The popular Google Chrome browser has some of the best security tools baked in with features such as Safebrowsing which protects users from malicious websites. By extension, ChromeOS which powers the affordable Chromebooks is indeed one of the safest systems one can get these days.
Even though the surface of attack is smaller than that of a typical Windows PC, online crooks will always find a way to abuse the system. One of the main points of entry is via rogue browser extensions which are increasingly becoming a problem and are being leveraged in various types of attacks ranging from data theft, spying, pop up ads and more.
Chrome extensions are very much like Android Apps as they require certain permissions (access to your contacts, microphone, camera, etc…) and unfortunately more often than not, they require more rights than they ought to have. Additionally, a lot of people don’t really understand what those mean and will install these extensions and forget about them.
This makes it an ideal situation for threat actors to aggressively push bogus apps and use a little bit of social engineering to coerce end users into downloading malware laden extensions.
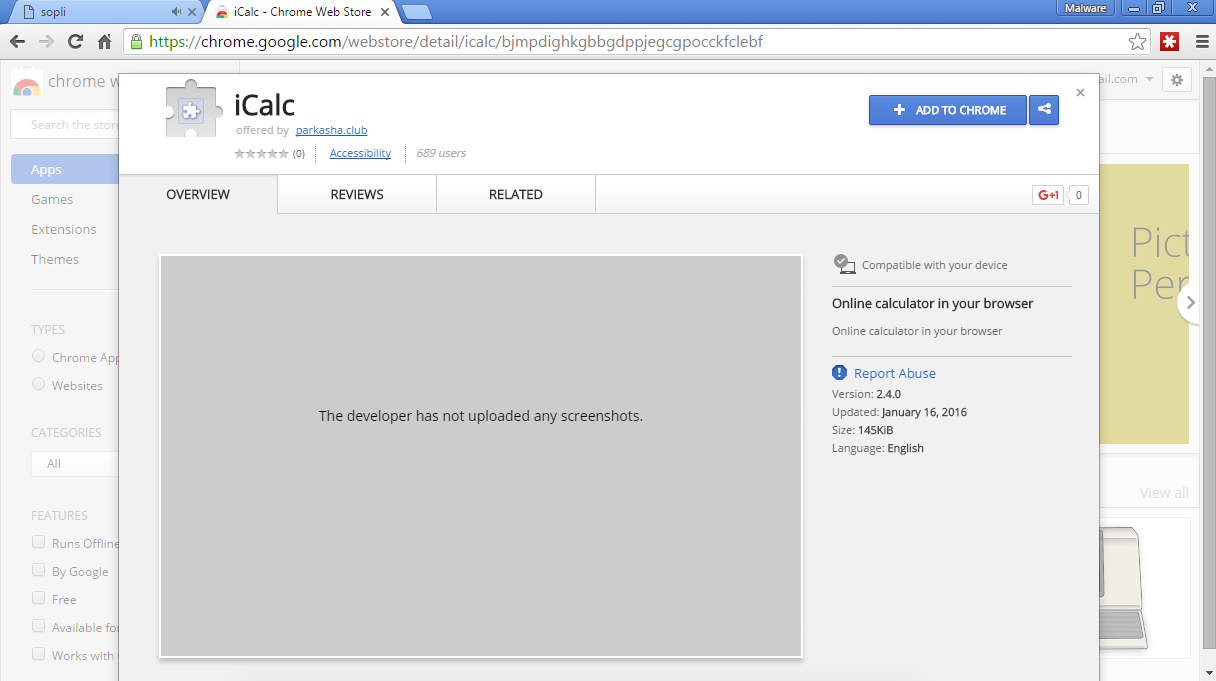
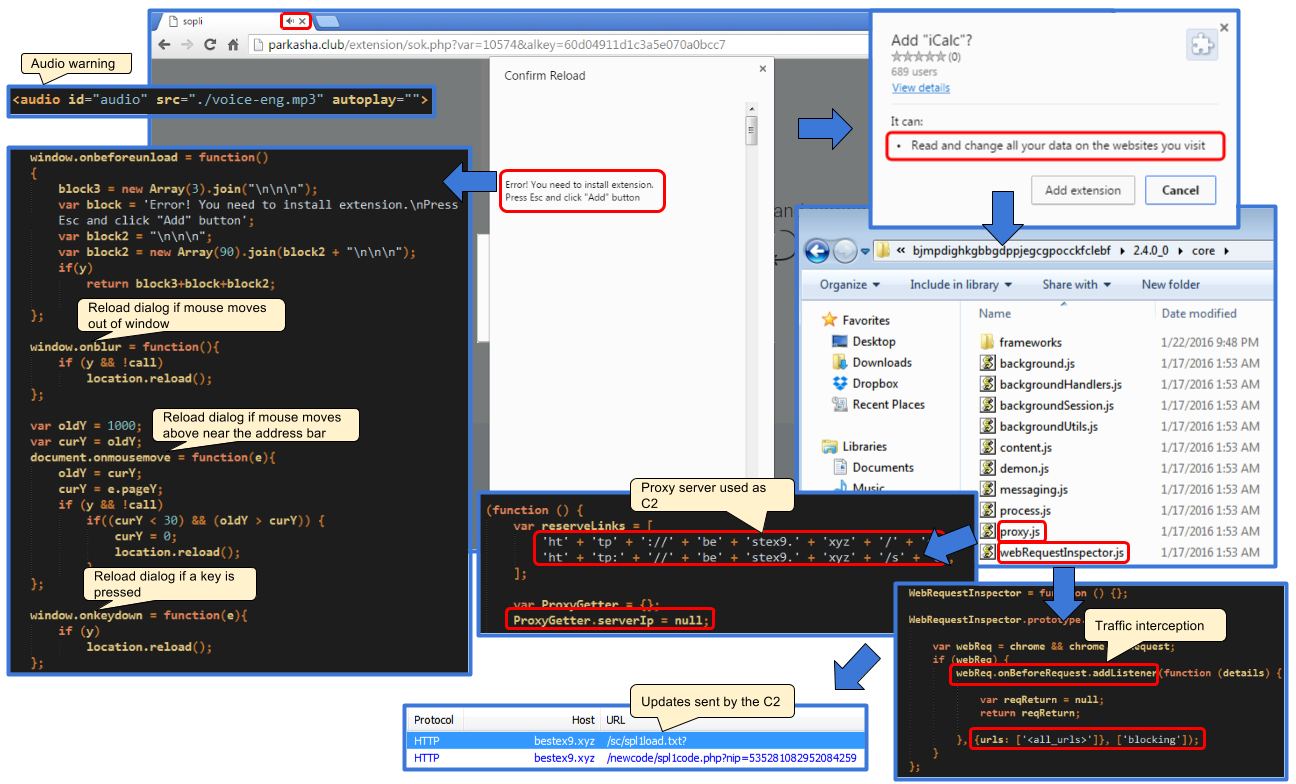
Case in point, we recently came across a malvertising incident pushing a site forcing us to install a Chrome extension called iCalc. There was no clean way of closing the window and refusing to install this program. As soon as the user moved the mouse close to the address bar or near the close button, an annoying dialog accompanied by a stern audio message would pop up.
[youtube https://youtu.be/xlVcWQzg1P8]
