[updated] Windows MSHTML zero-day actively exploited, mitigations required
Several researchers have independently reported a 0-day remote code execution vulnerability in MSHTML to Microsoft. The reason it was reported by several researchers probably lies in the fact that a limited number of attacks using this vulnerability have been identified, as per Microsoft’s security update.
Microsoft is aware of targeted attacks that attempt to exploit this vulnerability by using specially-crafted Microsoft Office documents.
MSHTML is a software component used to render web pages on Windows. Although it’s most commonly associated with Internet Explorer, it is also used in other software including versions of Skype, Microsoft Outlook, Visual Studio, and others.
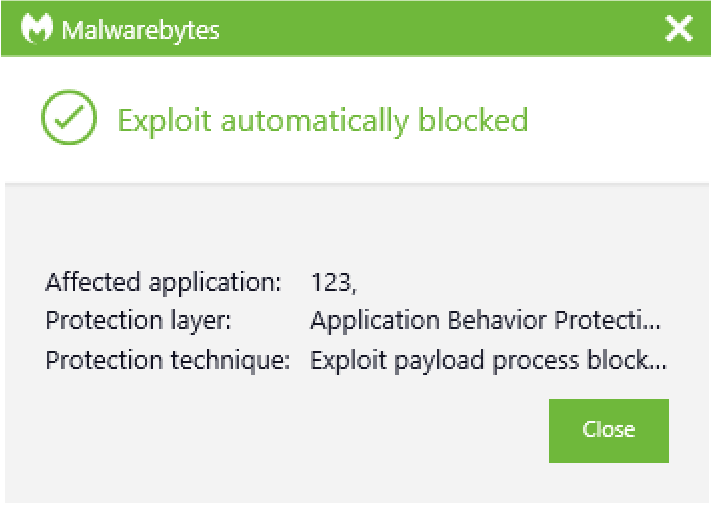
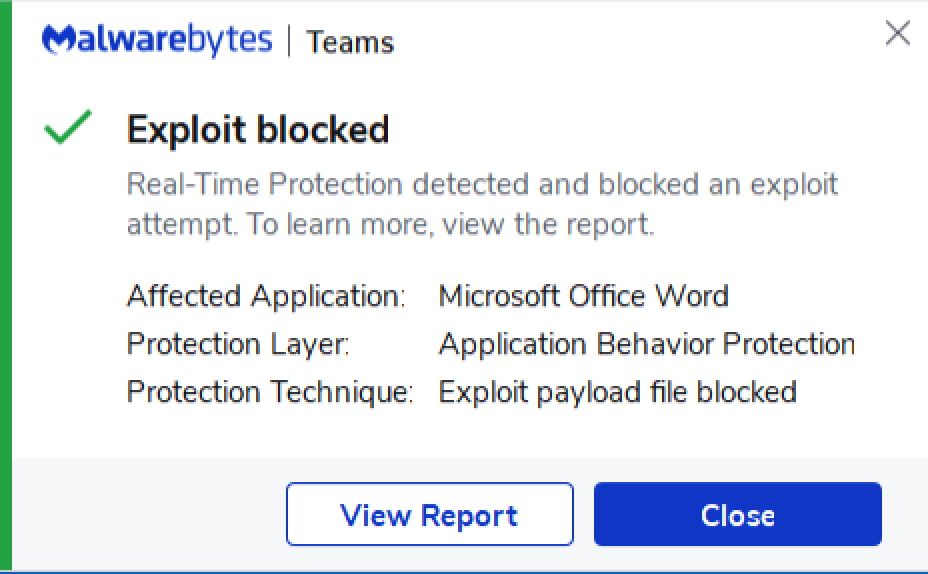
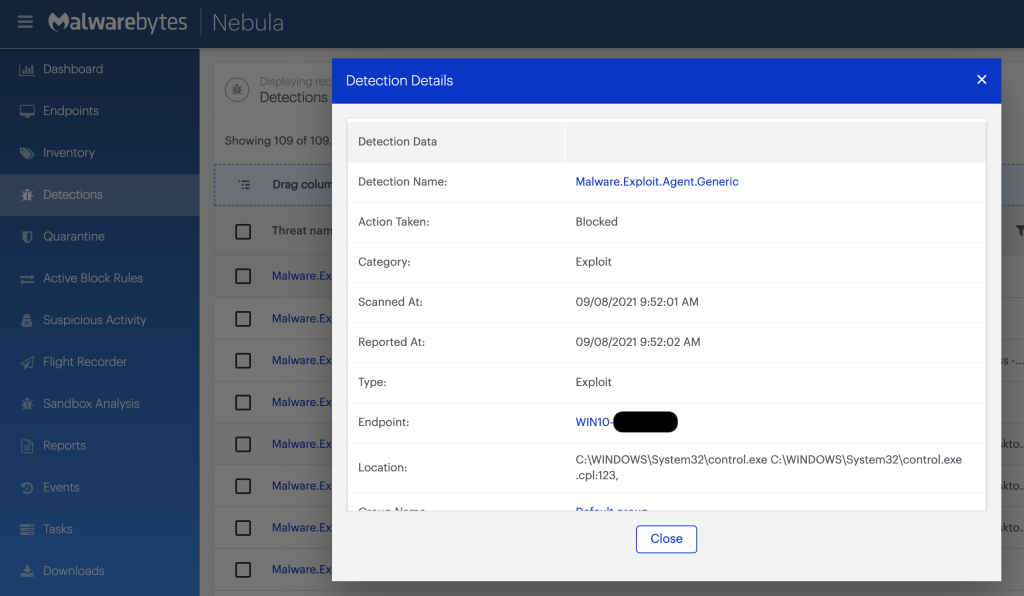
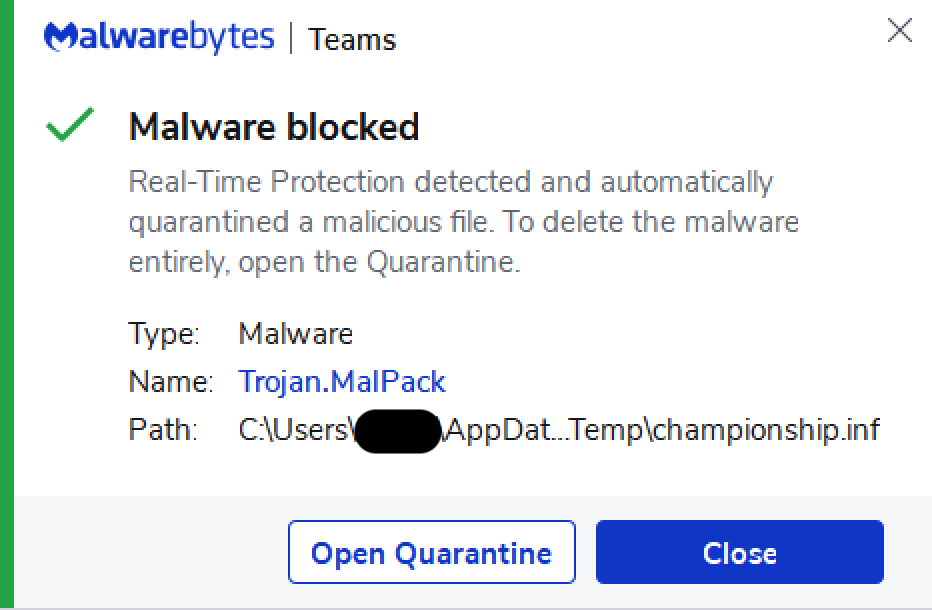
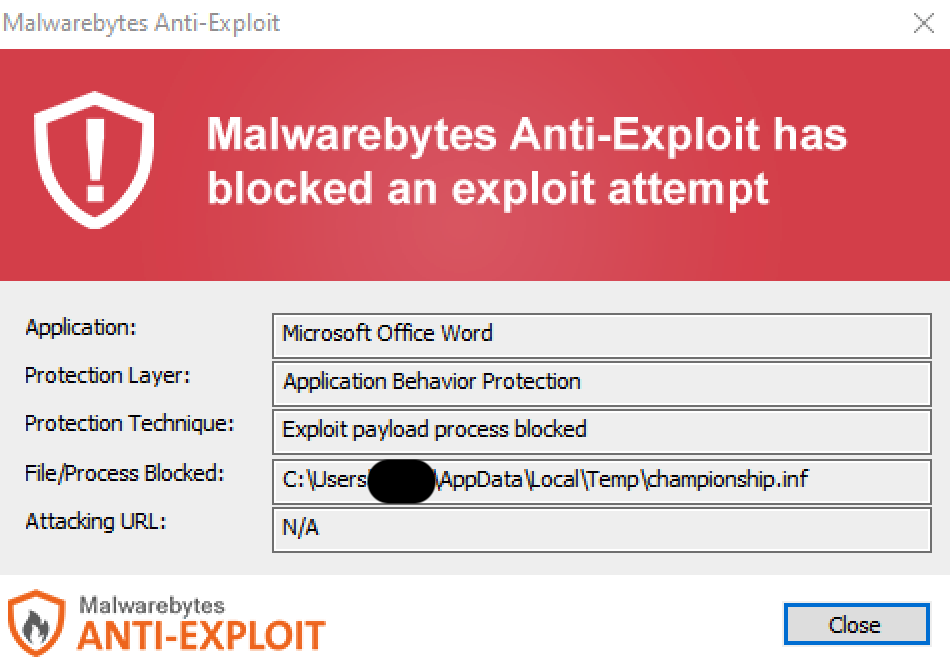
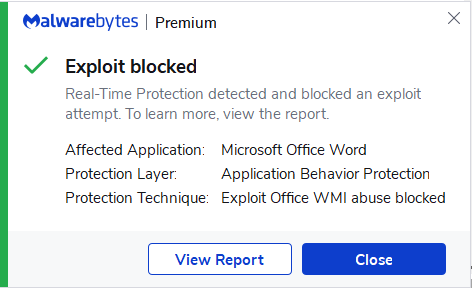
Malwarebytes, as shown lower in this article, blocks the related malicious powershell code execution.
