Short bio
Browser extensions are computer programs that add functionality to existing browsers. They come in as many kinds (and more) as there are browsers.
Internet Explorer distinguishes between toolbars and browser helper objects (BHOs). Other browsers like Firefox, Chrome, Opera, and Safari call them add-ons or simply extensions.
For PUPs, the economically most interesting browsers are the most popular ones, e.g. Chrome, Firefox, and Internet Explorer.
History
Browser extensions (in this case BHOs) were introduced with the release of Internet Explorer 4 in 1997. The first concerns arose because of their tracking capabilities and the fact that the extensions also affected explore.exe. Other browsers give their extensions less power and are trying different approaches to stop Potentially Unwanted Programs from installing. Google warns about installing extensions that did not come from the Chrome Web Store. Firefox and Opera use blacklists to disable extensions that are found breaking the rules.
Common infection method
Browser extensions offer some added functionality to the user. With PUPs these are often advertisement supported applications. Another common infection method for browser extensions is bundled installers. These bundles are designed to install more than the user bargained for and usually include one or more browser extensions that function as adware and/or hijackers.
Associated families
There are many PUPs that use browser extensions to deliver their content. Currently most famous and widespread is Ask. It uses several subfamilies like MindSpark and Bandoo to get its toolbars installed. Other families that use extensions for more than one browser are Sanbreel/Browsefox, Crossrider, and Conduit/SearchProtect.
Remediation
Removal of browser extensions is usually not difficult in the case of PUPs. Often they have working uninstallers, and browser extensions can be easily disabled (and in some cases removed) in the browser settings themselves. In more serious infections, it may be necessary to change the passwords you used while you were online.
Aftermath
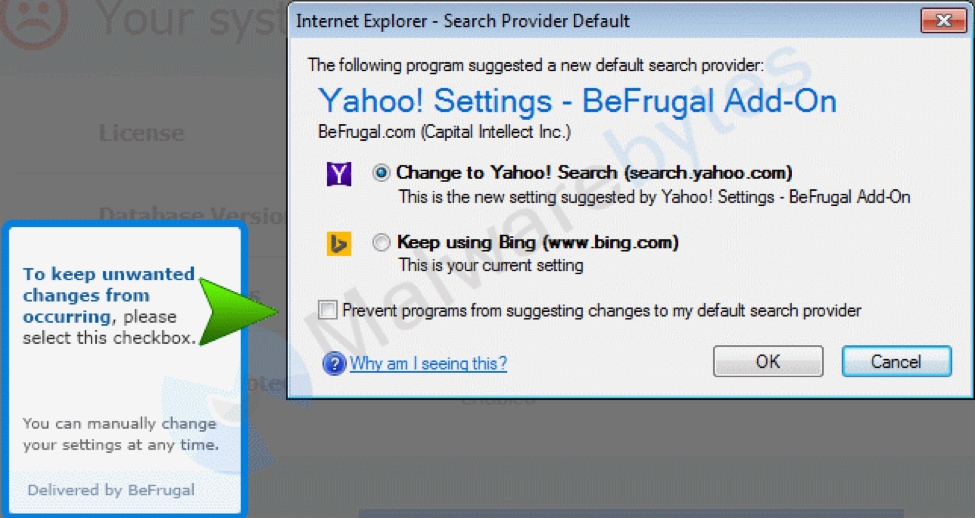
Incomplete or incorrect removal of browser extensions can lead to browser instability and crashes. In cases of hijackers, it may take some extra steps to change back startpage(s), default search engines, and even “new-tab-urls.”
Avoidance
Don’t get tempted to install software without a bit of research. Sometimes all it takes is a short look at the EULA or a quick search about the application to know it’s better to stay away from it. Avoid bundlers by downloading from the publishers’ sites whenever possible. Sometimes the price for free software is more than you would be willing to pay.
