Update (12:34 PM): Web security firm Sucuri has already detected in the wild attempts to load remote shells onto servers using the #bashbug. Shells can allow attackers to take remote control of web servers and use them for various purposes.
It would have been hard to imagine anything as bad as the HeartBleed bug was going to happen but the recent discovery of a flaw in the popular bash command shell very well could be.
Bash is used as the command interpreter for many Linux systems including Red Hat, CentOS, Ubuntu and Debian and ships with Mac OS X.
The vulnerability which was quickly nicknamed ‘shellshock’ was discovered by Stéphane Chazelas and assigned CVE-2014-6271.
It allows anyone to execute arbitrary code by abusing an environment variable and launching a function containing trailing commands.
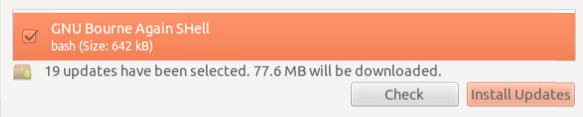
While patches have been issued, system administrators will be working long shifts to go through every single server, router and other piece of equipment that uses the bash shell.
It is a race against time as proof of concept code in the form of a metasploit module is already available meaning the bad guys are hard at work trying to hack into affected systems.
In fact the vulnerability is so severe it has been assigned a score of 10 and yet is almost trivial to adapt and use for nefarious purposes.
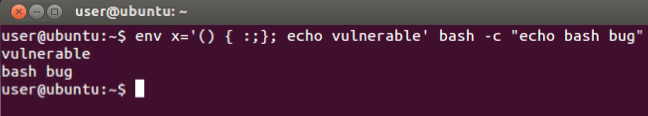
To verify if your system is vulnerable, you can type the following command:
env x='() { :;}; echo vulnerable' bash -c "echo bash bug"If it displays something like this: