In mid August, the actors behind some of the recent malvertising campaigns we documented on this blog before started to come out with several new tricks to fly under the radar and yet expose tens of millions of users to malware.
Without a doubt, the increased scrutiny on malvertising and ad networks has forced malicious actors to revise how they go about their business, a critical part in driving victims to exploit kits for the purpose of compromising their systems.
The malvertising campaign we are exposing leveraged several top ad networks, as well as many more smaller ones. Despite its large scope and impact, it ran mostly uninterrupted for almost three weeks, according to telemetry data we were able to mine once we uncovered the scheme.
The threat actors responsible for this attack devised a cunning plan to pose as legitimate advertisers and employed stealthy and advanced techniques to hide malicious traffic redirections so well that they evaded most detection systems.
The ultimate goal of this plan was to compromise the computers of millions of users browsing popular websites by covertly redirecting their browsers to the Angler Exploit Kit, the most advanced tool used in drive-by download attacks.
Bogus (but clean) adverts
Malicious actors registered to various ad platforms posing as legitimate advertisers and submitted their creatives (shown below) through Real Time Bidding.
The companies they were purporting to represent appeared legitimate on the surface, with websites registered years ago with even some listed in the Better Business Bureau registry. This decoy worked well enough to fool many ad networks with direct ties to the major ones in the online ad industry.
The ads themselves were loaded directly from the rogue advertisers’ websites, which, as we will see it later, was part of the problem in compromising the advertising chain. However it is worth mentioning that the ads themselves were not booby trapped at all, which again made it more difficult to spot something suspicious.

Top publishers affected
The list of affected publishers is quite long, but here are the most notable ones, sorted by traffic (monthly visits according to SimilarWeb):
| Site name | Traffic | Site name | Traffic | |
| ebay.co.uk | 139M | nuvid.com | 51.50M | |
| drudgereport.com | 61.30M | upornia.com | 35.80M | |
| answers.com | 53.8M | eroprofile.com | 15.60M | |
| wowhead.com | 27.8M | pornyeah.com | 10.60M | |
| ehowespanol.com | 20.30M | iceporn.com | 7.50M | |
| legacy.com | 18.4M | streamsexclips.com | 5M | |
| newsnow.co.uk | 15.50M | xbabe.com | 4.40M | |
| talktalk.co.uk | 11.10M | |||
| manta.com | 9.8M |
Ad networks
This campaign took advantage of some of the biggest ad networks in the industry, but also smaller players.
- DoubleClick (ad-emea.doubleclick.net)
- AppNexus (fra1.ib.adnxs.com)
- engage:BDR (delivery.first-impression)
- ExoClick (syndication.exoclick.com)
- adk2x.com
- rtbfy.com
- ecpmrocks.com
- teracreative.com
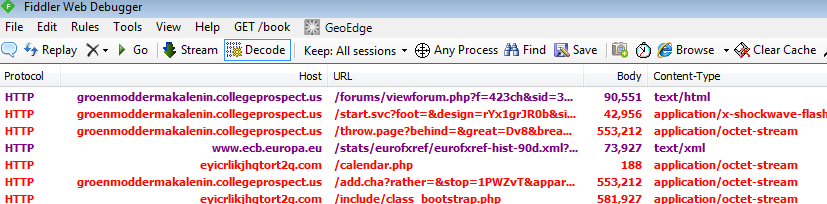
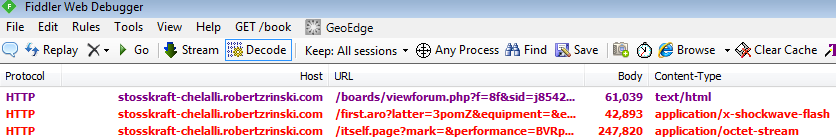
Stealthy and efficient redirection flow
To better understand how this particular malvertising campaign works, we designed the following chart. The techniques used are similar to previous ones, but great care was put on masquerading as legitimate advertisers and avoiding detection by encrypting traffic and using various advanced tricks.
We also noticed the use of URL shorteners, as well as a custom API to perform the redirection to the Exploit Kit landing pages.
Angler Exploit Kit
As was the case with past malvertising attacks, the Angler Exploit Kit was used to convert incoming web traffic into infected machines. We observed Angler loading Bedep and pushing 2 payloads:
and the regular Angler with the single payload:
In both cases, we saw the usual suspects: ad fraud and ransomware with most exploit attempts occurring in the US and the UK.
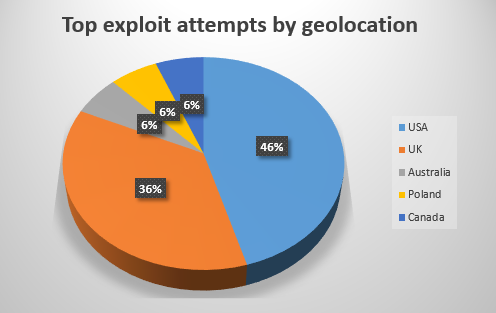
Top five countries where users landed on Angler EK for this campaign, as per our telemetry.
Evolution of malvertising
While malvertising has made headlines during the past few months, the attacks that are documented publicly are only the tip of the iceberg. There are some campaigns that are so advanced that no one will ever see or hear about them, which is exactly what threat actors are hoping for.
In this cat and mouse game, the initiators will always have the advantage, that window of opportunity to distribute malware before their scheme is exposed.
This particular case is a good illustration of why screening advertisers is so important, especially when they are allowed to host and serve the ad content themselves. The ad could be clean or booby trapped, but the rogue actors are in full control of the delivery platform and can instruct it to perform nefarious actions that will easily bypass most security checks.
Ad networks have been informed and have taken the necessary steps to stop this campaign but we will continue to monitor the situation to detect potential changes or migration into other ad networks.
Malwarebytes Anti-Exploit users were already protected against the Angler Exploit Kit. We’d also like to remind our readers that outdated software is the number one cause for infections via web exploits and a major reason why malvertising continues to be an extremely viable infection mechanism for cyber criminals. This is why patching machines and having anti-exploit mitigation software is so important.










