This blog post was authored by Hasherezade
Update:
Malwarebytes #Crackme : we already have the winners in the category "the fastest solve", congratulations!
— Malwarebytes Threat Intelligence (@MBThreatIntel) October 30, 2021
1st: @nazywam
2nd: Suvaditya Sur (@x0r19x91)
3rd:@evandrix
But we are still waiting for your submissions! https://t.co/9KEAarLxpF
Update 2:
Twice in the past (2017, 2018) we’ve published a Capture-The-Flag challenge dedicated to aspiring malware analysts. Each time it was a Windows executable, containing up to 3 stages to break, in order to get the final flag. The goal of the crackme was to provide an exercise where the contestants will be able to challenge themselves in understanding and overcoming techniques commonly present in real-life malware. Yet we present them in a harmless example.
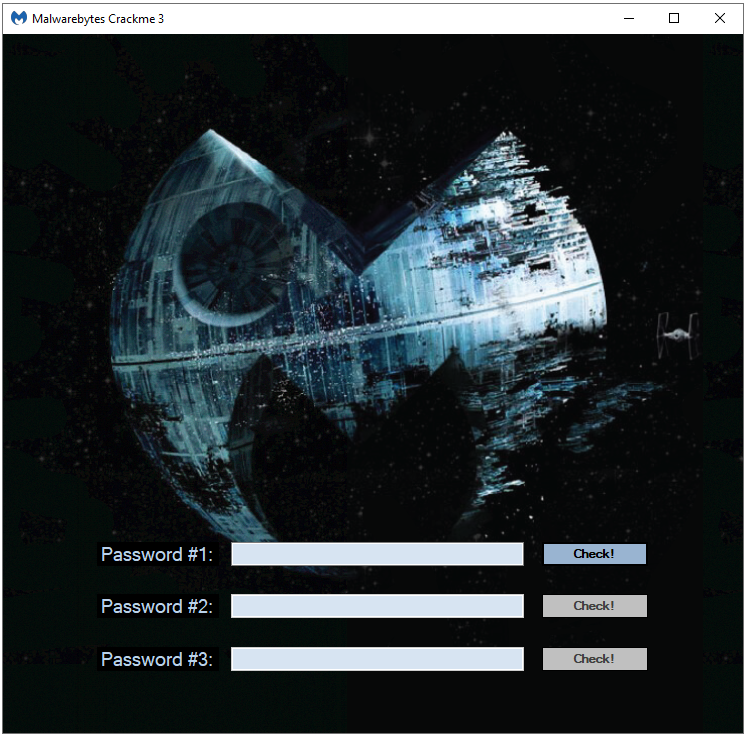
After a long break, we decided to resume our small contest, and possibly make it an annual event. Without further ado, we present you the Malwarebytes CrackMe number 3!
Rules of the contest
The rules remain mostly unchanged since the second edition. As before, we have two parallel tracks of the contest:
- The fastest solve. The three earliest submitted flags win. The flag should be submitted along with (minimal) notes about the steps taken to find it. (No detailed write-up is required.) Any updates about the known winners in this category will be appended to this post.
- The best write-up. The write-up will be judged by its educational value, clarity, and accuracy. The author should show their method of solving the CrackMe, as well as provide the explanation of the techniques used in the challenge. The write-up submissions closes two weeks after the start of the challenge.
In each track we will select three winners that will be rewarded with unique Malwarebytes swag. The first place winner in each category will additionally get any IT-related book of their choice. All the solvers are going to be listed in our hall of fame.
The flag is in format: flag{...}
Submissions to both contests should be sent as a private message to the Twitter account: @hasherezade.
Three weeks after the challenge started we will publish the closing summary, along with a detailed walk-through, provided by the author.
WARNING: We are sorry, but Malwarebytes employees and people who have access to the CrackMe before the official publication are not allowed to participate.
The application
The application is a Windows executable. It was tested on Windows 8 and above.
WARNING: please bear in mind that since the CrackMe contains techniques similar to those used in malware, it may be flagged by various AV products. It is a known false-positive. We recommend you run it on a VM, with Windows Defender disabled.
You can download it here.
Best of luck, and have fun!
Hall of fame
We already have the winners in the category “the fastest solve”:
- 🥇 @nazywam
- 🥈 Suvaditya Sur (@x0r19x91)
- 🥉 @evandrix
- 🎊 Alex Skalozub (@pieceofsummer)
- 🎊 @JLeow00
- 🎊 rainbowpigeon
- 🎊 arm4nd0
- 🎊 Matthieu Walter (@matth_walter)
- 🎊 Bahlai Vladyslav (@BaglaiVlad) & Alex Shevchuk
But you can still be included in this “Hall of fame”, just send us your solution!