Example
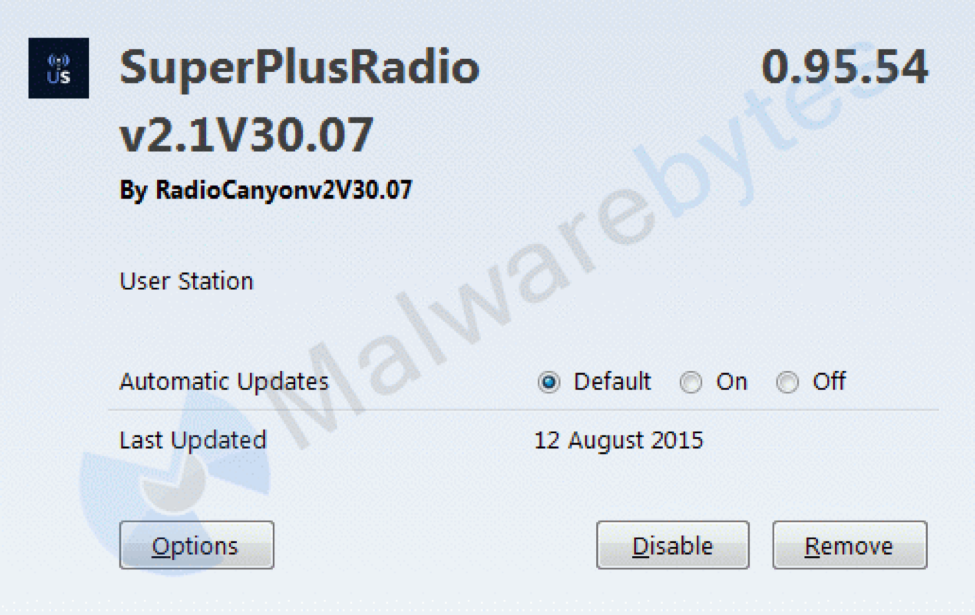
Internet Explorer is dealt three extensions. Two BHOs and a toolbar.
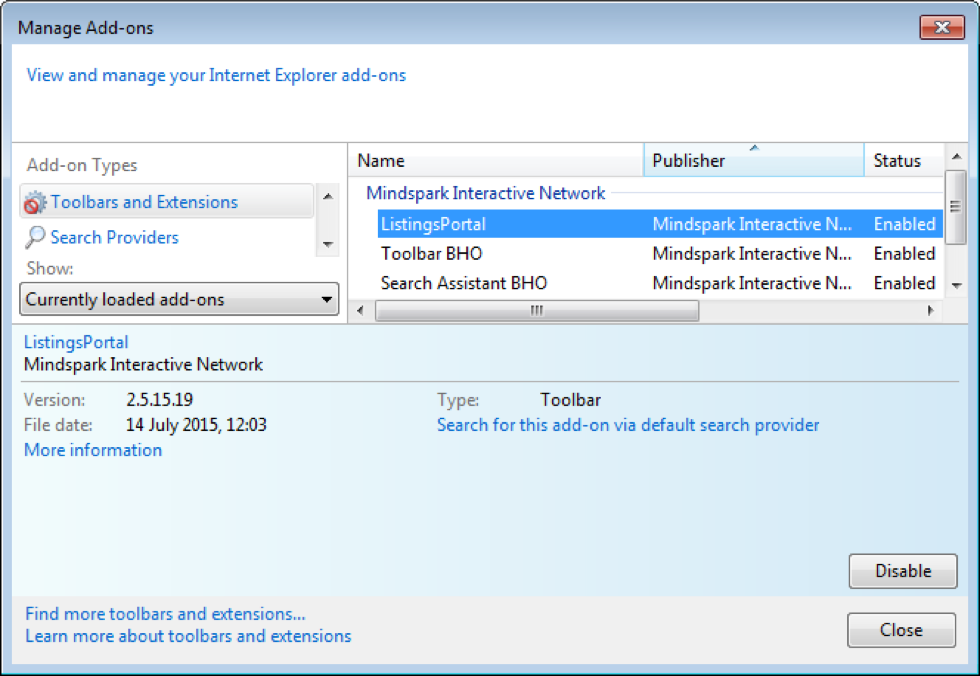
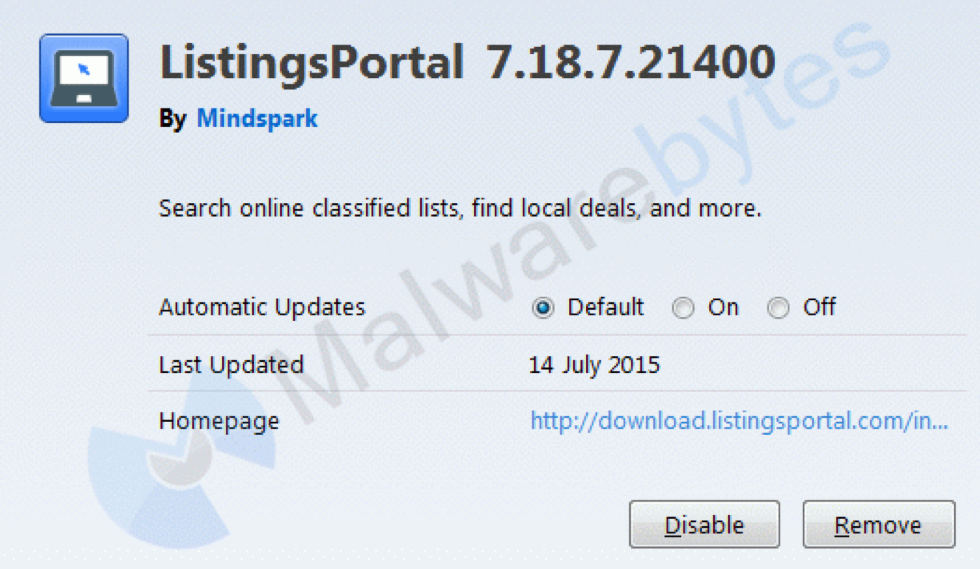
The toolbar pretty much looks the same in these three browsers.