This extension had some telltale signs of being malicious beyond its aggressive distribution method. Although it was listed in the Chrome store, it had no screenshot information or reviews.
It also required invasive permissions (Read and change all your data on the websites you visit) for being a calculator:
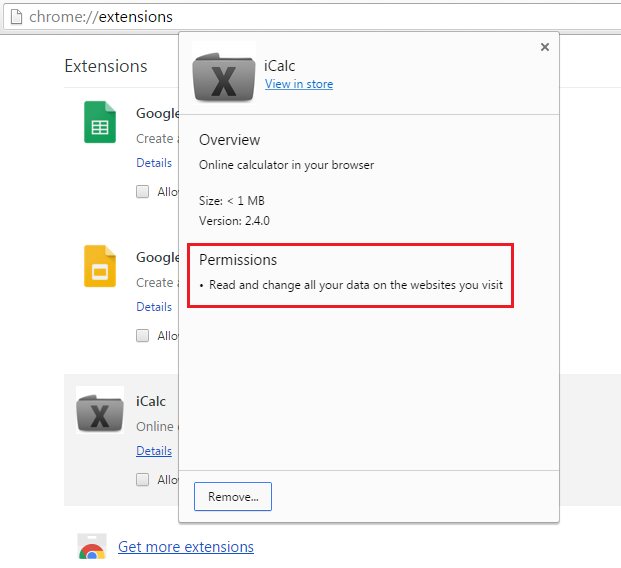
A closer look at this app confirmed our suspicions. There was little if nothing about any calculator in there but rather a set of scripts to create a proxy and perform web requests interceptions.
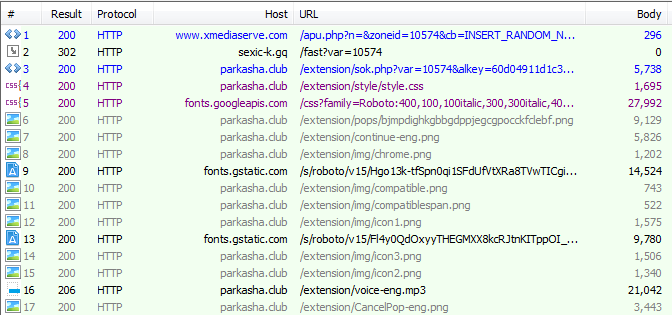
Each browser’s tab was hooked and routed through the following domain: bestex9.xyz
Registrant Name: WhoisGuard Protected Registrant Organization: WhoisGuard, Inc. Registrant City: Panama
We noticed that it silently talked back to this domain to retrieve additional commands and updates at regular intervals.
This extension was eventually pulled out of the Chrome web store after it had been downloaded close to a thousand times. Interestingly, shortly after it was removed, we observed the same malvertising campaign push out a different Chrome extension, this time aimed at Russian users before also being replaced with a redirect to a social networking website.
In addition to malware authors, a lot of adware companies are pushing rogue extensions using their usual techniques: free coupons, recipes, videos too good to be true and the like. Often times, their motivation is to harvest your browsing habits and resell them to marketing companies to target you with ads.
It’s a good idea to regularly check what extensions you have installed by simply typing chrome://extensions/ in the address bar. You can remove any that you no longer need or can’t remember where it came from.
IOCs:
- Traffic flow (malvertising):