We’ve seen a particular card skimming campaign really pick up pace lately. With hundreds of stores compromised, you may come across it if you shop online this holiday season.
Tag: skimmers
Credit card skimmer evades Virtual Machines
This blog post was authored by Jérôme Segura There are many techniques threat actors use to slow down analysis or, even…
q-logger skimmer keeps Magecart attacks going
This blog post was authored by Jérôme Segura Although global e-commerce is continuing to grow rapidly, it seems as though Magecart…
The many tentacles of Magecart Group 8
This blog post was authored by Jérôme Segura During the past couple of years online shopping has continued to increase at…
Lil’ skimmer, the Magecart impersonator
This blog post was authored by Jérôme Segura A very common practice among criminals consists of mimicking legitimate infrastructure when registering…
Lock and Code S1Ep17: Journalism’s role in cybersecurity with Alfred Ng and Seth Rosenblatt
Most everything about cybersecurity—the threats, the vulnerabilities, the breaches and the blunders—doesn’t happen in a vacuum. And the public doesn’t learn…
Inter skimming kit used in homoglyph attacks
As we continue to track web threats and credit card skimming in particular, we often rediscover techniques we’ve encountered elsewhere before….
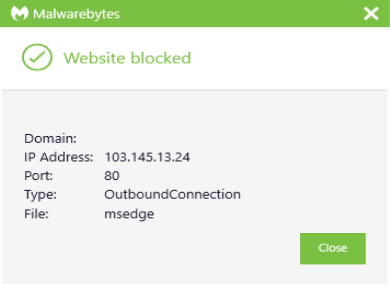
Web skimmer hides within EXIF metadata, exfiltrates credit cards via image files
They say a picture is worth a thousand words. Threat actors must have remembered that as they devised yet another way…
Online credit card skimming increased by 26 percent in March
Crisis events such as the current COVID-19 pandemic often lead to a change in habits that captures the attention of cybercriminals….
Fraudsters cloak credit card skimmer with fake content delivery network, ngrok server
Threat actors love to abuse legitimate brands and infrastructure—this, we know. Last year we exposed how web skimmers had found their…