UPS Canada is warning customers in Canada of potential data exposure and the risk of phishing. People have started to receive…
Tag: smishing
A week in security (October 3 – 9)
Last week on Malwarebytes Labs: Stay safe!
Huge increase in smishing scams, warns IRS
The Internal Revenue Service (IRS) has issued a warning for taxpayers about a recent increase in IRS-themed smishing scams aimed at stealing…
FCC warns of steep rise in phishing over SMS
After the FCC (Federal Communications Commission) made a huge splash weeks ago when it told Google and Apple to pull TikTok from their…
“A little gift for you” SMS spam appears to come from your own phone number
If you’ve received a spam SMS message sent from your own phone number, don’t panic. No, you weren’t hacked. And you’re…
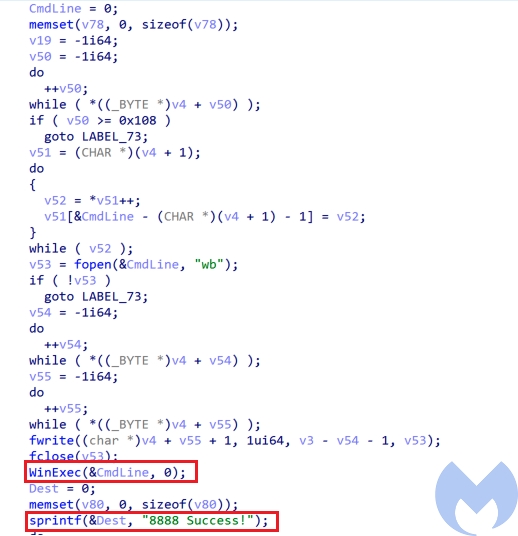
Android malware BRATA can wipe devices
Cleafy, a cybersecurity firm specializing in online fraud, has published new detailsabout banking Trojan BRATA (Brazilian Remote Access Tool, Android), a…
Italian mafia cybercrime sting leads to 100+ arrests
The Spanish National Police (Policía Nacional) has successfully dismantled an organized crime ring of hundreds of members in a sting operation…
A week in security (August 2 – August 8)
Last week on Malwarebytes Labs: Other cybersecurity news: Stay safe!
Royal Mail phish deploys evasion tricks to avoid analysis
Royal Mail phish scams are still in circulation, slowly upgrading their capabilities with evasion tools deployed in far more sophisticated malware…
What is Smishing? The 101 guide
Smishing is a valuable tool in the scammer’s armoury. You’ve likely run into it, even if you didn’t know that is…