk of phishing. People have started to receive…
Phishing scam takes $950k from DoorDash drivers
A particularly nasty slice of phishing, scamming, and social engineering is responsible for DoorDash drivers losing a group total of around…
Fake security researchers push malware files on GitHub
Researchers from VulnCheck have observed a campaign using real security researchers as bait for malware. The campaign goes to some lengths…
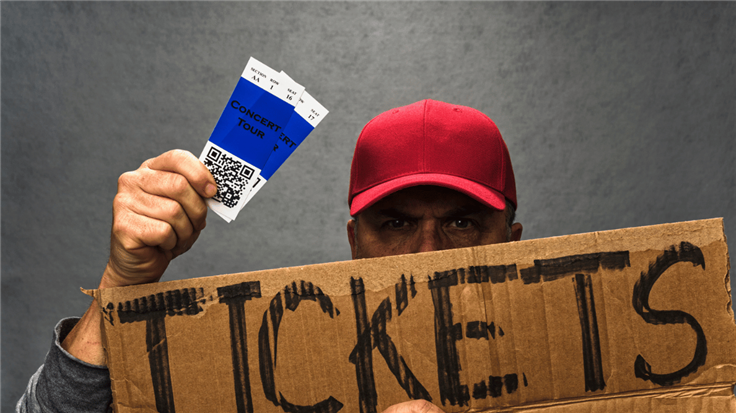
Ticket scammers target Taylor Swift tour
Taylor Swift fans are being warned to be cautious when buying tickets for her current “Eras” tour, with scammers waiting in…
GuLoader returns with a rotten shipment
GuLoader, a perennial favourite of email-based malware campaigns since 2019, has been seen in the wild once again. GuLoader is a downloader…