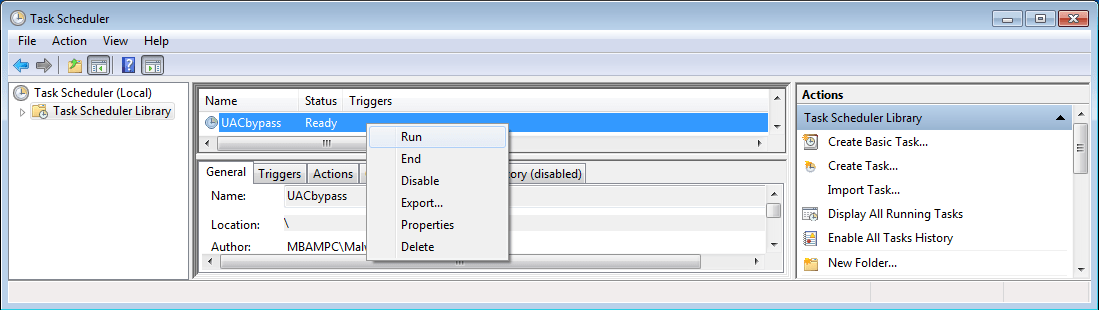
Many years ago, I wrote a little batch file to find and delete Scheduled Tasks added by an adware variant called…
Tag: the more you know
Logging In and Captcha
What is Captcha? CAPTCHA (“Completely Automated Public Turing test to tell Computers and Humans Apart”) is one of the annoyances that…
Goodbye CD Wallet. Hello ISOSTICK!
The ISOSTICK is a USB stick that masquerades as an external CD/DVD drive and loads ISOs from a removable MicroSD card. Many of…
What are Online Problematic Situations: EU Kids Speak Up
The London School of Economics and Political Science, in partnership with the EU Kids Online Network, published a long white paper…
Automating Malware Analysis with Cuckoo Sandbox
Analyzing malware can be a lengthy process. Malware today can be simple, like something that downloads another program from a rogue…
A Week in Security (April 20 – 26)
Below is a bird’s-eye-view of blogs we published last week followed by top security news. As much as possible, we don’t…
25 Years and our computers are still…
Today, Ars Technica posted an article looking back 25 years ago to when the Nintendo Game Boy was first released. I…
CanSecWest: Day 2 Recap
Day two of annual CanSecWest conference started bright and early, and when I say bright I mean it. In an uncharacteristic weather…
Android Botnets Hop on the TOR Train
Botnet creators have attempted numerous tactics for hiding their presence, traffic and locations of their command and control (CnC) servers. To…
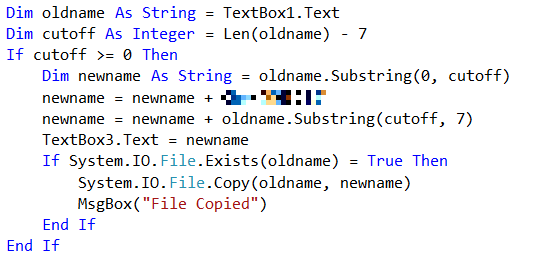
The RTLO method
After my post about extensions, I received some requests to deal with another method of pretending to be a different type…