CVE-2021-40444
Publicly disclosed computer security flaws are listed in the Common Vulnerabilities and Exposures (CVE) database. Its goal is to make it easier to share data across separate vulnerability capabilities (tools, databases, and services). This one has been assigned the designation CVE-2021-40444 and received a CVSS score of 8.8 out of 10. The CVSS standards are used to help security researchers, software users, and vulnerability tracking organizations measure and report on the severity of vulnerabilities. CVSS can also help security teams and developers prioritize threats and allocate resources effectively.
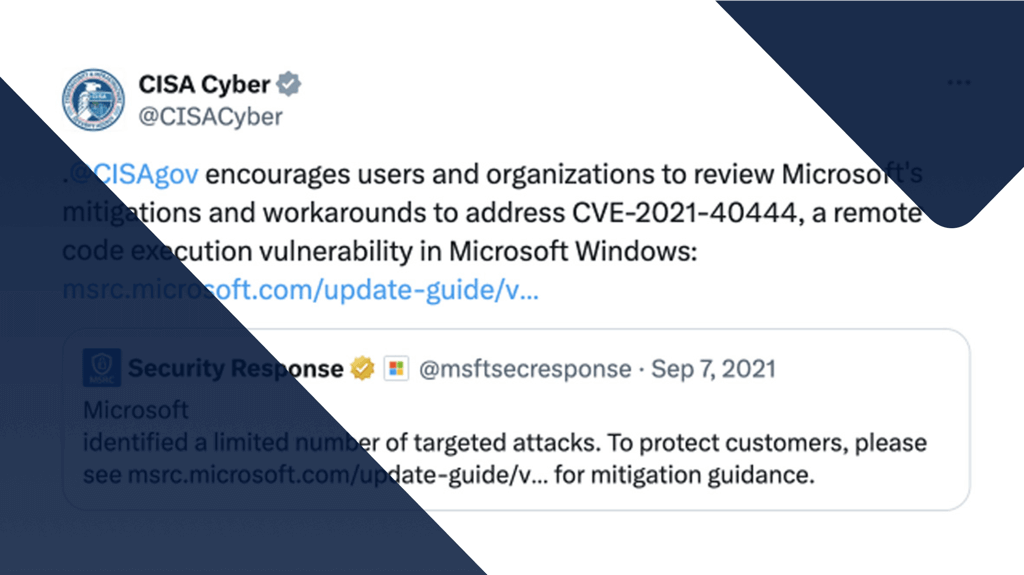
The Cybersecurity and Infrastructure Security Agency took to Twitter to encourage users and organizations to review Microsoft’s mitigations and workarounds to address CVE-2021-40444.
ActiveX
Because MSHTML is the beating heart of Internet Explorer, the vulnerability also exists in that browser. Although given its limited use, there is little risk of infection by that vector. Microsoft Office applications however, use the MSHTML component to display web content in Office documents.
The attack depends on MSHTML loading a specially crafted ActiveX control when the target opens a malicious Office document. The loaded ActiveX control can then run arbitrary code to infect the system with more malware.
So, the attacker will have to trick the user into opening a malicious document. But we all know how good some attackers are at this.
Mitigation
At the moment all supported Windows versions are vulnerable. Since there is no patch available yet, Microsoft proposes a few methods to block these attacks.
- Disable the installation of all ActiveX controls in Internet Explorer via the registry. Previously-installed ActiveX controls will still run, but no new ones will be added, including malicious ones.
- Open documents from the Internet in Protected View or Application Guard for Office, both of which prevent the current attack. This is a default setting but it may have been changed.
Despite the lack of a ready patch, all versions of Malwarebytes currently block this threat, as shown below. Malwarebytes also detects the eventual payload, Cobalt Strike, and has done so for years, meaning that even if a threat actor had disabled anti-exploit, then Cobalt Strike itself would still be detected.