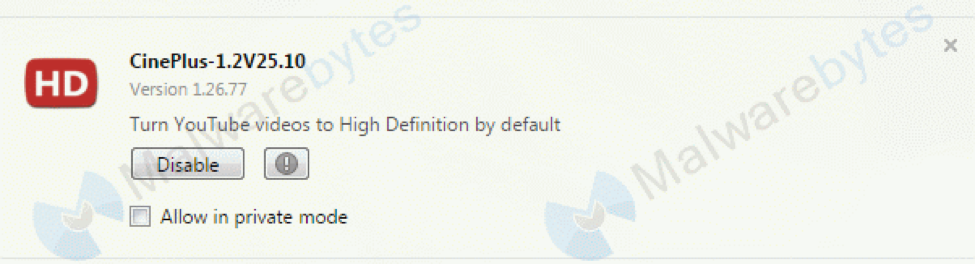
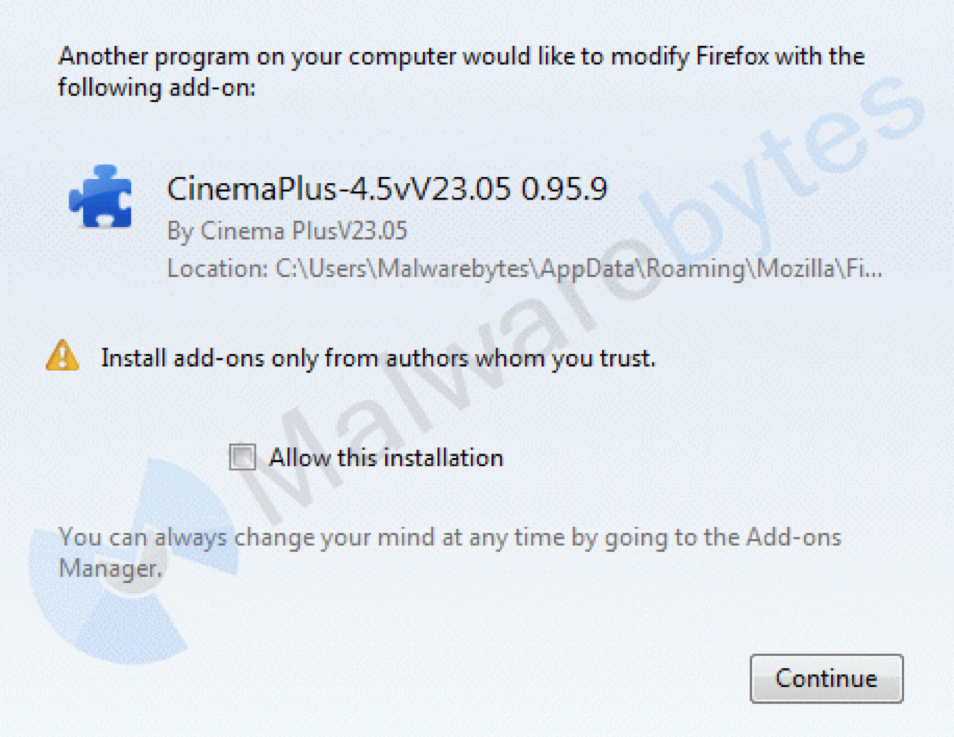
The Firefox extension looks like this:
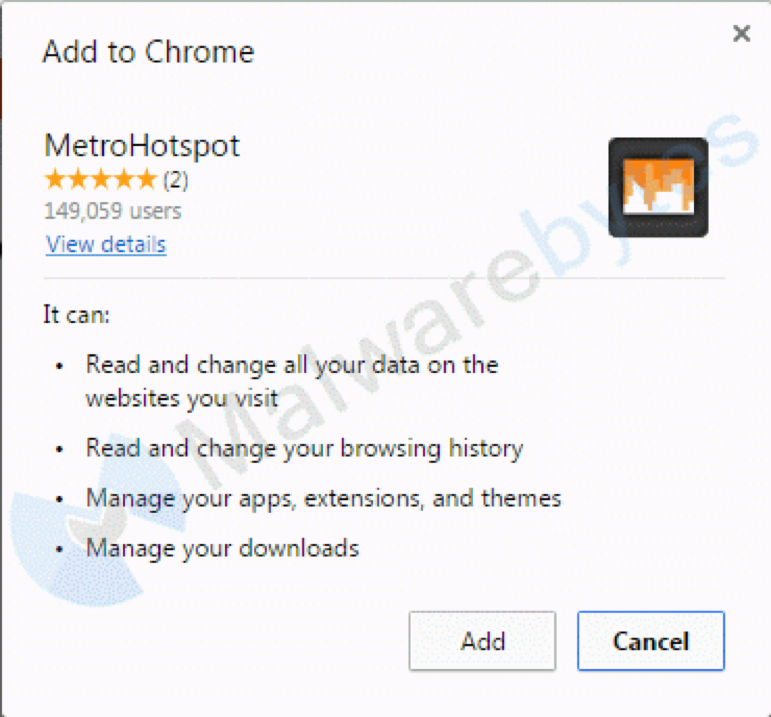
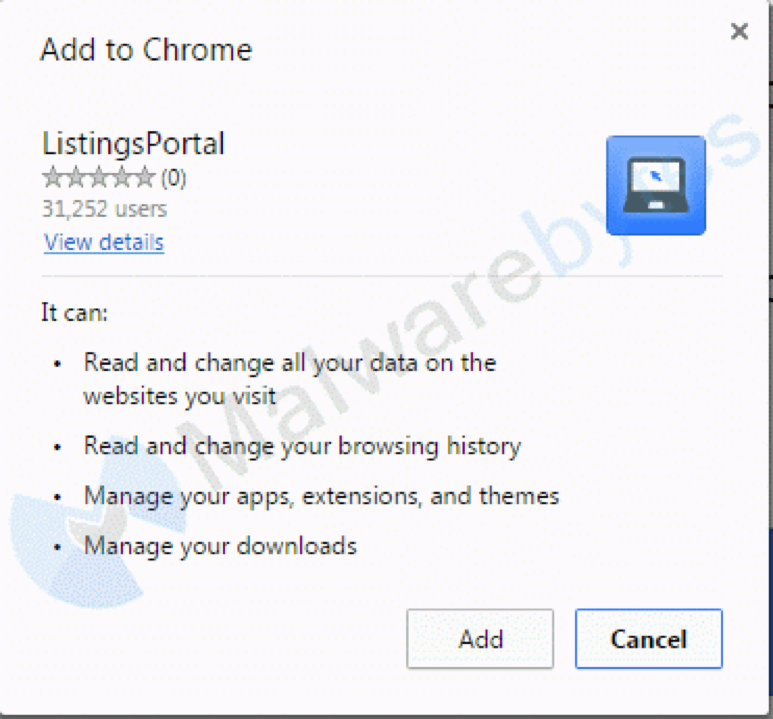
And this is the Chrome extension:
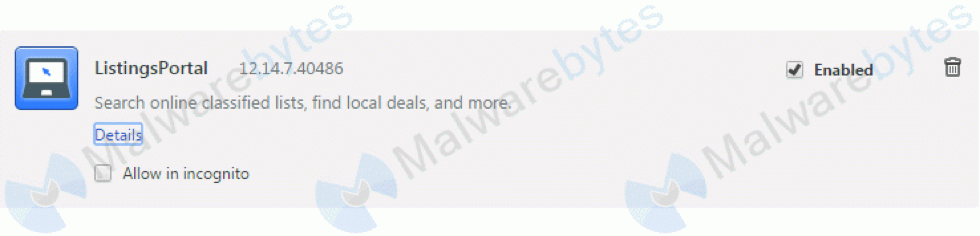
Looking at the details shows you the permissions for the extension.
Normally this PUP will only install the toolbar on your default browser, but we wanted to show you all the options.
Screenshots