What are file extensions? A file extension (or simply “extension”) is the suffix at the end of a filename that indicates…
Tag: the more you know
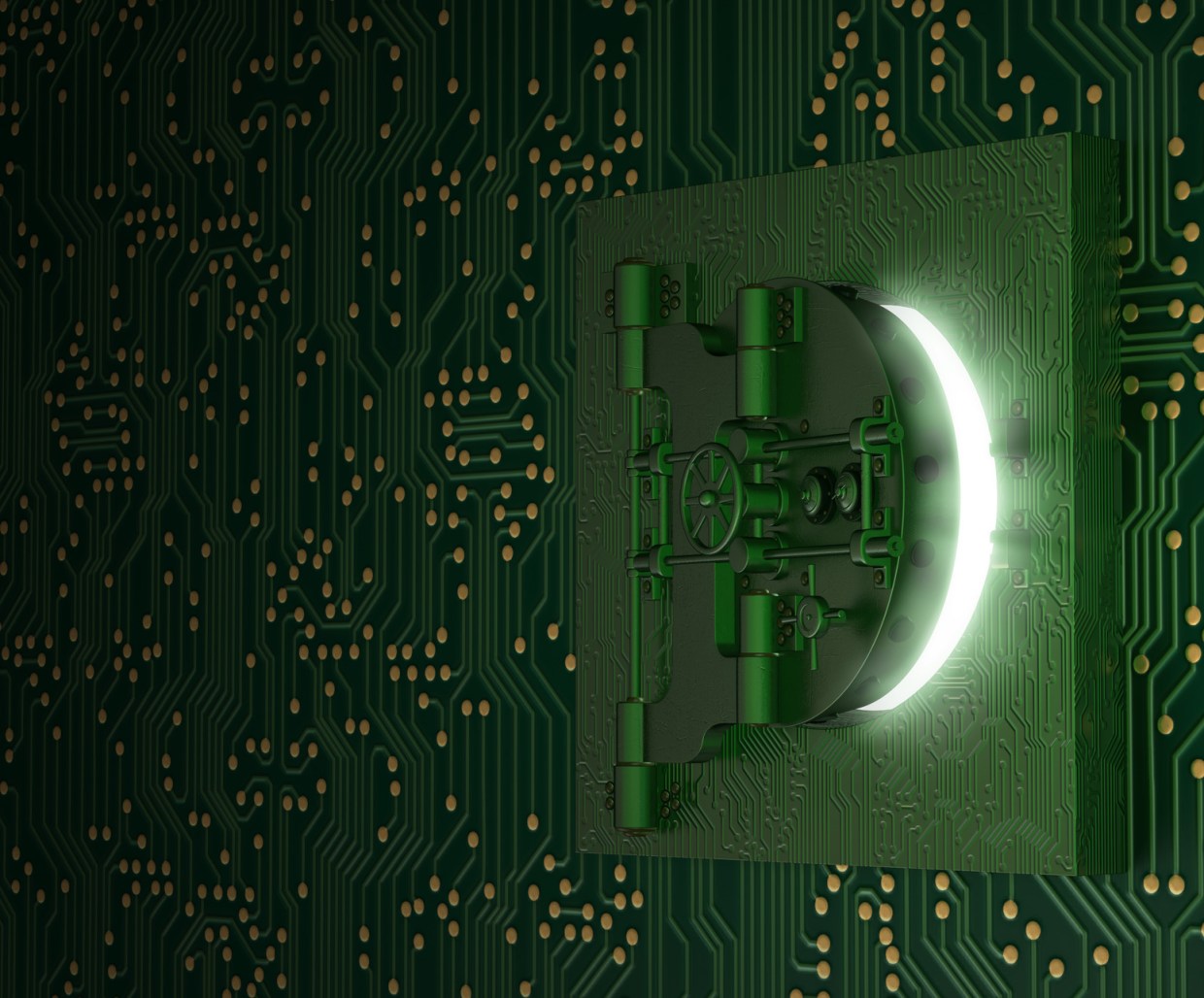
Security: Finding the balance
Finding the balance between security and ease of use. A computer system, or almost anything else for that matter, can never…
World’s first Bitcoin ATM comes to Canada
Bitcoin, the famous digital currency which has sparked much controversy over the years, is now heading to an ATM near you. The…
Money Mules, If it looks too good to be true…
It is a sad state of affairs, but email is still a viable attack vector for the bad guys, and today…
Chrome’s Solution to the Unsavvy Poses A Potential Risk
Don’t get me wrong, I love Chrome, I think it’s a fantastic browser and has a great track record of protecting…
Hiding in plain sight
A lot of programs we install on our computer are automatically run when Windows starts and loads. While this is not…
Phishing is for the birds
One of the largest threats facing users today is from Phishing attacks, or social engineering attempts at getting the average person…
It’s National Cyber Security Awareness Month! So be aware of an IE 0-Day!
This month marks the 10th Anniversary of National Cyber Security Awareness Month, or NCSAM, here in the United States and hopefully…
In computers, are random numbers really random?
Sometimes it is necessary to use random numbers in programs. Depending on the need, it can be important how random the…
Encryption: types of secure communication and storage
After supplying you with examples on how to encrypt your mail and how to encrypt files and folders I would like…