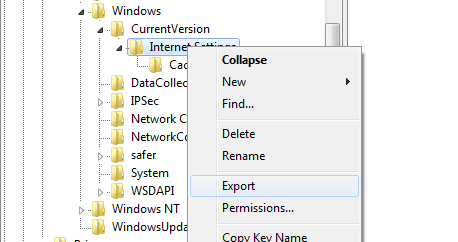
Registry changes
Modifying the registry may create unforeseen results, so create a backup before you change it! It may also come in handy when you want to undo the changes at a later point.
To create a backup, open Regedit and drill down to the key you want to back up (if it exists):
HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsCurrentVersionInternet SettingsZones
Right click the key in the left side of the registry pane and select “Export”. Follow the prompts and save the created reg file with a name and in a location where you can easily find it.
To make the recommended changes, open a text file and paste in the following script. Make sure that all of the code box content is pasted into the text file!
Windows Registry Editor Version 5.00[HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsCurrentVersionInternet SettingsZones] "1001"=dword:00000003 "1004"=dword:00000003[HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsCurrentVersionInternet SettingsZones1] "1001"=dword:00000003 "1004"=dword:00000003[HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsCurrentVersionInternet SettingsZones2] "1001"=dword:00000003 "1004"=dword:00000003[HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsCurrentVersionInternet SettingsZones3] "1001"=dword:00000003 "1004"=dword:00000003
Save the file with a .reg file extension. Right-click the file and select Merge. You’ll be prompted about adding the information to the registry, agree, and then reboot your machine.
Update september 9, 2021
It has taken researchers only a few days to circumvent the mitigations proposed by Microsoft. Once they were able to find a sample of a malicious Word document, they have started analyzing how it works and along the way poked holes in the defense strategies proposed by Microsoft.
One of the wobbly pillars is the Mark-of-the-Web (MoTW) flag that is given to downloaded files. This only blocks the exploit unless a user clicks on the ‘Enable Editing’ buttons. Sadly, experience has learned us that it is not a good idea to trust that they won’t do that. Another problem with this flag is that it doesn’t survive when it is handled by other applications, like for example, unzipping. Another problem are certain filetypes that use the same MSHTML to view webcontent, but are not protected by Office’s Protected View security feature. Researcher Will Dormann was able to replicate the attasck using an RTF file.
The registry fix we posted to prevent ActiveX controls from running in Internet Explorer, were supposed to effectively block the current attacks. But, security researcher Kevin Beaumont has already discovered a way to bypass Microsoft’s current mitigations to exploit this vulnerability.
The attack chain
The researchers have also managed to reconstruct the attack chain with the use of a limited set of samples of malicious docx files.
- Once a user clicks on the ‘Enable Editing’ button, the exploit will load a side.html file by using the mhtml protocol to open a URL. The side.html file is hosted at a remote site and will be loaded as a Word template.
- The Internet Explorer browser will be started to load the HTML, and its obfuscated JavaScript code will exploit the CVE-2021-40444 vulnerability to create a malicious ActiveX control.
- This ActiveX control will download a ministry.cab file from a remote site.
- And extract a championship.inf file, which is actually a DLL, and execute it as a CPL file by using rundll32.exe.
- The ultimate payload is a Cobalt Strike beacon, which would allow the threat actor to gain remote access to the device.
Given the few days that are left until next patch Tuesday, it is doubtful whether Microsoft will be able to come up with an effective patch.
Consider me one happy camper that Malwarebytes does not rely on the MoTW flag.
Update september 13, 2021
As reported by BleepingComputer threat actors are sharing PoCs, tutorials and exploits on hacking forums, so that every script kiddy and wannabe hacker can follow step-by-step instructions to build their own attacks. Since the method we mentioned that uses an RTF file even works in Windows explorer file previews. This means this vulnerability can be exploited by viewing a malicious document using the Windows Explorer preview feature.
Since this was discovered, Microsoft has added the following mitigation to disable previewing of RTF and Word documents:
- In the Registry Editor (regedit.exe), navigate to the appropriate registry key: For Word documents, navigate to these keys:
- HKEY_CLASSES_ROOT.docxShellEx{8895b1c6-b41f-4c1c-a562-0d564250836f}
- HKEY_CLASSES_ROOT.docShellEx{8895b1c6-b41f-4c1c-a562-0d564250836f}
- HKEY_CLASSES_ROOT.docmShellEx{8895b1c6-b41f-4c1c-a562-0d564250836f} For rich text files (RTF), navigate to this key:
- HKEY_CLASSES_ROOT.rtfShellEx{8895b1c6-b41f-4c1c-a562-0d564250836f}
- Export a copy of the Registry key as a backup.
- Now double-click Name and in the Edit String dialog box, delete the Value Data.
- Click OK,
Word document and RTF file previews are now disabled in Windows Explorer.
To enable Windows Explorer preview for these documents, double-click on the backup .reg file you created in step 2 above.
Stay safe,everyone!